 Enterprise Technology
Enterprise Technology
Master Networking & Cybersecurity
Explore in-depth tutorials, latest industry trends, and expert insights to advance your IT career. Join thousands learning networking technologies.
7000+
Articles
1.2M+
Monthly Readers
100%
Free Content
Featured Article

AI-Driven Network Security 2026: Trends and Strategies
Discover how AI-driven network security detects threats 60% faster in 2026, with case studies, stats, and implementation steps for unbreakable defenses.
Trending Now
Latest industry trends and high-impact updates
 Enterprise Technology
Enterprise TechnologyWhen Your Digital Clone Can Hack the Network: AI Avatar Security Risks
 AI
AIHow Robotics and Secure Networking Are Feeding San Francisco’s Most Vulnerable
 Enterprise Technology
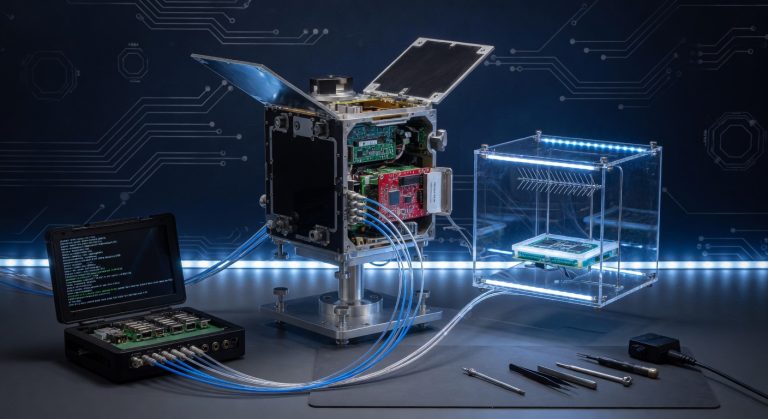
Enterprise TechnologyRed Hat extends open source technology into space
 Mobile Threat Defense
Mobile Threat DefenseZimperium Mobile App Response Agent helps security teams counter mobile attacks
 Cybersecurity
CybersecurityPoor security left hackers inside water company network for nearly two years
Browse Categories
Find content that matches your interests
Networking
Deep-dive guides for CCNA, routing, switching, and more

How to Build Edge Network: Complete 2026 Guide
Master building edge networks with step-by-step instructions, case studies, and 2026 stats. Reduce latency by 60% and scale for IoT success.
Why Networking Companies Need a Logo That Communicates Technical Reliability
Expert guide to logo design for networking and IT companies covering trust signals, color psychology, and vendor examples.

How Delay Metrics Dictate Traffic Flow in Modern Networks
Delay metrics determine traffic flow more than bandwidth in modern networks—here’s how to configure them correctly in 2026 environments.
Editors Picks
Hand-picked articles selected by our editorial team

Back Casting Room: Complete Guide to What It Is, How It Works, and Why It Matters in 2026
Whether you first heard this term in a business strategy meeting, a film production discussion, or an online forum, "back casting room" means something different depending on who is using it — and that confusion is exactly why most articles on this topic fail to actually help you. This guide cover

Node.js Outsourсing vs. In-House Team: What’s the Real Tradeoff?
Building a Node.js product involves choosing between outsourcing and an in-house team, each with unique benefits and challenges. In-house teams offer direct control and deep system knowledge but require lengthy recruitment. Outsourcing enables quick expertise access and speed but involves coordination with external partners.
What Stops AI Models From Working Reliably in Real Systems
AI models often excel in training but falter in production due to data drift, infrastructure dependencies, and versioning issues. This gap highlights the need for robust monitoring and MLOps practices. Teams can ensure reliability by addressing these real-world challenges effectively.
Latest Reviews
In-depth product & tech reviews from our editorial team
Latest News
Breaking tech news, security alerts, and industry updates

OpenAI Adds Lockdown Mode to ChatGPT Enterprise to Enhance Data Security
OpenAI introduced 'Lockdown Mode' for ChatGPT Enterprise, limiting external tools to prevent data exfiltration. This feature enhances security...

AI Agent Finds 21 FFmpeg Zero-Days; Chrome Patches Record 429 Bugs
An AI agent uncovered 21 zero-day vulnerabilities in the FFmpeg multimedia library. Meanwhile, Google issued a Chrome update...

I use these 10 secret Netflix codes to find hidden movies – here's how to enter them
A Netflix user has detailed a method using 10 specific codes to access hidden movies on the platform,...

MuddyWater Deploys DLL Side-Loading in 9-Country Espionage Campaign
Iranian hackers MuddyWater target governments and critical sectors using DLL side-loading in a new cyberespionage campaign.

AI Chatbots Direct Users to Cryptojacking Malware Sites
AI chatbots are reportedly directing users to websites that install cryptojacking malware, exploiting retrieval-augmented generation systems. This leads...

JINX-0164 Malware Targets Crypto Firms via Fake Recruiters
A new macOS malware campaign, JINX-0164, is attacking cryptocurrency companies using fake recruiter lures. The operation distributes custom...
Job Opportunities
Browse verified job listings across tech, marketing, design and more

Cybersecurity News Writer – Weekly Roundup (Remote) at Help Net Security
Cybersecurity News Writer Opportunity at Help Net Security The cybersecurity landscape evolves at breakneck speed, and…
Dashlane Addresses Brute-Force Attack Impacting User Accounts A recent security incident at Dashlane, a prominent password…

Let’s Encrypt Post-Quantum Cryptography Developer Role
Let’s Encrypt Advances Post-Quantum Certificates with Merkle Tree Technology Let’s Encrypt, a leading certificate authority providing…
Urgent Security Advisory: Cisco SD-WAN 0-Day Vulnerability Exploited About the Role This article reports on a…
Unpacking the Anthropic Report: AI’s Role in Modern Cyberattacks The landscape of cybersecurity is ever-evolving, and…

Cybersecurity Event Insights: Infosecurity Europe 2026 Overview
## Reporting on the Infosecurity Europe 2026 Event: A Glimpse into Cybersecurity Careers The cybersecurity landscape…











