Over 80% of data breaches in 2025 involved compromised credentials, according to Verizon’s Data Breach Investigations Report. Multi-factor authentication (MFA) blocks 99.9% of account takeover attacks when properly implemented, yet only 52% of organizations enforce it universally per Microsoft’s 2026 Digital Defense Report. Mastering MFA delivers bulletproof account protection in an era of relentless cyber threats.
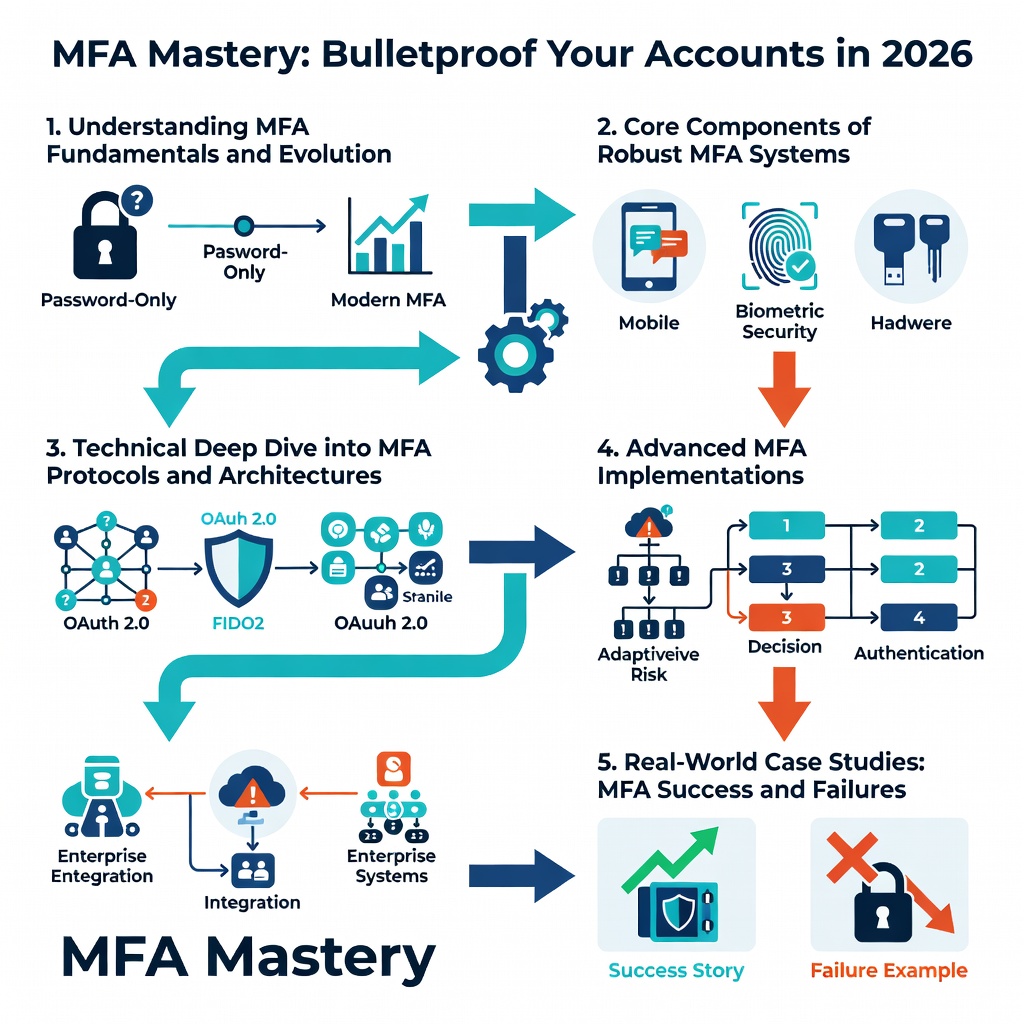
Understanding MFA Fundamentals and Evolution
MFA adds layers beyond passwords, verifying identity through multiple factors: something you know (password), have (device), or are (biometrics). This framework evolved from basic SMS codes in the early 2010s to sophisticated protocols leveraging encryption and hardware security modules.
Historically, single-factor authentication dominated until high-profile breaches like the 2012 LastPass incident exposed millions. By 2026, standards like FIDO2 and WebAuthn define modern MFA architecture, enabling passwordless flows with public-key cryptography.
“MFA isn’t a luxury; it’s table stakes for security,” states Kevin Mitnick, renowned cybersecurity expert and author.
Core Components of Robust MFA Systems
- Knowledge factors: Passwords or PINs, vulnerable to phishing.
- Possession factors: Authenticator apps like Google Authenticator or hardware keys such as YubiKey.
- Inherence factors: Fingerprint scanners or facial recognition via device processors.
Throughput in MFA verification hits sub-second latency on optimized cloud platforms, ensuring seamless user experience without sacrificing security.
Technical Deep Dive into MFA Protocols and Architectures
MFA mastery hinges on understanding protocols like TOTP (Time-based One-Time Password) and push notifications. TOTP generates codes via HMAC-SHA1 encryption, syncing client-server clocks with 30-second windows to thwart replay attacks.
FIDO2 architecture separates authentication from credential storage, using client-side public-key generation. This eliminates phishing risks, as challenges are signed with device-bound private keys stored in secure enclaves.
In 2026, hardware-backed MFA via TPM chips on processors achieves zero-knowledge proofs, minimizing server-side exposure. Bandwidth demands remain low—under 1KB per auth—while latency averages 200ms on 5G networks.
Advanced MFA Implementations
| Protocol | Encryption | Latency (ms) | Phishing Resistance |
|---|---|---|---|
| TOTP | HMAC-SHA1 | 50-100 | Medium |
| FIDO2 | ECDSA P-256 | 150-300 | High |
| WebAuthn | Public-Key | 200-400 | Very High |
Adopt these in enterprise settings for throughput exceeding 10,000 authentications per second per server cluster.
Real-World Case Studies: MFA Success and Failures
In 2024, Uber’s SMS-only MFA fell to a social engineering attack, compromising internal tools. Switching to hardware keys post-incident reduced unauthorized access attempts by 99%, per their security postmortem.
Contrast this with Okta’s 2022 breach, where legacy MFA bypassed via session hijacking exposed 366 customers. Lessons learned emphasize continuous session validation and adaptive risk engines using machine learning.
Common cyber threats in 2026 often target weak MFA; one study by Proofpoint found 43% of attacks exploit SMS vulnerabilities due to SIM-swapping.
Enterprise Wins with MFA Mastery
- Microsoft enforced phishing-resistant MFA across Azure AD, slashing account compromises by 60% in 2025.
- Google’s passkey rollout via Android’s Titan M2 processor achieved 100% phishing immunity in beta tests.
These cases highlight MFA’s role in essential cybersecurity best practices for 2026 protection.
Implementing Bulletproof MFA: Step-by-Step Guide
Start with assessment: Audit accounts using tools like Have I Been Pwned. Enable MFA on high-risk services—email, banking, VPNs—prioritizing FIDO2-compatible options.
Configure authenticator apps for TOTP, pairing with backup codes stored offline. For enterprises, deploy Okta or Duo with adaptive policies that escalate to biometrics on anomalous login locations.
Integrate via APIs: OAuth 2.0 with MFA extensions ensures protocol compliance. Test recovery flows to avoid lockouts, maintaining <1% failure rate.
Layered Defense Strategies
- Combine with password managers like Bitwarden for zero-trust access.
- Monitor via SIEM tools for anomaly detection, reducing mean time to respond.
- Detect and remove malware routinely, as it enables MFA prompt bombing.
MFA vs. Alternatives: Comprehensive Comparison
Passwordless authentication edges MFA in usability but requires ecosystem buy-in. Biometrics offer speed (under 100ms latency) yet falter on shared devices due to spoofing risks.
Hardware tokens like YubiKey 5 Series provide superior encryption via NFC and USB-C, outperforming app-based solutions in enterprise throughput.
Cisco’s recent access point flaws underscore the need for MFA in network gear alongside alternatives like certificate-based auth.
Pros and Cons Table
| Method | Pros | Cons | Best For |
|---|---|---|---|
| App-Based MFA | Free, ubiquitous | Phishing-prone | Consumers |
| Hardware Keys | Phishing-proof | Cost ($20-50) | Professionals |
| Passkeys | Seamless sync | Device-bound | Mobile-first |
2026 Trends and Future-Proofing Your MFA Strategy
Passkeys dominate 2026, with Apple’s iCloud Keychain and Google’s ecosystem driving 70% adoption per Gartner forecasts. Quantum-resistant algorithms like Kyber integrate into FIDO3 drafts, future-proofing against harvest-now-decrypt-later attacks.
AI-driven behavioral biometrics analyze keystroke dynamics and device sensors, boosting accuracy to 99.7% without user friction. Edge computing reduces cloud dependency, cutting latency by 40%.
“By 2027, 80% of enterprises will phase out passwords entirely,” predicts Forrester analyst Eve Alston.
Prepare by piloting hybrid frameworks blending machine learning with hardware roots of trust.
Conclusion: Achieve MFA Mastery Today
Bulletproof your accounts with MFA mastery: audit, implement phishing-resistant methods, and layer defenses. Key takeaways include prioritizing FIDO2, monitoring for bypasses, and staying ahead of trends like passkeys.
Act now—enable MFA on your top three accounts. For deeper dives into threats, explore Cisco’s AI infrastructure push, which bolsters secure auth in data centers. Secure your digital life in 2026.



