Static routes are manually configured paths in a router’s routing table, offering precise control over traffic flow. Unlike dynamic routing protocols like EIGRP or OSPF, static routes are ideal for small networks or backup scenarios. Floating static routes enhance this by serving as a backup path with a higher administrative distance (AD), activating only when the primary route fails due to link issues or misconfigurations.
For CCNA and CCNP students, mastering floating static routes is essential for certification exams and real-world network resilience. This article explores their configuration, verification, and practical application using a sample topology with Router3, Router1, and Router2.
The network administrators use floating static routes to provide a backup path to a primary static or dynamic route in case of a link failure. The floating static route works only when the primary route is not available. The primary route may fail due to physical layer problems, a wrong configuration, or many other reasons. The router will choose the path with the lowest administrative distance if multiple routes are available to the destination. If multiple paths exist to the destination, the router will choose the route with the lowest administrative distance value.
The default administrative distance of EIGRP is 90, so if we want to configure the floating static route for EIGRP routes, it must be configured with an administrative value higher than 90. If the floating static route is configured with a lower value than 90, the router will use that static route first.
Topology and Configuration of Floating Static Routes
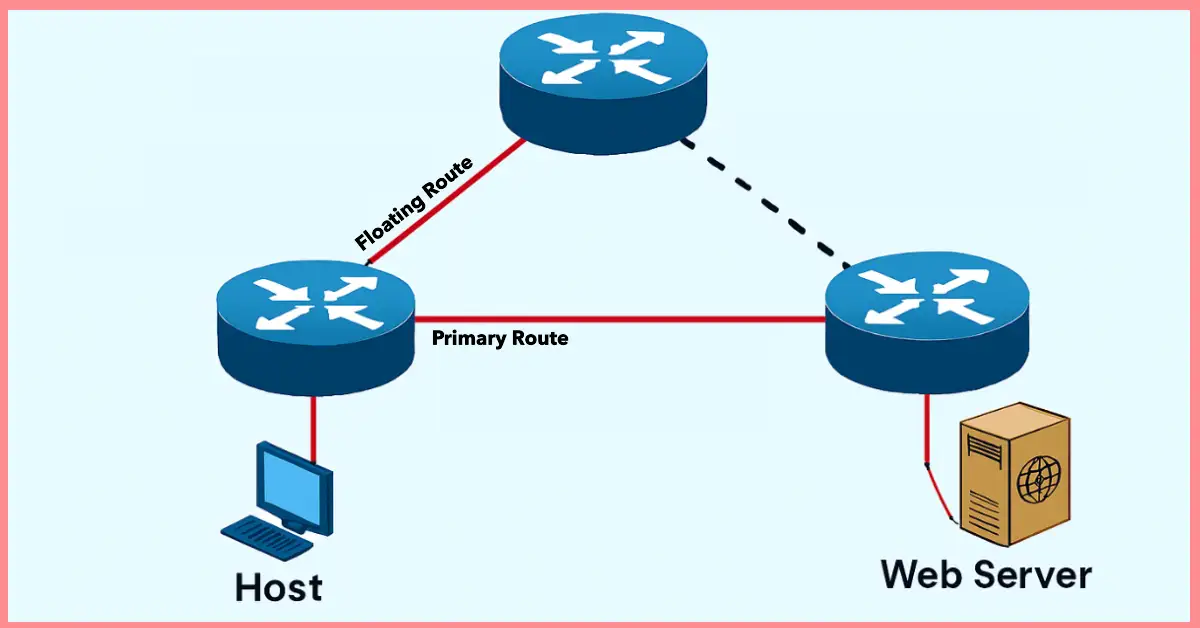
In the topology, a host connects to a web server via Router3, which has two paths: a primary route through Router1 and a backup (floating) route through Router2. Router3 is configured with a default static route to Router1 via FastEthernet 0/0 with the default AD of 1. The floating static route to Router2 is configured with an AD of 3 to ensure it activates only if the primary route fails.
Corrected Configuration Commands
Router3>enable
Router3#configure terminal
Router3(config)#ip route 0.0.0.0 0.0.0.0 FastEthernet0/0 1 ! Primary route to Router1
Router3(config)#ip route 0.0.0.0 0.0.0.0 FastEthernet0/1 3 ! Floating route to Router2
Router3(config)#exit
Router3#write memory
This ensures the floating route (AD 3) remains inactive unless the primary route (AD 1) fails.
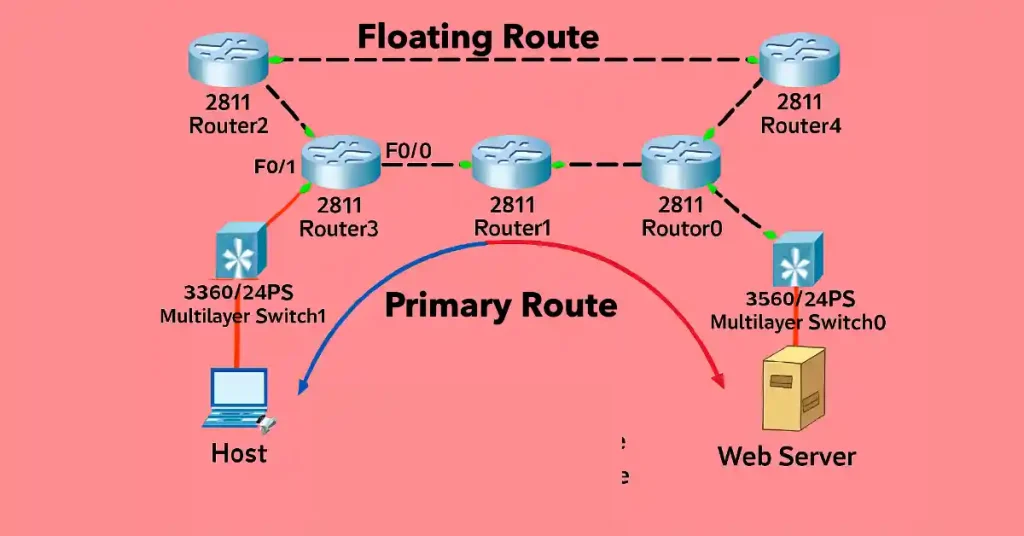
In the figure above, the host has two paths to reach a web server. Router3 has two default static routes configured, one with the default value of administrative distance and the other with an administrative distance of 3. Router3 typically sends data to the web server via Router1 because the static route pointing to Router1 is configured with the default AD value (1). The route pointing to Router2 is configured with an AD value of 3, so this is the static floating route.
When there is a problem in the first path, the router should automatically delete the first route from the routing table and add the floating static route in the routing table. So, the traffic will flow to the web server via the floating route.
Administrative Distance Values
The administrative distance (AD) indicates a route’s trustworthiness, with lower values preferred. Common protocols include:
- Static – 1
- EIGRP = 90
- IGRP = 100
- OSPF = 110
- IS-IS = 115
- RIP = 120
For a floating static route to work with EIGRP (AD 90), configure it with an AD higher than 90 (e.g., 95).
Verifying Floating Static Routes
To verify the configuration, use the following commands on Router3:
Router3#show ip route
Expected Output (Primary Route Active):
Gateway of last resort is 0.0.0.0 to network 0.0.0.0
S* 0.0.0.0/0 [1/0] via FastEthernet0/0
The floating route (AD 3) is absent as the primary route is active.
To test the floating route, disconnect the cable between Router3 and Router1:
Router3#show ip route
Expected Output (Floating Route Active):
Gateway of last resort is 0.0.0.0 to network 0.0.0.01
S* 0.0.0.0/0 [3/0] via FastEthernet0/
Use traceroute to confirm the path:Router3#traceroute 192.168.1.1
This will show the path shifting to Router2 after the primary link failure.
Troubleshooting Floating Static Routes
- Floating Route Not Activating: If the backup route doesn’t appear, check the AD value. Ensure it’s higher than the primary route (e.g., AD 3 > AD 1). Use
show ip routeto verify. - Primary Route Persisting: A misconfiguration or physical link issue might prevent route removal. Test with
shutdownon the primary interface and checkshow ip route. - Incorrect Interface: Verify the interface (e.g., FastEthernet 0/1) matches the topology. Use
show running-config | section ip routeto confirm.
Resolve issues by adjusting AD values or correcting interface assignments.
FAQs
What is a floating static route, and how does it work?
A floating static route is a backup route configured with a higher administrative distance (AD) than the primary route, ensuring it activates only when the primary fails. For example, in the Router3 topology, a primary route to Router1 (AD 1) and a floating route to Router2 (AD 3) are set. If the link to Router1 fails due to a cable issue or misconfiguration, Router3 removes the primary route and adds the floating route to the routing table, redirecting traffic.
How do I configure a floating static route on a Cisco router?
To configure a floating static route, access global configuration mode on a Cisco router like Router3. First, set the primary route with a lower AD, e.g., ip route 0.0.0.0 0.0.0.0 FastEthernet0/0 1 for Router1. Then, add the floating route with a higher AD, e.g., ip route 0.0.0.0 0.0.0.0 FastEthernet0/1 3 for Router2. The higher AD (3) ensures it remains inactive unless the primary fails. Save with write memory and verify with show ip route. This hands-on skill is vital for CCNA/CCNP exams and network reliability.
What administrative distance should I use for a floating static route?
The administrative distance (AD) for a floating static route must exceed the primary route’s AD. For static routes, the default AD is 1, so a floating route needs an AD of 2 or higher (e.g., 3, as in the Router3 example). If backing up an EIGRP route (AD 90), set the floating route’s AD above 90, such as 95. This ensures the router prioritizes the primary route until it fails. CCNA/CCNP students should test this show ip route after configuration to confirm the floating route’s standby status, a key concept for routing exams.
How can I verify if a floating static route is working?
To verify a floating static route, use show ip route on Router3 to check the active route. Initially, with the primary route to Router1 (AD 1) up, only that appears (e.g., S* 0.0.0.0/0 [1/0] via FastEthernet0/0). Disconnect the Router1 link, then re-run the command; the floating route to Router2 (AD 3) should appear (e.g., S* 0.0.0.0/0 [3/0] via FastEthernet0/1). Additionally, use traceroute to trace the path shift. This verification process is essential for CCNA/CCNP students to master routing table dynamics.
What should I do if my floating static route doesn’t activate?
If a floating static route fails to activate, first check the AD values show ip route to ensure the floating route’s AD (e.g., 3) is higher than the primary’s (e.g., 1). Verify the interface (e.g., FastEthernet 0/1) with show running-config | section ip route. A physical link issue or misconfiguration might prevent the primary route from failing; test by shutting down the primary interface. For CCNA/CCNP students, troubleshooting with these commands ensures network uptime, a critical skill for certification and professional practice.