An Access Control List (ACL) is a critical feature in Cisco networking, used for security and traffic management. It consists of a set of rules designed to filter network traffic by specifying which users or systems are granted access to network resources and what operations they can perform. ACLs are commonly configured on devices with packet filtering capabilities, such as routers and firewalls, running Cisco IOS or IOS XE.
An ACL contains conditions and criteria that determine whether to allow or deny network traffic. These rules can be applied on a per-interface basis, affecting packets entering or leaving an interface. In Cisco environments, ACLs are a cornerstone of the IOS software, enabling administrators to enforce policies that enhance network efficiency, security, and control. Named ACLs, supported since IOS 12.0 and emphasized in IOS XE 16+ for better manageability, allow alphanumeric names for intuitive configuration, reducing errors in complex deployments.
By default, Cisco routers do not apply ACLs, routing traffic solely based on the routing table. Once an ACL is configured and applied to an interface, the router inspects each packet against the ACL rules to decide whether to forward or drop it. ACLs also support traffic classification for priority processing or restricting specific traffic types. Administrators must plan ACL entries carefully, as hardware limitations (e.g., a maximum of 18 ACLs on some Cisco switches) may apply, requiring efficient rule design.
ACLs extract key information from packet headers and compare it against predefined rules, including Layer 3 details (source/destination IP addresses, ICMP message types) and Layer 4 information (TCP/UDP ports). Rules are processed sequentially, with the first matching rule determining the packet’s fate—permit or deny. Best practices include placing specific rules before general ones to optimize performance and using logging options (e.g., the log keyword in ACEs) to track matches for troubleshooting.
Key Tasks and Benefits
ACLs perform several essential functions in a network, contributing to performance, security, and management:
Enhancing Network Performance
ACLs improve network efficiency by reducing unnecessary load. For example, if an organization prohibits video streaming to conserve bandwidth, an ACL can block such traffic, allowing critical applications to perform better.
Providing Traffic Flow Control
Its regulate routing update propagation. By limiting unnecessary updates across specific segments, ACLs preserve bandwidth and optimize resource utilization.
Ensuring Network Security
It provide a foundational layer of security by selectively allowing or denying access to network segments. For instance, an ACL can permit a trusted server to access sensitive data while blocking unauthorized devices, serving as a first line of defense.
Filtering Network Traffic
ACLs offer granular control over traffic based on attributes like protocol or port. They can permit email traffic (SMTP) while blocking Telnet or restrict access to services like FTP or HTTP, ensuring only approved traffic flows.
ACLs are versatile, enabling both filtering and classification for advanced traffic processing, making them indispensable for balanced and secure networks. In modern IOS XE deployments (e.g., version 16+), enhanced management tools simplify ACL editing and integrate with network management platforms, improving scalability in SD-WAN and cloud-integrated environments.
Packet Filtering
Packet filtering, or static filtering, is the core mechanism of ACLs, controlling incoming and outgoing packets based on criteria such as source/destination IP addresses, protocols, and ports.
The router, acting as a packet filter, examines packet headers during transmission, reception, forwarding, or denial, extracting information and applying rules to determine whether a packet passes or is discarded. Filtering operates at:
- Network Layer (OSI) / Internet Layer (TCP/IP): IP addresses and protocols.
- Transport Layer: TCP/UDP source and destination ports.
ACLs consist of Access Control Entries (ACEs), also called ACL statements, which are permit or deny rules based on criteria like source/destination addresses, protocols, and ports. When a packet arrives at an ACL-configured interface, the router compares it against each ACE in order. A match triggers the corresponding action (permit/deny), halting further processing. An implicit deny at the end of the list drops unmatched packets. Proper binding to interfaces (inbound/outbound) is critical to avoid misconfigurations.
Key information extracted includes:
| Layer | Information Extracted |
| Layer 3 | – Source IP address- Destination IP address- ICMP message type |
| Layer 4 | – TCP/UDP source port- TCP/UDP destination port |
This sequential approach ensures precise control over network or subnet access, blocking unauthorized traffic while allowing legitimate flows.
Types of IPv4 ACLs in Cisco Routers
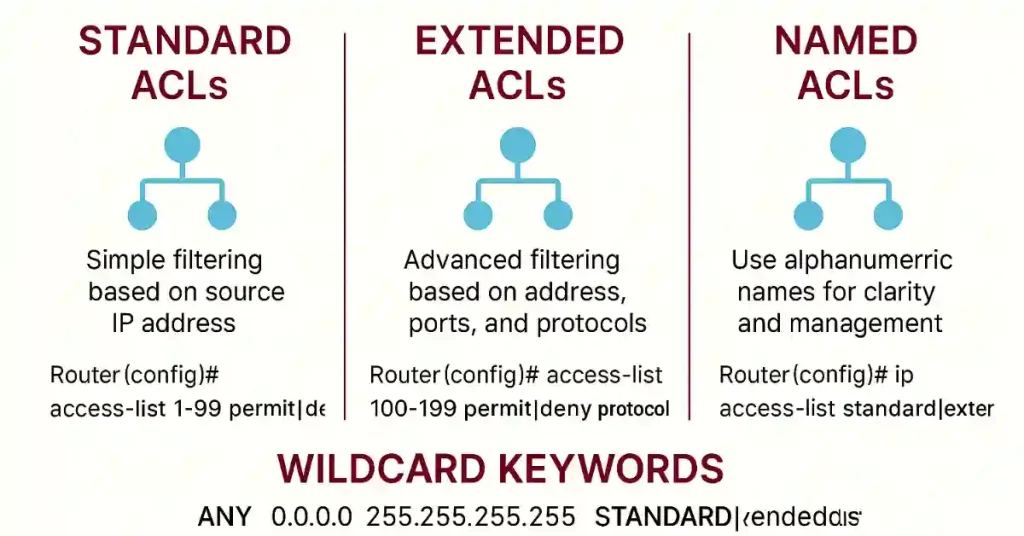
Cisco supports ACLs for various protocols (IPv4, IPv6, IPX, DECnet, AppleTalk). For IPv4, there are two primary types: Standard ACLs and Extended ACLs, with named ACLs offering a modern alternative for both.
Standard Access Lists
Standard ACLs filter traffic based solely on the source IP address, making them suitable for server-based filtering or distinguishing routes without considering destinations or ports. Their configuration syntax is:
Router(config)# access-list {1-99} {permit | deny} source-addr [source-wildcard]
- Number Range (1-99): Identifies a standard ACL.
- Permit/Deny: Specifies whether to allow or block matching traffic.
- Source-addr: The source IP address.
- Source-wildcard: A mask for the address range (see wildcard section).
Standard ACLs are simple but limited, as they do not evaluate destinations or ports.
Extended Access Lists
Extended ACLs offer advanced filtering based on source/destination IP addresses, protocol types (e.g., IP, TCP, UDP), ports, and other features, ideal for packet-based filtering across networks. Their syntax is:
Router(config)# access-list {100-199 | 2000-2699} {permit | deny} protocol source-addr [source-wildcard] [operator operand] destination-addr [destination-wildcard] [operator operand] [established]
- Number Range (100-199 or 2000-2699): Marks an extended ACL.
- Permit/Deny: Defines the action.
- Protocol: Specifies the IP sub-protocol (e.g., TCP, UDP).
- Source/Destination and Wildcards: Define traffic source and destination.
- Operator/Operand: Specifies port conditions (e.g., eq for equal, gt for greater than).
- Established: Optional for TCP, allowing established connections.
Ports must follow destination configurations to avoid dropping all traffic to that destination.
Named ACLs
Named ACLs, supported since IOS 12.0 and emphasized in IOS XE 16+, use alphanumeric names for better readability and maintenance. They can be standard or extended:
Router(config)# ip access-list {standard | extended} name
Router(config-std-nacl)# {permit | deny} source-addr [source-wildcard]
Router(config-ext-nacl)# {permit | deny} protocol source-addr [source-wildcard] destination-addr [destination-wildcard] ...
Both ACL types use permit/deny statements to control packet entry, with named ACLs improving manageability in large deployments.
ACL Operations: Inbound and Outbound
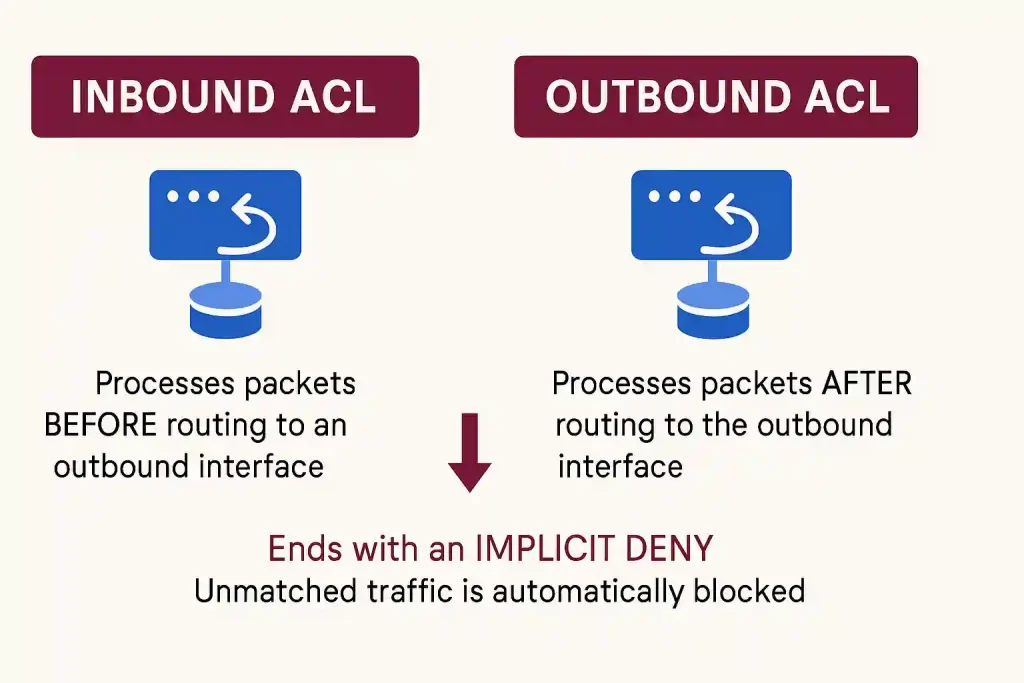
ACL operations apply rules to traffic direction—either inbound or outbound—without affecting packets originating from the router itself.
Inbound ACL
Inbound ACL process packets before routing to an outbound interface, discarding non-matching packets early to reduce routing lookups. If permitted, the packet is routed; if denied, it’s dropped. They are ideal for single-source inbound interfaces.
Outbound ACL
Outbound ACL process packets after routing to the outbound interface, applying filters before exit. They are best for traffic from multiple inbound interfaces requiring uniform filtering at a common outbound interface.
Both types end with an implicit deny, automatically blocking unmatched traffic, ensuring comprehensive filtering. Proper interface binding and rule ordering are critical best practices to avoid performance issues or misconfigurations.
| ACL Type | Processing Point | Efficiency Advantage | Best Use Case |
| Inbound | Before routing | Reduces routing load | Single inbound source |
| Outbound | After routing, before exit | Uniform filtering | Common outbound interface |
Wildcard Masking in ACLs
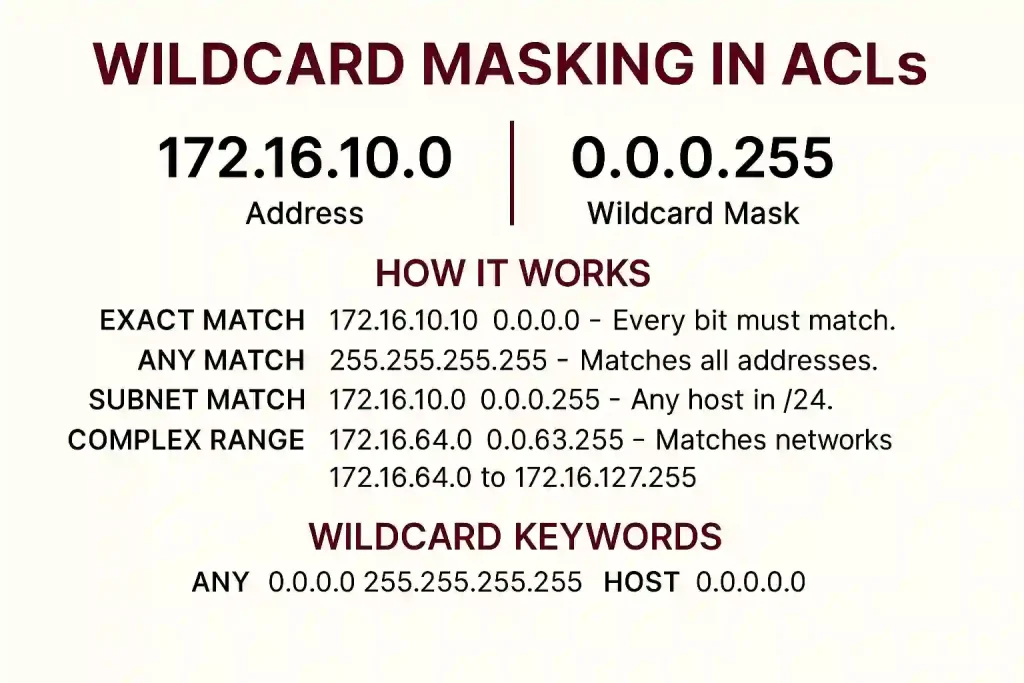
Wildcard masking uses a 32-bit string to specify which address bits to match or ignore, used in routing protocols like OSPF or IPv6 ACLs (via prefix lengths). Unlike subnet masks (1s for network, 0s for host), wildcard masks reverse this:
- Bit 0: Must match the address bit.
- Bit 1: Ignores the address bit.
Wildcard masks are typically the inverse of subnet masks, calculated by subtracting the subnet mask from 255.255.255.255.
Wildcard Mask Calculation Examples
Example 1: Network 172.16.0.0/24 (subnet mask 255.255.255.0), permitting all hosts:
- Subtract: 255.255.255.255 – 255.255.255.0 = 0.0.0.255
- Matches the entire /24 subnet.
Example 2: Network 172.16.1.0/27 (subnet mask 255.255.255.224), permitting 32 users:
- Subtract: 255.255.255.255 – 255.255.255.224 = 0.0.0.31
- Covers 172.16.1.0 to 172.16.1.31.
Example 3: Network 172.16.4.0/22 (subnet mask 255.255.252.0):
- Subtract: 255.255.255.255 – 255.255.252.0 = 0.0.3.255
- Matches a larger range.
How Wildcard Masking Works
- Exact Match (0.0.0.0): 172.16.10.10 0.0.0.0 – Every bit must match.
- Any Match (255.255.255.255): Matches all addresses.
- Subnet Match (0.0.0.255): 172.16.10.0 0.0.0.255 – Any host in /24.
- Complex Range (0.0.63.255): 172.16.64.0 0.0.63.255 – Matches networks 172.16.64.0 to 172.16.127.255.
Wildcard Keywords
- Any: Substitutes 0.0.0.0 255.255.255.255 (e.g., access-list 10 permit any).
- Host: Substitutes a single address with 0.0.0.0 (e.g., access-list 10 permit host 172.16.10.100).
These keywords simplify configurations for broad or specific matches.
How to Create an ACLs
Creating and configuring Access Control Lists (ACLs) is not an easy task, as it often requires multiple policies and ongoing management. For example, consider a router with two interfaces, each configured for both IPv4 and IPv6. To filter traffic for both protocols in both directions (inbound and outbound), each interface would require up to four ACLs: one for IPv4 inbound, one for IPv4 outbound, one for IPv6 inbound, and one for IPv6 outbound. This totals eight separate ACLs across both interfaces.
However, ACLs do not always need to be configured for both directions. The number and direction of ACLs depend on your network’s security requirements.
ACL Requirements Table
| Interface | Protocol | Direction | ACL Type |
|---|---|---|---|
| Interface 1 | IPv4 | Inbound | Standard/Extended |
| Interface 1 | IPv4 | Outbound | Standard/Extended |
| Interface 1 | IPv6 | Inbound | IPv6 ACL |
| Interface 1 | IPv6 | Outbound | IPv6 ACL |
| Interface 2 | IPv4 | Inbound | Standard/Extended |
| Interface 2 | IPv4 | Outbound | Standard/Extended |
| Interface 2 | IPv6 | Inbound | IPv6 ACL |
| Interface 2 | IPv6 | Outbound | IPv6 ACL |
This table illustrates the “Three P’s” principle early, aiding CCNA students in visualization.
General Guidelines for Using ACLs
General guidelines for using ACLs include:
- Place ACLs on routers between internal and external networks, such as firewall routers.
- Use ACLs on routers between network segments to control traffic flow.
- Apply ACLs on border routers at network edges.
- Configure ACLs for all protocols (e.g., IPv4, IPv6, IPX if legacy) on border interfaces.
For CCNP students: In modern networks, prioritize IPv6 ACLs (using ipv6 access-list) as dual-stack environments grow. Avoid over-filtering to prevent performance issues on high-throughput interfaces.
The Three P’s in ACL Guidelines
The three P’s are important in ACL guidelines. We can configure one ACL Per protocol, Per direction, Per interface:
- One ACL per protocol – To control traffic flow on an interface an ACL must be defined for each protocol enabled on the interface, for example, IP, IPX, AppleTalk.
- One ACL per direction– ACLs can control traffic only in one direction at a time on an interface. So, two separate ACLs must be configured to control inbound and outbound traffic.
- One ACL per interface– ACLs control traffic for an interface, for example, GigabitEthernet 0/0 or FastEthernet 0/1.
For instance, on a GigabitEthernet0/0 interface running IPv4 and IPv6:
- Per Protocol: Separate ACLs for IPv4 (access-list 10 …) and IPv6 (ipv6 access-list ACLv6 …).
- Per Direction: Apply inbound with ip access-group 10 in and outbound with ip access-group 20 out.
- Per Interface: Configure uniquely for each interface to avoid conflicts.
Differences and Placement of Standard vs. Extended ACLs
As the name suggests, standard access lists are basic filters that allow or deny traffic based on source IP addresses. On the other hand, extended access lists offer more advanced features, allowing you to filter traffic based on source and destination IP addresses and other parameters such as protocols and port numbers.
By delving into the intricacies of these access lists, you’ll understand how each works and how to implement them effectively in your network infrastructure. Whether you’re an IT professional or a networking enthusiast, this article will provide you with the knowledge you need to enhance your network security.
Standard ACLs Placement
As the name suggests, standard access lists are basic filters that allow or deny traffic based on source IP addresses. When configuring a standard access list, you can specify a range of source IP addresses you want to permit or deny access to certain network resources. The main advantage of using standard access lists is their simplicity and ease of implementation.
Unlike extended access lists, standard access lists do not consider the destination IP address, protocols, or port numbers, which limits their filtering capabilities. Standard access lists are generally used for simple filtering tasks, such as blocking specific IP addresses or allowing access from a specific range of IP addresses.
To create a standard access list, you must assign a number, typically 1 to 99 or 1300 to 1999. The lower the number, the higher the priority of the access list. Each access list entry consists of a permit or deny statement followed by the source IP address or a wildcard mask. The wildcard mask specifies the range of IP addresses you want to permit or deny.
We know that standard ACLs only filter traffic based on a source address. The basic rule of standard ACLs requires placement that is possibly close to the destination network. This allows the traffic to arrive at all other networks except those where the packets will be filtered. In the figure below, we want to prevent traffic from the 192.168.2.0/24 network from reaching the 192.168.4.0/24 network.
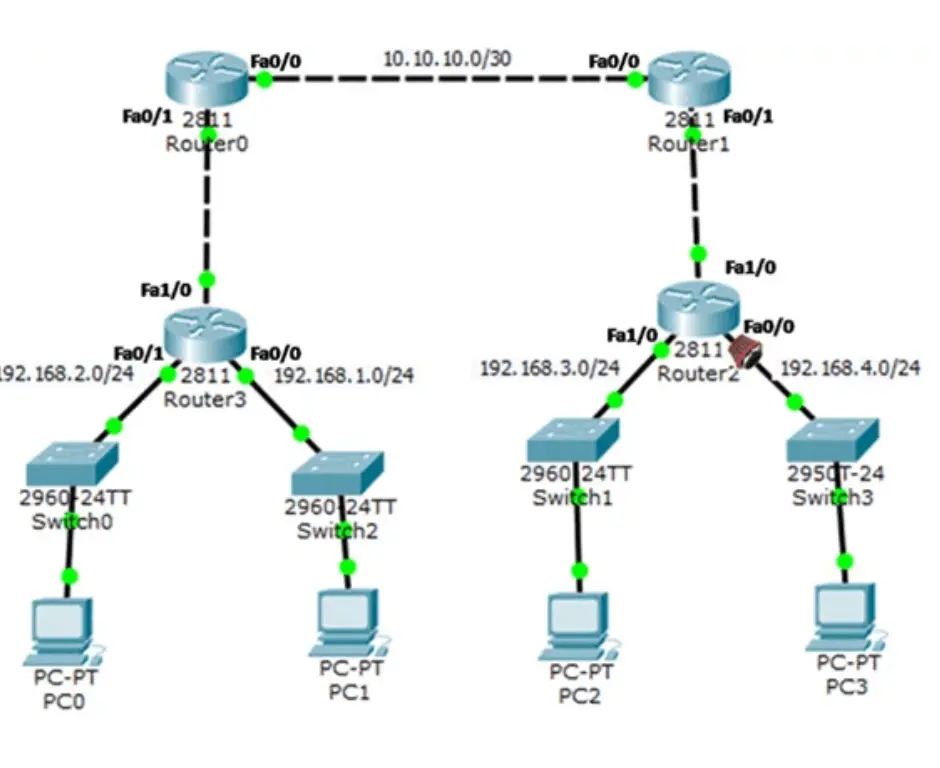
If we place the standard ACL on the inbound interface of Router0, this will stop the 192.168.2.0/24 network traffic from reaching any other network. If we place ACL on the outbound interface towards Router1, this will stop 192.168.2.0/24 traffic from reaching any network of Router1.
If we place the ACL on the router’s inbound or outbound interface, this will also prevent traffic from the 192.168.2.0/24 network from reaching any of Router1 and Router2’s networks. If we place the ACL inbound on interface Fa1/0 of Router2, this will also stop all traffic from the 192.168.2.0 network from reaching any of Router2’s networks.
So, the best place to place the ACL is Router 1’s Eth 1/0 interface. This is the closest interface to the destination. Therefore, we would apply a standard Ethernet 1/0 outbound interface ACL. This will prevent traffic from 192.168.2.0/24 from entering the Ethernet 1/0 interface and reaching 192.168.4.0/24 and all other networks reachable to the 192.168.4.0/24 network.
Extended ACLs Placement
On the other hand, extended access lists offer more advanced features. They allow you to filter traffic based on source and destination IP addresses and other parameters such as protocols and port numbers. Extended access lists provide a higher level of granularity and flexibility compared to standard access lists.
With extended access lists, you can specify the source IP address and the destination IP address. This allows you to control access to specific network resources based on source and destination. In addition, extended access lists consider the protocols and port numbers associated with the traffic, giving you even more control over the types of traffic allowed or denied.
To create an extended access list, you must assign it a number between 100 and 199 or 2000 and 2699. Similar to standard access lists, the lower the number, the higher the priority. Each entry in an extended access list consists of a permit or deny statement followed by the source and destination IP addresses, protocols, and port numbers.
It can filter traffic based on the source address, destination address, protocol type, and port number. Extended ACL gives more flexibility in filtering the kind of traffic and where to place the ACL. The basic rule for identifying an extended ACL is to put it close to the traffic’s source. Extended ACL filters unnecessary traffic from being sent across multiple networks.
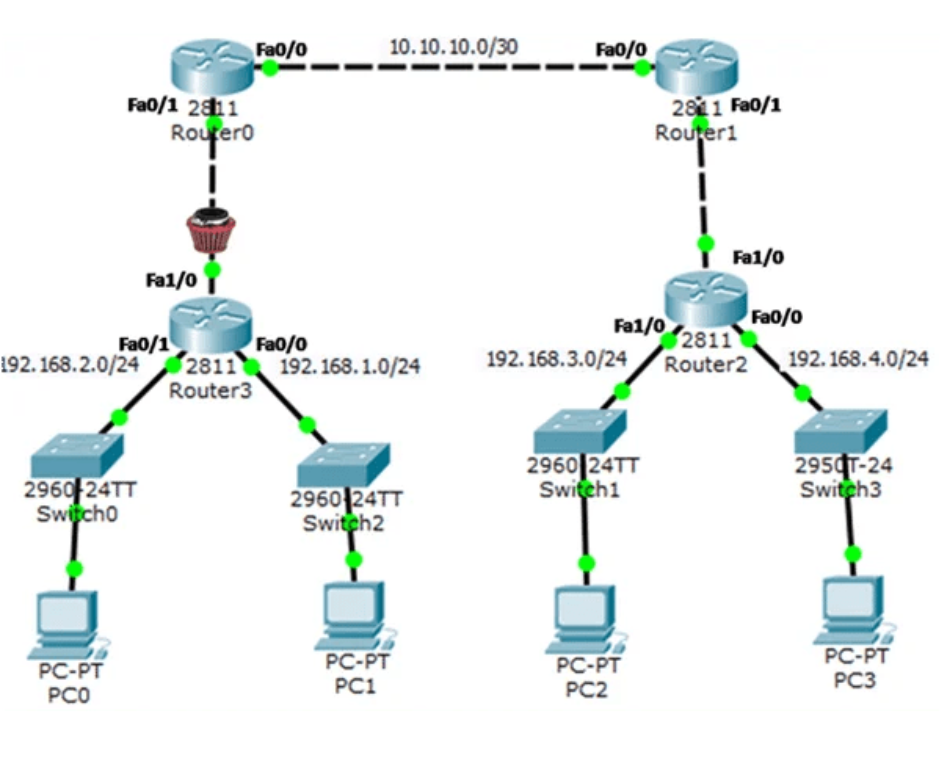
The network administrator places extended ACLs on devices that they can easily control. In the figure, the administrator wants to control FTP and telnet traffic from the 192.168.1.0/24 and 192168.2.0/24 networks. At the same time, all other traffic from both networks must be permitted to leave Router3 without any restriction.
There are several ways to accomplish these goals. We can configure an extended ACL inbound to Router3 Fa0/0 and Fa0/1 networks. However, this is not a best practice because we should configure an extended ACL inbound for both ACLs.
A best practice is to place an extended ACL on Router3 interface Fa0/1 outbound. The extended ACL specifies both source and destination addresses and enforces the rule, “Telnet and FTP traffic from the 192.168.1.0/24 and 192.168.2.0/24 network is not allowed to go to the 192.168.3.0/24 network.
The above type of ACL may also depend on the following:
- Ease of configuration– If we want to deny traffic coming from several networks, The first option is to use a single standard ACL on the closest to the destination. However, the main disadvantage of this ACL is the unnecessary use of bandwidth. So, we can configure an extended ACL on each router source router. This will save bandwidth by filtering the traffic at the source, but this requires creating extended ACLs for several routers.
- The extent of the network administrator’s control– Placement of the ACL also depend on the network administrator. He can control both the source and destination networks using an ACLs.
- The bandwidth of the networks – Filtering unwanted traffic at the source prevents consumption of the bandwidth. This is important in low bandwidth networks.
- Entering Criteria Statements. Then router receives traffic, the traffic is compared to all the access control entries in the order that the entries listed. The router continues comparing the access control entries until it finds the first match. The router will process the packet based on the first match found, and it will terminate by comparing more access control entries.
- If no matches are found in the access control entries and the router reaches the end of the list, the traffic is denied. This is because, by default, there is an implied deny at the end of all access control lists for traffic that was not matched to a configured entry. A single-entry access control list with only one denied entry has the effect of banning all traffic. So, one permit entry must be configured in an access control list.
Key Differences Between SACLs and EACLs
Now that we have a basic understanding of standard and extended access lists let’s explore their key differences.
The first major difference is that standard access lists only consider the source IP address, while extended access lists consider both the source and destination IP addresses. This means standard access lists are limited in controlling access to specific network resources based on the destination.
The second difference is that extended access lists provide more granular control over the types of traffic allowed or denied. With extended access lists, you can filter traffic based on protocols and port numbers, allowing you to have fine-grained control over the types of traffic that are permitted or denied.
Another important difference is the range of access list numbers that can be used. Standard access lists typically use numbers ranging from 1 to 99 or 1300 to 1999, while extended access lists use numbers ranging from 100 to 199 or 2000 to 2699. Choosing the appropriate range when creating access lists is important to avoid conflicts and ensure proper functionality.
Understanding the Syntax and Structure of SACLs
To effectively configure and implement standard access lists, it is crucial to understand their syntax and structure. Standard access lists are created using the access-list command, followed by the access list number and the permit or deny statement. The source IP address or wildcard mask is then specified to define the range of IP addresses allowed or denied.
For example, to create a standard access list that denies access from a specific IP address, you would use the following syntax:
access-list <access-list-number> deny <source-ip-address>
To create a standard access list that permits access from a specific range of IP addresses, you would use the following syntax:
access-list <access-list-number> permit <source-ip-address> <wildcard-mask>
It’s important to note that standard access lists are processed top-down, meaning that the first match determines the outcome. Therefore, it’s crucial to carefully consider the order of the access list entries to ensure that they are applied correctly.
Common use cases for Standard Access Control Lists (SACLs)
Standard Access Control Lists (SACLs) are the simpler of the two types of access lists. They are used primarily for filtering traffic based on source IP addresses. Let’s explore some common use cases for SACLs:
1. Restricting access to internal resources
One main use case for SACLs is restricting access to internal resources within a network. For example, you may want to allow access to a specific server from only a certain range of IP addresses. By configuring a SACL with the appropriate source IP addresses, you can effectively control access to the server and prevent unauthorized access from other IP ranges.
2. Blocking specific IP addresses
Another common use case for SACLs is blocking specific IP addresses or ranges from accessing your network. This can be useful when dealing with known malicious IP addresses or when you want to block traffic from a specific country or region. By creating a SACL that denies traffic from the specified IP addresses, you can effectively block unwanted traffic and enhance the security of your network.
3. Prioritizing network traffic
SACLs can also prioritize network traffic based on source IP addresses. This can be particularly useful in scenarios where you have limited bandwidth and must ensure that critical traffic gets priority over non-critical traffic. By configuring a SACL that allows traffic from necessary IP addresses while denying or limiting traffic from other IP addresses, you can effectively manage your network resources and ensure optimal performance.
In summary, SACLs are primarily used to filter traffic based on source IP addresses. They can also restrict access to internal resources, block specific IP addresses, and prioritize network traffic. Now, let’s explore the common use cases for Extended Access Control Lists (EACLs).
Common use cases for Extended Access Control Lists (EACLs)
Extended Access Control Lists (EACLs) offer more advanced filtering capabilities than SACLs. In addition to source IP addresses, EACLs can filter traffic based on destination IP addresses, protocols, and port numbers. Let’s dive into some common use cases for EACLs:
1. Controlling traffic based on source and destination IP addresses
One of the key advantages of EACLs is the ability to filter traffic based on source and destination IP addresses. This allows for more granular control over network traffic. For example, you may want to allow traffic from a specific source IP address to a specific destination IP address while denying traffic from other combinations of source and destination IP addresses. EACLs can be configured to achieve this level of control and enhance network security.
2. Filtering traffic based on protocols and port numbers
EACLs also allow traffic to be filtered based on protocols and port numbers. This is particularly useful when dealing with specific applications or services that use well-known port numbers. For example, you may want to allow traffic on port 80 for web browsing but block traffic on port 23 for Telnet access. By configuring an EACL with the appropriate protocol and port number restrictions, you can effectively control the flow of network traffic and ensure the security of your network.
3. Implementing access control for different network segments
EACLs can be used to implement access control between different network segments. For example, if you have a network with multiple VLANs, you may want to allow communication between specific VLANs while blocking communication between others. By configuring EACLs on the router or switch connecting the VLANs, you can control traffic flow between the different segments and enforce network segmentation for improved security.
In summary, EACLs offer advanced filtering capabilities compared to SACLs. They can control traffic based on source and destination IP addresses, filter traffic based on protocols and port numbers, and implement access control between network segments. Now, let’s conclude our exploration of standard and extended access lists.
FAQs
What are the main types of IPv4 ACLs in Cisco routers?
The primary types are Standard ACLs (filter by source IP, numbers 1-99), Extended ACLs (filter by source/destination IP, protocols, ports; numbers 100-199 or 2000-2699), and Named ACLs (alphanumeric names for standard or extended, improving manageability in IOS 12.0+ and IOS XE 16+). These enable precise traffic control.
How do inbound and outbound ACLs differ in operation?
Inbound ACLs filter packets before routing, reducing load by dropping early, ideal for single-source interfaces. Outbound ACLs filter after routing but before exit, suited for uniform filtering from multiple inbounds. Both have implicit deny and don’t affect router-originated packets.
What is wildcard masking and how is it calculated?
Wildcard masking uses a 32-bit mask where 0 matches bits exactly and 1 ignores them, inverse of subnet masks (subtract from 255.255.255.255). Examples: /24 subnet (255.255.255.0) wildcard is 0.0.0.255; /27 (255.255.255.224) is 0.0.0.31. Keywords like ‘any’ (255.255.255.255) or ‘host’ (0.0.0.0) simplify configs.
What benefits do ACLs provide in network management?
ACLs enhance performance by blocking unnecessary traffic (e.g., video streaming), control routing updates for bandwidth savings, ensure security by denying unauthorized access, and filter based on protocols/ports (e.g., allow SMTP, block Telnet). They classify traffic for priority processing in IOS XE.
How does packet filtering work with ACLs?
ACLs examine packet headers at Layer 3 (IP addresses, ICMP) and Layer 4 (TCP/UDP ports), processing ACEs sequentially. First match permits/denies; implicit deny drops unmatched. Applied per-interface inbound/outbound for efficient filtering and logging.
What is an Access Control List (ACL) in Cisco networking?
An ACL is a set of rules on Cisco devices like routers and firewalls to filter traffic, allowing or denying access based on criteria like IP addresses, protocols, and ports. It enhances security, performance, and traffic management in IOS or IOS XE environments.
What are the key benefits of using ACLs?
ACLs boost network performance by blocking unnecessary traffic, control routing updates to save bandwidth, provide security by restricting unauthorized access, and filter traffic by protocols/ports like allowing SMTP while blocking Telnet.
What are the steps to create an ACL?
Define rules per protocol, direction, and interface (Three P’s). For IPv4, use access-list commands; apply to interfaces with ip access-group. Consider IPv6 separately. Plan for up to 8 ACLs in dual-stack setups.
What are the general guidelines for using ACLs?
Place on border/firewall routers, between segments, or edges. Configure per protocol (IPv4/IPv6). Avoid over-filtering for performance. Prioritize IPv6 in dual-stack for CCNP-level scalability.
What is the ‘Three P’s’ principle in ACL guidelines?
One ACL per protocol (e.g., IPv4 vs IPv6), per direction (inbound/outbound), and per interface (e.g., GigabitEthernet0/0). Ensures targeted control without conflicts in multi-protocol setups.
Where should standard ACLs be placed?
Place close to the destination network to allow traffic to other areas while blocking specific paths. Example: On Router1’s outbound interface to deny 192.168.2.0/24 from reaching 192.168.4.0/24.
Where should extended ACLs be placed?
Place close to the source to filter unnecessary traffic early, saving bandwidth. Example: On Router3’s outbound to block Telnet/FTP from 192.168.1.0/24 and 192.168.2.0/24 to 192.168.3.0/24.
What are the key differences between standard and extended ACLs?
Standard: Source IP only (1-99). Extended: Source/destination IP, protocols, ports (100-199). Extended offers granularity; standard is simpler for basic tasks like blocking specific IPs.
What are common use cases for standard ACLs?
Restrict access to internal resources by source IP, block malicious IPs or regions, prioritize traffic for bandwidth management. Ideal for simple filtering without destination/protocol details.
Why is there an implicit deny in ACLs?
It ensures unmatched packets are dropped, providing comprehensive security. Always include at least one permit; a single deny entry blocks all. Process rules top-down for first-match action.