Cybersecurity
Welcome to NetworkUstad’s Cybersecurity Hub – your comprehensive resource for staying secure in an increasingly connected world. In today’s digital landscape, cyber threats evolve faster than ever. From sophisticated ransomware attacks to simple phishing scams, businesses and individuals face constant risks. Our cybersecurity section delivers practical, actionable insights to help you build robust defenses and protect what matters most. Whether you’re a security professional, IT administrator, business owner, or someone concerned about digital privacy, you’ll find expert guidance covering everything from fundamental security principles to advanced threat protection strategies. What You’ll Discover: 🔐 Security Fundamentals – Master the CIA Triad, understand information security basics, and build a strong foundation in cybersecurity principles. 🛡️ Threat Intelligence – Learn about different attack vectors, hacker types, malware categories, and emerging cyber threats targeting organizations worldwide. 🔒 Protection Strategies – Explore practical defense mechanisms including encryption, multi-factor authentication, network security, endpoint protection, and access controls. 📊 Compliance & Governance – Navigate regulatory requirements like GDPR, HIPAA, PCI DSS, and industry frameworks such as NIST and ISO 27001. ⚡ Incident Response – Prepare for the inevitable with comprehensive guides on breach detection, containment, recovery, and forensic analysis. 🚀 Emerging Technologies – Stay ahead with insights on AI security, cloud protection, IoT vulnerabilities, blockchain security, and quantum computing threats. 💼 Enterprise Security – Discover strategies for securing hybrid workforces, protecting corporate data, managing third-party risks, and building security-aware cultures. 🎓 Career Development – Explore ethical hacking careers, certification paths (CEH, CISSP, OSCP), and skill development resources. Our articles combine technical depth with practical applicability. We break down complex security concepts into digestible insights, provide real-world examples, and offer step-by-step implementation guides. No unnecessary jargon—just clear, actionable cybersecurity knowledge you can use immediately. From understanding basic threats to implementing enterprise-grade security architectures, NetworkUstad’s cybersecurity content empowers you to make informed decisions and take meaningful action. We cover the full spectrum: network security, application security, data protection, cloud security, mobile security, and everything in between. Security isn’t a one-time project—it’s an ongoing journey. Join thousands of readers who trust NetworkUstad to keep them informed about the latest threats, best practices, and innovative solutions in cybersecurity. Protect your network. Secure your future. Start exploring our cybersecurity resources today.

Browser Plugins and Poisoning: Risks, Exploits, and Defenses in Cybersecurity
Security backdoors and vulnerabilities can severely impact web browsers, leading to unwanted pop-up ads, collection of personal data, or installation of adware, viruses, or spyware. Cybercriminals often target a browser’s executable files, core components, and browser plugins to gain unauthorized access. Browser Plugins A browser plugin (now often called an extension or add-on in modern...

Vishing, Smishing, Pharming, and Whaling in Cybersecurity: Definitions, Examples, and Prevention Tips
In the ever-evolving landscape of cybersecurity, social engineering attacks like vishing, smishing, pharming, and whaling continue to exploit human vulnerabilities alongside network weaknesses. According to the 2025 Verizon Data Breach Investigations Report, phishing variants account for over 30% of breaches, with vishing and smishing rising due to mobile and VoIP adoption. As a network engineer,...

What Is Phishing? A Comprehensive Guide for Cybersecurity Enthusiasts (Updated 2025)
As discussed in previous articles on network security, phishing remains a low-effort, high-reward tactic for cybercriminals. They send fake emails, text messages, or create authentic-looking websites to steal personal and financial data. This technique, also known as spoofing, involves forging email headers or IP addresses to mimic trusted sources, often evading basic network filters like...

Understanding Spyware, Adware, and Scareware: A Cybersecurity Guide for Enthusiasts
In the previous article, I discussed malware, including its types: viruses, worms, ransomware, Trojan horses, logic bombs, back doors, and rootkits. This article dives deeper into additional malware types—spyware, adware, and scareware—focusing on their mechanics, network implications, and real-world impacts. As a network engineer with years of experience in cybersecurity, I’ll emphasize how these threats...

Identifying Spam Mail: A Comprehensive Cybersecurity Guide for 2025
Email remains a universal service for billions worldwide, serving as one of the most popular communication tools. However, its widespread use comes with significant vulnerabilities, making it a prime target for cybercriminals. These unsolicited messages, commonly known as “junk mail” or spam, are predominantly sent by advertisers or malicious actors. Criminals exploit spam to distribute...
What is Malware and Malicious Software? (Updated 2025)
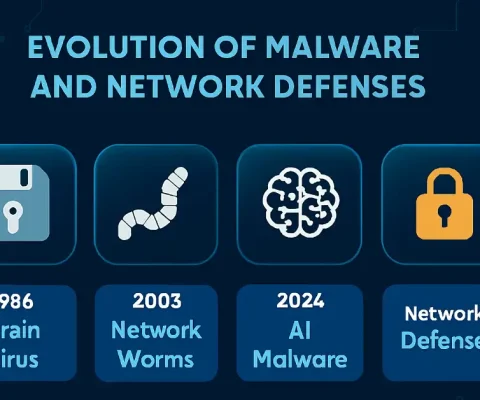
Updated: October 19, 2025—Includes latest threats and network defenses. Malware, or malicious software, is a program or file designed to disturb computer processes and operations or gain unauthorized entry to the computer system, often via network protocols like RDP or SMB, without the user’s knowledge or permission. Malware has become a common term for all...

Thwarting Cybercriminals: Master Key Measures and Strategies for Cybersecurity Enthusiasts in 2025
As a cybersecurity and networking expert with extensive experience in securing enterprise environments, I’ve seen firsthand how cybercriminals evolve their tactics. Thwarting cybercriminals isn’t easy, but companies, governments, and organizations are taking proactive steps to limit and discourage these threats. In this article, we’ll explore key actions and measures, updated for 2025, with practical insights...

Cyber Security Threats and Defenses: A Comprehensive Guide for 2025
Cyber security threats are a growing concern worldwide, escalating with AI and ransomware in 2025. Individuals and organizations rely on networks, making intrusions devastating. Computer networks are necessary for everyday activities, and both individuals and organizations depend on their computers and networks. Intrusion to these computers by an illegal person can result in a network...
What is VLAN Attacks – Brief Explanation
In the previous article, I explained how trunks work. By default, trunk ports can use all VLANs and pass traffic for multiple VLANs across the same physical link between switches. The VLAN simplifies network administration and maintenance. It also improves the performance of the network, but it has some backhaul for hackers which is necessary...