Network redundancy ensures high availability and reliability in modern networks by providing alternate paths for data transmission, allowing seamless failover if a link or device fails. In CCNA/CCNP contexts, it shares traffic loads, boosts capacity, and employs protocols like Spanning Tree Protocol (STP) for Layer 2 loop prevention, or First Hop Redundancy Protocols (FHRP) like HSRP for gateway redundancy. With the rise of hybrid cloud environments (as of 2025), redundancy now integrates with SDN controllers for automated failover.
According to Cisco’s 2025 Networking Trends Report, redundant designs achieve 99.999% uptime, critical for zero-trust architectures in enterprise networks.
Key Benefits of Network Redundancy
- Eliminates single points of failure
- Enables load sharing across multiple paths
- Increases overall network capacity
- Provides fault tolerance during hardware or link failures
Network Redundancy at OSI Layers 1 and 2
The three-tier hierarchical network attempts to eliminate a single point of failure on the network. Multiple cabled connections between switches provide physical redundancy in a switched network.
Network redundancy improves the reliability and availability of the network. Alternate physical connections for data to pass through the network make it possible for users to access network resources, regardless of any interference.
Nowadays, the availability of the network is very necessary for every organization to complete their business needs. So, the network infrastructure plan is a serious component. Path redundancy eliminates the possibility of failure and continues the services without any disruption.
A hierarchical network design that uses core, distribution, and access layers with network redundancy attempts to eliminate any disruption of network services to users.
Redundant networks need physical connection, including logical redundancy. However, there are possibilities of physical and logical layer 2 loops in the redundant paths in a switched Ethernet network.
When multiple paths exist between two switches on a network, and there is no spanning tree protocol between both, a Layer 2 loop occurs. A Layer 2 loop can result in three primary issues:
- MAC database instability
- Broadcast storms
- Multiple frame transmission
MAC Database Instability (Layer 1 Redundancy)
Ethernet frames require a mechanism to block the continued propagation of broadcast frames on a switched network. The Ethernet frames propagate between switches endlessly, or until a link is disrupted and breaks the loop because the Ethernet frames have no TTL value in their frame headers. This nonstop propagation between switches can result in MAC database instability.
The MAC address instability occurs due to broadcast frame forwarding, which is forwarded out to all switch ports except the original ingress port. The broadcast ensures that all devices in a broadcast domain can receive the frame.
So, if there is a redundant network path between network switches, that causes an endless loop result. When a loop occurs, it is possible for the MAC address table on a switch to constantly change with the updates from the broadcast frames, which results in MAC database instability.
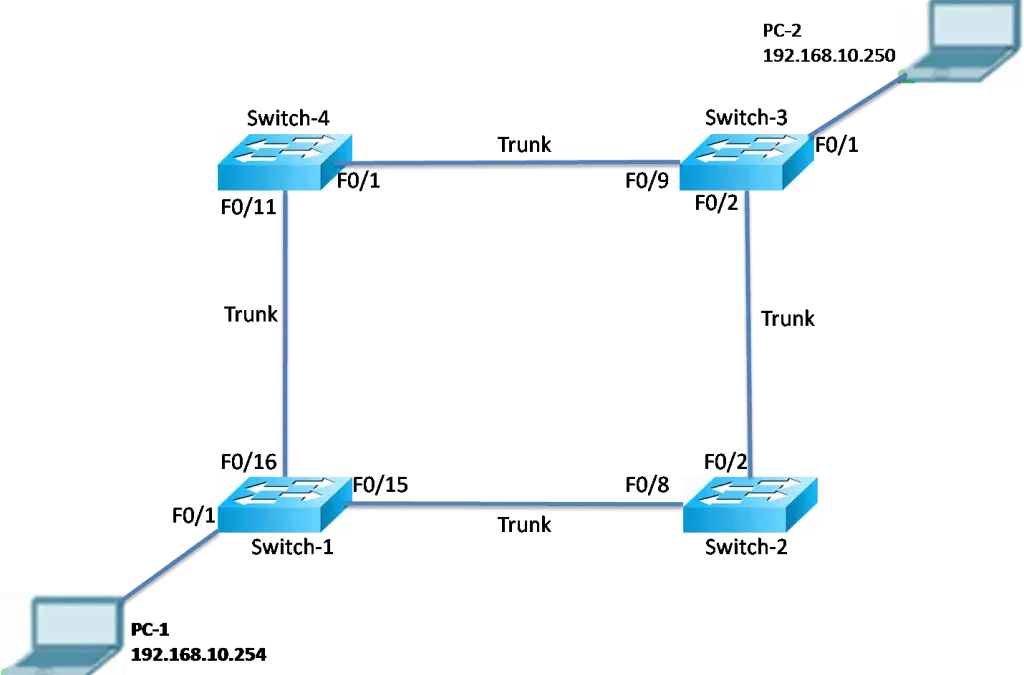
Now look at the below topology PC-1 and PC have a redundant path without any proper logical mechanism. The process of packet sending is as under:
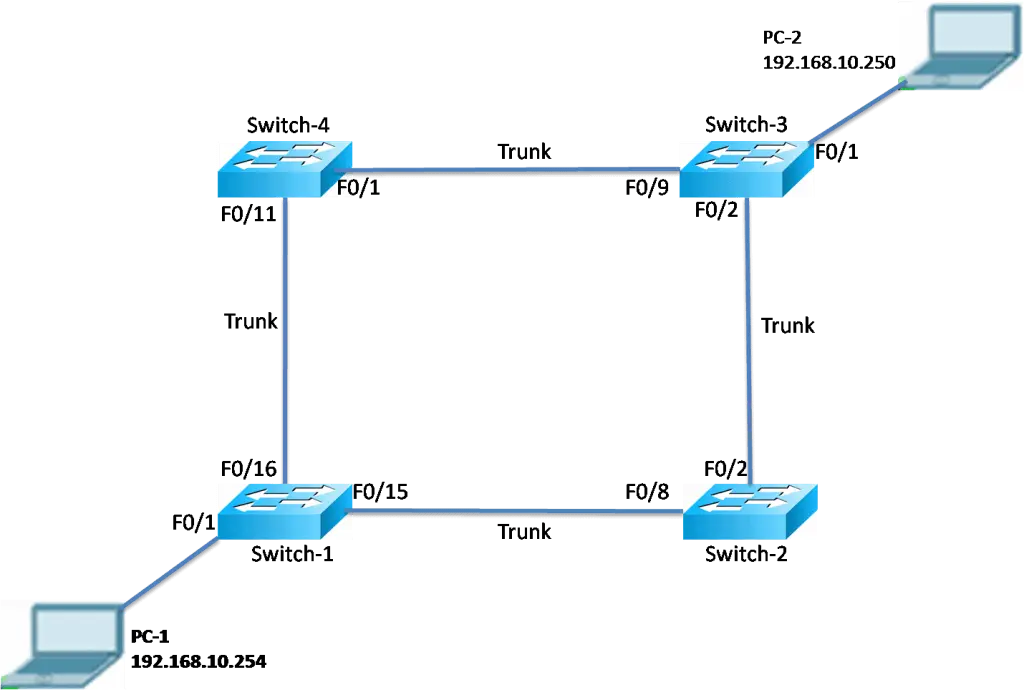
- When PC1 sends a broadcast frame to Switch-1. Switch-1 will receive the broadcast frame on F0/1. When Switch-1 receives the broadcast frame, it updates its MAC address table that PC1 is available on port F0/1.
- Due to the broadcast frame, Switch-1 forwards the frame out to all its ports, including both trunks. When the broadcast frame arrives at Switch2 and Switch-4, the switches update their MAC address tables to indicate that PC1 is available on port F0/8 on Switch-2 and F0/11 on Switch-4.
- So, when the broadcast frame is received on Switch-2 and Switch-4, they forward the frame out all ports except the incoming ports. Both switches send the broadcast frame to Switch-3. If Switch-3 received the broadcast frame from Switch-2 first, it maintains the MAC address table that PC-1 is available on F0/2 and floods the frame out to all its ports exceptport 0/2. Meanwhile, it receives the frame from switch-4 on the interface F0/9, and switch-3 overwrite its MAC address table again and flood the same packet to all its interfaces except F0/9
- Now again the same packet will circulate into the entire network. Each switch forwards the broadcast frame out all of its ports, except the ingress port. Each time, the MAC address table is updated with the last entry received from the other two switches.
This process continues nonstop until the loop is broken. The loop can be broken by disconnecting the connections physically or powering down one of the switches in the loop. The loop between switches puts a high load on the CPU load of all switches, which slows down performance on the switch when genuine traffic arrives.
A host participating in the network loop cannot access other hosts on the network. At last, due to the constant changes in the MAC table, the switch does not know which port to forward unicast frames.
Broadcast Storms (Layer 1 Redundancy)
When so many broadcast frames are caught in a Layer 2 loop that consumes all available bandwidth and there is no bandwidth available for legitimate traffic and the network becomes unavailable for data communication, the broadcast storm occurs. This is also known as an effective denial of service (DoS).
A broadcast storm is expected on a looped network because more devices send broadcast traffic over the network, which causes more broadcast traffic, which is caught in the loop and consumes network resources. This finally creates a broadcast storm that causes the network to fail.
There are other disadvantages of the broadcast storm because traffic is forwarded out every port on a switch; all the connected devices must process all the broadcast traffic that is flooded endlessly around the looped network. This can cause the end device to malfunction.
Duplicate Unicast Frames (Layer 1 Redundancy)
Broadcast frames are not the only type of frames that are affected by loops. Unicast frames sent onto a looped network can result in duplicate frames arriving at the destination device.
Most upper-layer protocols cannot recognize duplicate frames. This protocol generally makes use of a sequence-numbering mechanism to assume that the transmission has failed and that the sequence number has recycled for another communication session. Ethernet protocol (Layer 2) requires a mechanism to recognize and eliminate endlessly looping frames.
Layer 3 implements a TTL mechanism for eliminating the loops because TTL limits the number of times a Layer 3 networking device can retransmit a packet. Layer 2 devices do not have a mechanism like TTL, so they continue to retransmit looping traffic again and again.
STP, a Layer 2 loop-avoidance mechanism, was developed to solve these problems. To stop these issues from occurring in a redundant network, some type of spanning tree must be enabled on the switches. By spanning tree is enabled in all the Cisco switches to stop Layer 2 loops from occurring.
FAQs
What happens if STP is disabled in a redundant network?
Without STP, frames loop infinitely, causing broadcast storms, MAC table instability, and duplicate unicast delivery. Bandwidth collapses; use show mac address-table to observe flapping. Enable spanning-tree mode rapid to resolve.
How does HSRP provide gateway redundancy for end devices?
HSRP creates a virtual IP (e.g., 192.168.1.1) shared by two routers. One is active, the other standby. If active fails, standby takes over in <1s using preempt and timers. Config: standby 1 ip 192.168.1.1.
Why is Layer 3 redundancy important in enterprise networks?
Layer 3 redundancy via OSPF/EIGRP ensures alternate routing paths. maximum-paths 4 enables load balancing. Prevents single router failure from isolating subnets. Critical for 99.999% uptime in 2025 zero-trust designs.
How can I simulate a broadcast storm in Packet Tracer?
Build 3 switches in a triangle, connect PCs, disable STP (no spanning-tree vlan 1). Ping continuously. Monitor CPU spike and show interfaces counters. Re-enable STP to watch blocked port and storm cessation.
What is the role of BPDU in Spanning Tree Protocol?
BPDUs are control messages sent every 2 seconds to elect root bridge and detect loops. Switches compare Bridge ID; lowest wins. Non-root ports transition to blocking if superior BPDU received. Use show spanning-tree to verify.