Search Results
Showing results for "seo" (616 articles found)

CISA Adds Actively Exploited Linux Root Access Bug CVE-2026-31431 to KEV
CISA Adds Linux Root Access Bug CVE-2026-31431 to KEV Catalog The U.S. Cybersecurity and Infrastructure Security Agency added CVE-2026-31431, an actively exploited Linux vulnerability that allows root access, to its Known Exploited Vulnerabilities catalog on May 1, 2026. This inclusion requires federal civilian executive branch agencies to apply mitigation measures by May 22, 2026. The...

The Race Is on to Keep AI Agents From Running Wild With Your Credit Cards
AI agents may soon be buying your stuff for you. The FIDO Alliance has teamed up with Google and Mastercard to try to ensure that shopping in the near future isn't a complete disaster.

Why Sharing a Screenshot Can Get You Jailed in the UAE
The war in Iran has drawn attention to arrests in the United Arab Emirates over online content, but the legal framework behind that enforcement has existed for years.

90,000 Screenshots of One Celebrity's Phone Were Exposed Online
Spyware appears to have captured everything from intimate photos to private messages from the smartphone of European celebrity. They were publicly accessible until a researcher flagged the exposure.

OpenAI Rolls Out ‘Advanced’ Security Mode for At-Risk Accounts
OpenAI is rolling out Advanced Account Security for people concerned that their ChatGPT or Codex accounts could be potential targets of phishing attacks.

Dangerous New Linux Exploit Gives Attackers Root Access to Countless Computers
The exploit, dubbed CopyFail and tracked as CVE-2026-31431, allows hackers to take over PCs and data center servers. The Linux vulnerabilities have been patched—but many machines remain at risk.
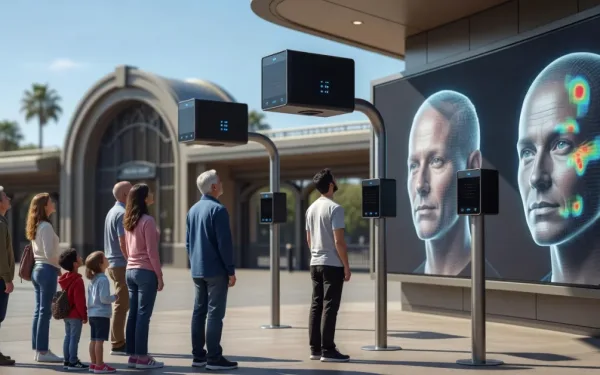
Disneyland Now Uses Face Recognition on Visitors
Plus: The NSA tests Anthropic’s Mythos Preview to find vulnerabilities, a Finnish teen is charged over the Scattered Spider hacking spree, and more.

Mexican Surveillance Company
Grupo Seguritech is a Mexican surveillance company that is expanding into the US.

ICE Uses Graphite Spyware
ICE has admitted that it uses spyware from the Israeli company Graphite.

FBI Extracts Deleted Signal Messages from iPhone Notification Database
404 Media reports (alternate site): The FBI was able to forensically extract copies of incoming Signal messages from a defendant’s iPhone, even after the app was deleted, because copies of the content were saved in the device’s push notification database…. The news shows how forensic extraction—when someone has physical access to a device and is able to run specialized software…