Challenge Handshake Authentication Protocol (CHAP) periodically checks the character of the far off hub utilizing a three-way handshake. The hostname on one switch must match the username the other switch has designed. The passwords should likewise coordinate. The password value is variable and changes unpredictably while the link exists.
When the PPP link establishment phase is complete, the local router sends a challenge message to the remote node containing Challenge Handshake Authentication Protocol (CHAP) user name and a hash value that is based on the Challenge Handshake Authentication Protocol (CHAP)Password.
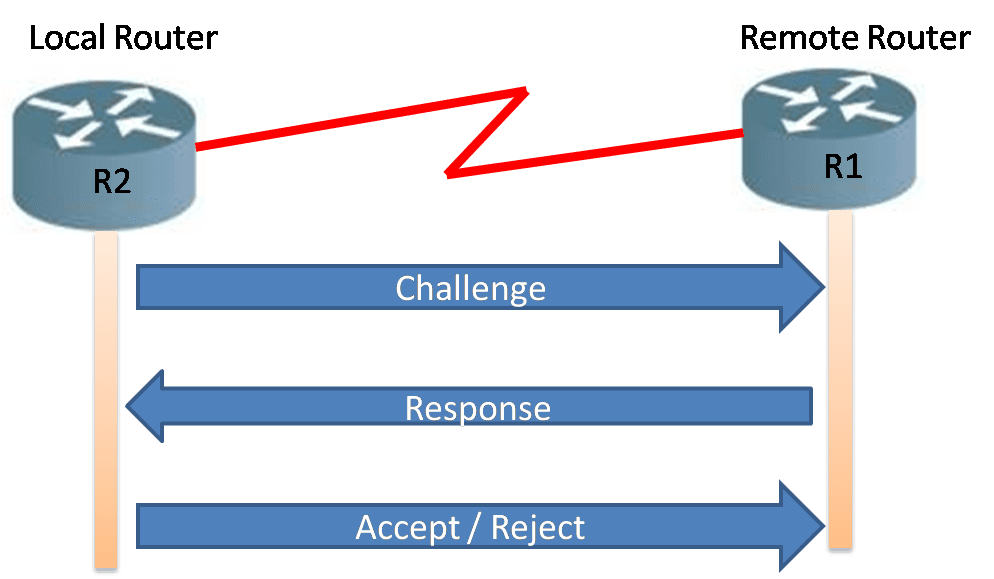
The remote router compares the local routers username and password in its local database and calculates hash value with the value sent from local router. The remote node then responds with a calculated value using a one way hash function, usually with Message Digest 5 (MD5) based on the password and challenge message. The figure1 illustrates the CHAP 3 way handshake.
The local router checks the reaction against its own calculation of the likely hash value. In case of value match, the initiating node acknowledges the authentication; otherwise, the initiating node immediately terminates the connection.
Challenge Handshake Authentication Protocol (CHAP) provides better protection then PAP because it protects devices from playback attacks using a variable challenge value that is unique and unpredictable. The challenge and resulted hash value are unique and random. The use of repetitive challenges limits the time of vulnerability to any single attack. The local router or a third-party authentication server is in control of the frequency and timing of the challenges.
Challenge Handshake Authentication Protocol (CHAP) Configuration
We have learnt in the previous section that CHAP periodically identifies the remote node using a three-way handshake. The hostname on one router should match the username the other router has configured. The passwords also required to match. This occurs on initial link establishment and can be repeated any time after the link has been established. The commands for configuring CHAP on R1 are the following:

Router R-1 (Local)
Router>enable
Router#config terminal
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#hostname R1
R1(config)#username R2 password Cisco
R1(config)# interface serial0/0/0
R1(config-if)#no shut
R1(config-if)# ip address 192.168.10.1 255.255.255.252
R1(config-if)# ipv6 address 2001:AD01:BD00::1/64
R1(config-if)# clock rate 64000
R1(config-if)#encapsulation PPP
R1(config-if)#ppp authentication chap
R1(config-if)#exit
Router R-2 (Remote)
Router>enable
Router#config terminal
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#hostname R2
R2(config)#username R2 password ccna12345
R2(config)# interface serial0/0/0
R2(config-if)#no shut
R2(config-if)# ip address 192.168.10.2 255.255.255.252
R2(config-if)# ipv6 address 2001:AD01:BD00::2/64
R2(config-if)# clock rate 64000
R2(config-if)#encapsulation PPP
R2(config-if)#ppp authentication chap
R2(config-if)#exit


