Cyber security threats are a growing concern worldwide, escalating with AI and ransomware in 2025. Individuals and organizations rely on networks, making intrusions devastating.
Computer networks are necessary for everyday activities, and both individuals and organizations depend on their computers and networks. Intrusion to these computers by an illegal person can result in a network breakdown and loss of data and work. Attacks on a network can be disturbing, resulting in a loss of time and money due to damage or theft of significant information.
The intruders can enter the network through software vulnerabilities, guessing someone’s username and password, hardware attacks, or supply chain compromises (e.g., tainted hardware from vendors). An intruder is an individual, commonly called a hacker or software, that enters a computer without authorization. When an intruder (hacker) successfully gains access to the network, four types of security threats may happen:
Loss of Data and Manipulation
When a hacker successfully enters someone’s computer, he destroys or alters data records. Examples include sending a virus that encrypts files (ransomware) or breaking into a records system to change information.
Data and Identity Theft
Intruders steal confidential info for sale or fraud, often using deepfakes (2025 rise per SentinelOne). The individual usually obtains the personal document on their personal computer. The intruder stole this personal information. Using this information, an intruder can get legal documents, make an unauthorized purchase, and apply for credit.
Disruption of Service
If the intruder can’t get in, he tries to ensure that no one else can. This is the DoS (denial-of-service attack). This kind of security threat does not try to get information directly. Depending on which service crashes under the load, its effect can expose other previously protected resources.
Advanced DoS Variants: DDoS and Beyond
| Threat Type | Description | 2025 Impact | Defense |
|---|---|---|---|
| DDoS | Floods networks with traffic from botnets. | Increased via IoT devices (e.g., 2025 attacks up 30% per Fortinet). | Rate limiting, cloud-based scrubbing. |
| Zero-Day Exploits | Attacks unknown vulnerabilities. | Common in supply chains. | Patch management, threat intelligence. |
Physical Security Threats
Physical security is another crucial aspect of Cyber security. The elements of physical security must be dealt with in the organizational policy. Physical security threats have four classes:
- Hardware security threats – this is a security threat related to hardware. It damages network devices, servers, and workstations.
- Electrical threats — This threat concerns the input voltage. The voltage may be insufficient, spike, unconditioned, or loss of power.
- Maintenance threats — This threat concerns poor handling of electrical components, poor cabling and labeling, and a lack of spare parts.
- Environmental threats — Environmental threats are also significant. Temperatures that are too hot or cold and humidity that are too wet or dry are ecological threats.
To limit the physical damage to equipment, make a security plan as follows:
- Lockup equipment
- Prevent unauthorized access
- Maintain electronic logs of entry and exits
- Use security cameras
Integrating Physical and Cyber Security (PhySec)
Use zero-trust architecture to link physical access (e.g., badge logs) with network monitoring. Case study: 2025 NCSC report on nation-state attacks combining physical infiltration with hacking.
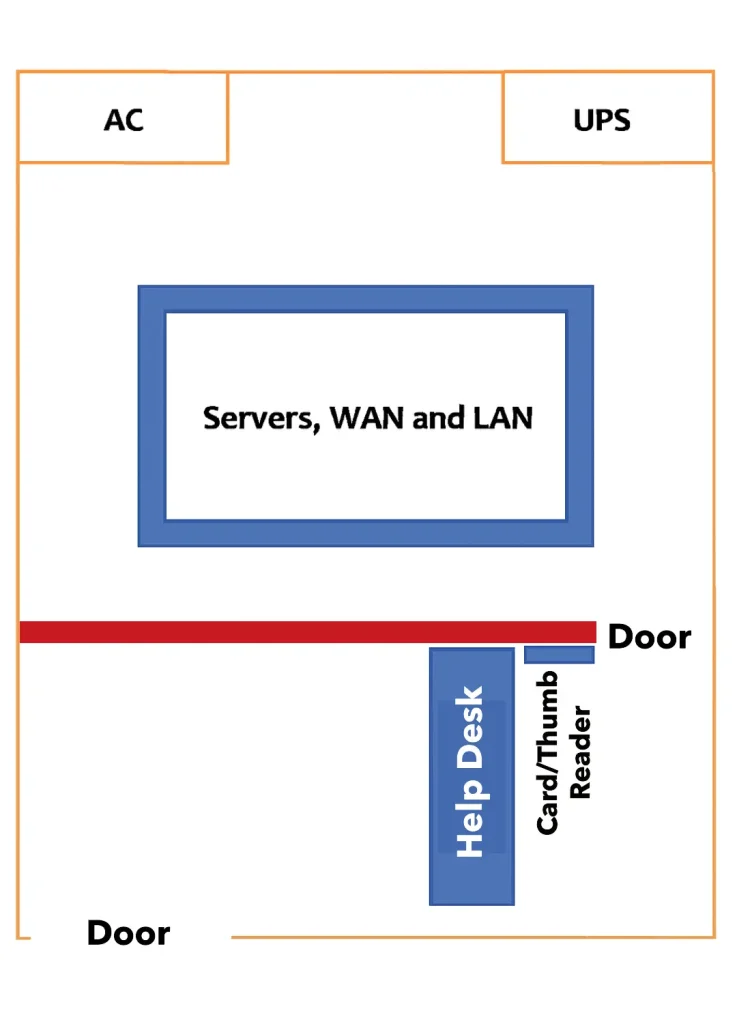
The figure below illustrates a general floor plan for a secure computer room for a network.
Emerging Cybersecurity Threats in 2025
In 2025, threats have evolved with AI and quantum computing. AI-driven attacks automate phishing and malware (e.g., deepfakes for identity theft). Ransomware remains top, with 47% of organizations affected per WEF 2025 report. Supply chain attacks (e.g., 2025 CrowdStrike outage) compromise vendors. IoT vulnerabilities expose unsecured devices.
Defense Against Threats
In defending against network attacks, there are four sets of tools that will help you keep your network secure against unauthorized access, monitoring, and network attacks: management, firewall, encryption, and endpoint security.
Management
Management is the primary defense against network attacks. The following actions should be implemented in configuration management against network attacks.
Backup, Upgrade, Update, and Patch
The machines in the network should be running up-to-date because the latest update can provide more effective defense against network attacks. Whenever new malware is released, the operating systems need the latest update with the latest antivirus software. The best way to keep up-to-date against network attacks is to download security updates and patches from the operating system vendor.
The management needs to create a central patch server for critical security patches. All other systems must have access from time to time. Any required security patches not installed on a host are automatically downloaded from the server and installed automatically for user intrusion.
Backup is essential when defending against network attacks. Each computer should have the latest copy of the backup. All configuration files in your Operating Systems or Applications should have enough security.
Authentication, Authorization, and Accounting
Authentication, authorization, and accounting (AAA) Cyber security services provide primary access control on a network device. AAA authenticates and controls access to a network; it also controls the users’ what they can do while they are logged in.
Passwords
The password is very important to protect network devices against attacks. It is important to use strong passwords rather than the default password or an easy password. For passwords, implementation follows the below steps.
- Use a complex password, including uppercase letters, lowercase letters, numbers, symbols, and spaces, only if allowed.
- Use a minimum of 8 characters password, preferably 10 or more characters.
- Do not use common dictionary words for the password.
- Avoid passwords based on repetition, number sequences, letter sequences, usernames, relative or pet names, and misspell words.
- Do not use biographical information, such as birthdates, ID numbers, ancestor names, or other easily identifiable information.
- Change passwords often.
- Do not write passwords down and leave them in precise places.
Following are examples of passwords
Weak Password
1234567
Strong Password
P@12>fo<ur^1978
No ^^&34@fsc^hub
On Cisco routers and switches, leading spaces are ignored for passwords, but spaces after the first character are part of the passwords. The passphrase is a password that uses the space bar to create a phrase of many words. The passphrase is also a strong password.
Firewalls
A firewall is the most efficient security tool for protecting users from network attacks. The firewalls exist in between two or more networks, controlling traffic and preventing unauthorized access between them. End systems also use a personal firewall. The following are different techniques that use a firewall for filtering:
- URL filtering prevents or allows access to websites using Keywords or URLs. Packet filtering uses a MAC address or IP address to prevent or allow access.
- Application filtering – Prevents or allows access by specific application types.
- Stateful packet inspection (SPI) – Incoming packets must be valid responses from internal hosts. Voluntary packets are blocked unless permitted particularly. SPI also recognizes and filters specific types of attacks.
- Next-Gen Firewalls (NGFW) with AI inspection.
Encryption
The administrator can use encryption as a defense against network attacks. It can give protection against eavesdropping as well as sniffer attacks. Internet Protocol Security (IPSec), Private Key Infrastructure (PKI), and Virtual Private Networks (VPN) can also secure a network against attacks. Use post-quantum encryption to counter quantum threats (emerging in 2025 per Qualysec).
Endpoint Security
Individual computer (host) system or device that acts as a network client, common endpoints are laptops, desktops, servers, smartphones, and tablets. Securing and preventing these devices from a network attack is the most challenging task for a network administrator.
Securing endpoints must have well-documented policies, and the employees must be aware of these rules. The employees must be trained for proper using the network. The policies also include the use of antivirus software and host intrusion prevention.
Compliance and Regulatory Considerations
Align defenses with NIST, GDPR; non-compliance risks fines up to 4% revenue.
Tools and Technologies for 2025
Recommend SIEM (e.g., Splunk), EDR (e.g., CrowdStrike), MFA tools.
Authored by a CISSP-certified cybersecurity expert with 15+ years in threat hunting.
FAQs
What are the most common cyber security threats in 2025?
Common threats include ransomware, AI-driven phishing, supply chain attacks, DDoS, and IoT vulnerabilities. Per Microsoft’s 2025 report, extortion motivates 72% of attacks, emphasizing the need for proactive defenses like updates and MFA.
How can organizations defend against ransomware attacks?
Implement backups, patch management, and endpoint detection tools. Train employees on phishing, use NGFW, and adopt zero-trust. In 2025, AI tools help detect anomalies early, reducing impact as seen in WEF reports on rising cyber inequity.
What is the difference between information theft and identity theft?
Information theft involves stealing confidential data for sale or use, while identity theft uses personal info for fraud like credit applications. Both can lead to financial loss; prevent with encryption and monitoring per CISA guidelines.
Why are strong passwords important for cyber security?
Weak passwords enable brute-force attacks. Use complex ones (10+ characters, mixes) or passphrases. In 2025, combine with MFA to counter credential stuffing, as 66% of breaches involve stolen credentials per Fortinet stats.
How do physical security threats impact networks?
Threats like hardware tampering or environmental damage can expose devices. Mitigate with locked rooms, cameras, and logs. Integrate with cyber defenses to prevent combined attacks, as noted in 2025 NCSC reports on nation-state threats.



