
Technology
Emerging technologies and innovation trends

What Is Call Center Software?
Hey folks! Today, we’re diving into how to choose call center software. This tool is crucial for anyone handling client calls. So, what is call center software? It’s a tool that manages all processes in your call center. Imagine you have many operators and hundreds of calls daily—everything needs to be organized. That’s where this...

Take Control of Your Photos: How to Unsyncing Google Photos
It’s no wonder that many see Google Photos as a staple. It offers easy photo backup and storage across devices, features that have contributed to its popularity. But, the convenience of automatic syncing might not always align with your needs. Consequently, you may want to use less storage. You may want to improve privacy. Or,...

Revo Technologies: More Than Just a Computer Store in Murray, Utah
Revo Technologies is in Murray, Utah. It is a trusted partner. It helps people and businesses achieve their tech goals. They specialize in computer and IT solutions. But, they offer much more than just a computer store. They offer personalized service and have technical expertise. They are also committed to the community. This has made...
Cannot connect to the docker daemon at unix:///var/run/docker.sock. Is the docker daemon running?” A Docker User’s Nightmare
Those who’ve tried containerization have seen the Docker error message. It says “cannot connect to the docker daemon at unix:///var/run/docker.sock.” Is the docker daemon running?” is an unwelcome but familiar sight. This cryptic message often starts a frustrating troubleshooting journey. It leaves developers scratching their heads and questioning their sanity. This article explores the heart...

Top 10 Paid VPNs of 2024 – The Ultimate Guide
In my blog, I conducted an extensive test and reviewed ALL the best paid VPNs for work and beyond. My subjective-objective ranking will help choose a VPN suitable for solving most basic tasks for 99% of regular users. Therefore, I first recommend that ordinary users who need a VPN simply to access blocked resources familiarize...

Top 10 Penetration Testing Tools You Should Know About in 2024
As cyber threats continue to evolve in sophistication, the need for robust penetration testing has never been more critical. Penetration testing tools play a vital role in identifying and exploiting vulnerabilities within your systems, enabling you to strengthen your defences. Here, we explore the top 10 penetration testing tools you should know about in 2024, each offering...

Why Choose Ite Nexar Dashcam for Your On-Road Safety
Navigating through today’s rapidly moving world frequently involves unavoidable hazards. But imagine if you could equip your vehicle with a smart wingman. One that is entirely committed to securing your safety. Nexar Dashcam emerges as a prime pick for drivers who value tranquillity while on the go. Let’s delve into why Nexar Dashcam should be...
Record That Call: How to Capture iPhone Conversations Without an App
iPhones are famously security-conscious, and that extends to recording phone calls. Apple’s phone operating system is different. Unlike some others, it lacks a built-in call recording feature. But that doesn’t mean you’re out of luck if you need to record an important talk. Let’s explore some workarounds that let you record incoming calls on your...

Instanavigation The Digital Navigation of the Future
In the digital age, navigation has evolved greatly from utilizing a basic map and compass. These days, a brand-new phenomenon known as “instanavigation” is beginning to appear. This expression combines the words “instant” with “navigation.” It captures the instantaneous, speedy navigation that modern technology offers. Comprehending Instanavigation Moving from one location to another is only...
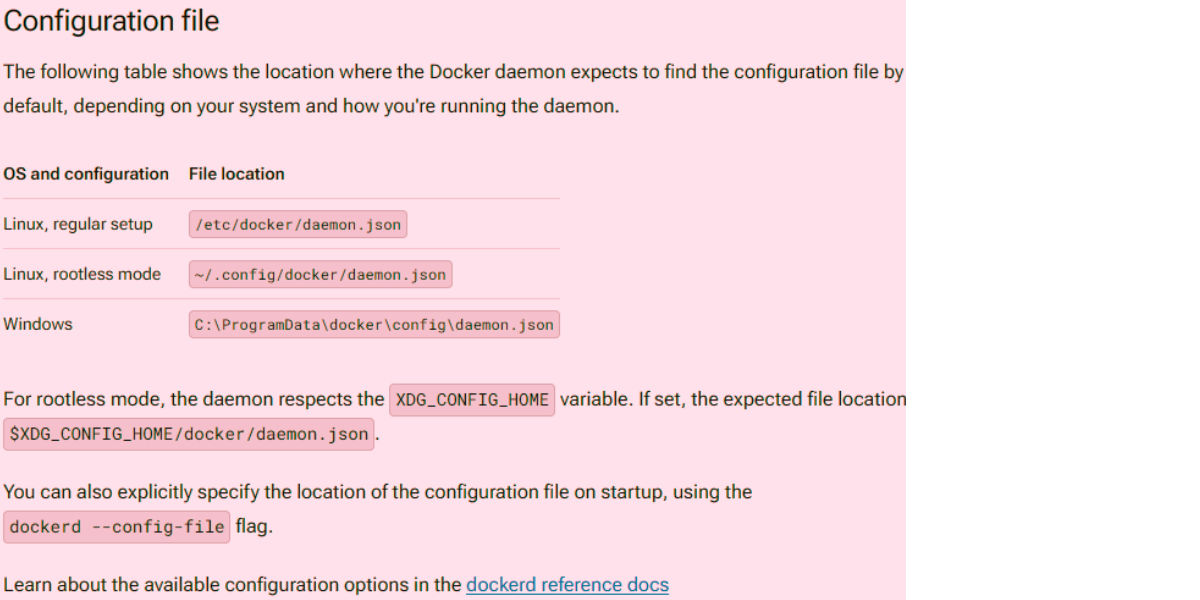
Research Report: Troubleshooting “Cannot Connect to the q
Caution Allowing Docker to accept connections from remote clients may expose you to risks such as unauthorized host access and potential attacks. Understanding the security risks associated with making Docker accessible over the network is crucial. If the connection is not properly secured, remote non-root users could potentially obtain root access on the host. In...