All Cisco routers and switches do not allow remote access by default via terminal programs like PuTTY or Tera Term. Remote connectivity options include Telnet (VTY Port) or SSH. SSH provides encrypted sessions and is strongly recommended by Cisco for remote administration due to Telnet’s vulnerabilities.
Prerequisites for CCNA/CCNP Students
- Basic knowledge of ACLs (review CCNA 200-301 Module 9).
- Cisco device with IOS 15+ or IOS-XE.
- Terminal software installed.
- Understanding of wildcard masks (e.g., 0.0.0.255 for /24 subnets).
However, if your router’s Cisco IOS does not support SSH (rare in post-2019 releases), fall back to Telnet with restrictions. For enhanced security—critical in CCNP enterprise designs—restrict VTY access to prevent brute-force attacks or unauthorized configs.
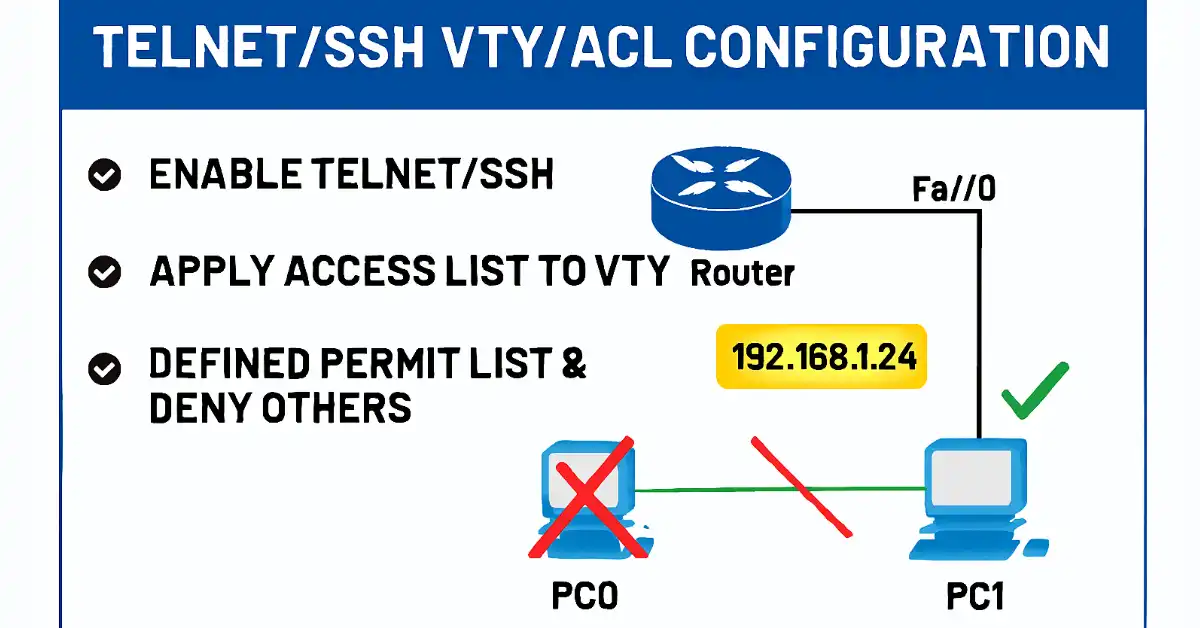
VTY port access restriction allows you to define which IP addresses are allowed Telnet access to the router EXEC process. We can also control administrative workstations using an ACL and an access-class statement configured on VTY lines.
The access-class command configured in line configuration mode restricts connections between a particular VTY/SSH and the addresses in an access list. Both standard and extended access lists apply to packets that travel through a router. An outbound Telnet extended ACL does not prevent router-initiated Telnet sessions by default.
Filtering Telnet traffic is usually considered an extended IP ACL function because it filters a higher-level protocol. However, a standard ACL can be used because the access-class command filters incoming or outgoing Telnet/SSH sessions by source address. The access-class command syntax is the following:
Router(config-line)# access-class < access-list-number> { in | out }
The parameter “ in” restricts incoming connections, and “out” restricts outgoing connections between the addresses in the access list and the Cisco device. We can allow a range of addresses or specific hosts.
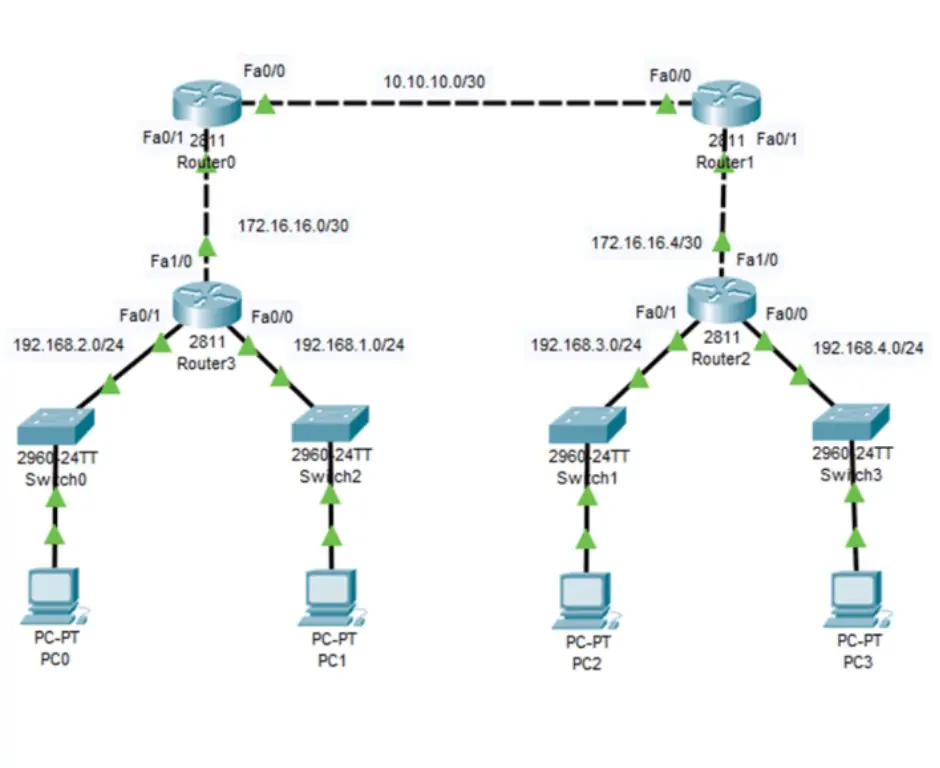
The example below allows a range of addresses to access VTY lines 0-4 to router 3. Network 192.168.1.0 is permitted in the ACL to access VTY lines 0-4, and all other networks are denied access to the VTY port.
R3>enable
R3#configure terminal
R3(config)#line vty 0 15
R3(config-line)#password StrongPass123!
R3(config-line)#login
R3(config-line)#transport input telnet ssh // Enable both, prefer SSH
R3(config-line)#access-class 2 in
R3(config-line)#exit
R3(config)#access-list 2 permit 192.168.1.0 0.0.0.255
R3(config)#access-list 2 deny any log // Add logging for denies
R3(config)#exit
R3#
Alternative: SSH-Only Config
R3(config)# hostname R3
R3(config)# ip domain-name example.com
R3(config)# crypto key generate rsa modulus 2048
R3(config)# username admin privilege 15 secret StrongPass
R3(config)# line vty 0 15
R3(config-line)# login local
R3(config-line)# transport input ssh
R3(config-line)# access-class 2 in
Using Named ACLs for VTY Security (CCNA Best Practice)
Instead of numbered ACLs, use named for readability:
R3(config)# ip access-list standard VTY-ACCESS
R3(config-std-nacl)# permit 192.168.1.0 0.0.0.255
R3(config-std-nacl)# deny any
R3(config-std-nacl)# exit
R3(config)# line vty 0 15
R3(config-line)# access-class VTY-ACCESS in
Verifying a Standard ACL used to secure a VTY Port
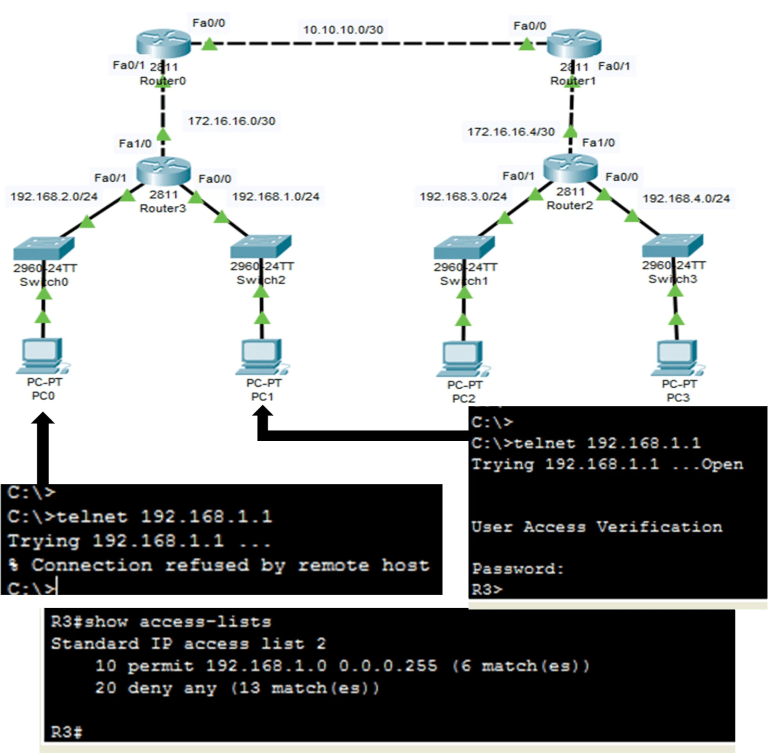
After configuring and applying ACL to VTY lines, verifying it is working as expected is important. The figure below shows a computer attempting to access R3 using telnet. Access list 2 has been configured on the VTY lines on R3. PC0 cannot access R3, but the attempt of PC1 successfully accessed the R3.
This is the expected result as we configured it. We can also use the show access-lists command after PC0 and PC1’s telnet attempts. The ACL statistics will show the match between the permit and deny lines.
Troubleshooting VTY ACL Issues
- Use
show lineto check active VTY sessions. - Debug denies:
debug ip packet(caution: high CPU). - Common errors: Forgot to enable
transport input; ACL applied out instead of in.
R3# show access-lists
Standard IP access list 2
10 permit 192.168.1.0, wildcard bits 0.0.0.255 (5 matches)
20 deny any log (3 matches)
IPv6 ACLs for VTY Security
For modern networks, apply IPv6 equivalents:
R3(config)# ipv6 access-list VTY-IPV6
R3(config-ipv6-acl)# permit ipv6 2001:DB8:1::/64 any
R3(config-ipv6-acl)# deny ipv6 any any
R3(config-ipv6-acl)# exit
R3(config)# line vty 0 15
R3(config-line)# ipv6 access-class VTY-IPV6 in
This ensures dual-stack compatibility in CCNP designs.
Real-World Scenarios
In a branch office, restrict VTY to admin subnets only, integrating with AAA for logging. For cloud-managed routers (e.g., Meraki), use similar concepts via dashboards.
Conclusion and Best Practices
Securing VTY with standard ACLs is foundational for CCNA but integrate with AAA/RADIUS for CCNP. Always test in lab environments.
FAQs
How do I configure a standard ACL for VTY security on a Cisco router?
Enter line config mode with line vty 0 15, set password and login, enable transport input (telnet or ssh), apply ACL with access-class <number> in, then define the ACL to permit trusted subnets and deny others. Verify with show access-lists to check matches, ensuring only authorized IPs connect remotely.
Why use standard ACLs instead of extended for VTY ports?
Standard ACLs filter by source IP only, sufficient for inbound VTY access control, and are simpler for CCNA basics. Extended ACLs add protocol/port filtering but aren’t needed for basic Telnet/SSH restrictions; they don’t block router-initiated sessions by default, making standards ideal for VTY security.
What are common issues when applying ACLs to VTY lines?
Forgotten transport input command blocks all access; incorrect wildcard masks permit unintended IPs; applying ‘out’ instead of ‘in’ fails inbound filtering. Troubleshoot with show line four sessions, debug ip packet for denies, and ensure ACL is numbered/named correctly before applying.
How does SSH improve VTY security over Telnet with ACLs?
SSH encrypts sessions, preventing eavesdropping (unlike plain-text Telnet), while ACLs restrict sources. Generate RSA keys, use transport input ssh, and local/RADIUS auth for CCNP-level setups; combine with ACLs for layered security against unauthorized remote access.
How to verify and troubleshoot VTY ACL configurations?
After attempts, run show access-lists for match counts; show running-config | section line vty to confirm application. If denied unexpectedly, check ACL order (implicit deny last), unlink/reapply, and log denies for auditing in enterprise environments.