Search Results
Showing results for "seo" (616 articles found)
Hiding Bluetooth Trackers in Mail
It was used to track a Dutch naval ship: Dutch journalist Just Vervaart, working for regional media network Omroep Gelderland, followed the directions posted on the Dutch government website and mailed a postcard with a hidden tracker inside. Because of this, they were able to track the ship for about a day, watching it sail from Heraklion, Crete, before it…

Anti-DDoS Firm Heaped Attacks on Brazilian ISPs
Anti-DDoS Firm Heaped Attacks on Brazilian ISPs An anti-DDoS protection company launched distributed denial-of-service attacks against multiple internet service providers in Brazil, according to reports from cybersecurity researchers. The firm, which offers services to block such attacks for clients, directed traffic floods at Brazilian ISPs over several days last week. Researchers tracked the activity to...

New Python Backdoor Uses Tunneling Service to Steal Browser and Cloud Credentials
New Python Backdoor Uses Tunneling Service to Steal Browser and Cloud Credentials Security researchers have identified a new Python-based backdoor that employs a tunneling service to exfiltrate browser credentials and cloud storage data from infected systems. The malware, detected in recent weeks, targets sensitive information stored in popular browsers and services like Google Drive and...

Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft
Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft Malicious packages in RubyGems and Go module repositories have targeted continuous integration pipelines to steal developer credentials, security researchers report. The attack campaign, active since early 2025, has affected multiple open-source projects by injecting code that exfiltrates secrets from CI environments. Attack Mechanics...

Two Cybersecurity Professionals Get 4-Year Sentences in BlackCat Ransomware Attacks
Two Cybersecurity Professionals Get 4-Year Sentences in BlackCat Ransomware Attacks A federal court sentenced two cybersecurity professionals to four-year prison terms for their roles in BlackCat ransomware attacks that targeted multiple organizations. Key Details The individuals, who worked in the cybersecurity field, received their sentences following convictions tied to the BlackCat ransomware group. BlackCat, also...

China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists
China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists China-linked hackers have targeted governments in Asia, a NATO member state, journalists, and activists in a series of cyber operations detected in recent months. Cybersecurity firms report the attacks aimed to steal sensitive data and monitor dissent, with operations linked to groups backed by Beijing....

Friday Squid Blogging: How Squid Survived Extinction Events
Science news: Scientists have finally cracked a long-standing mystery about squid and cuttlefish evolution by analyzing newly sequenced genomes alongside global datasets. The research reveals that these bizarre, intelligent creatures likely originated deep in the ocean over 100 million years ago, surviving mass extinction events by retreating into oxygen-rich deep-sea refuges. For millions of years, their evolution barely changed—until a…

Medieval Encrypted Letter Decoded
Sent by a Spanish diplomat. Apparently people have been working on it since it was rediscovered in 1860.

What Anthropic’s Mythos Means for the Future of Cybersecurity
Two weeks ago, Anthropic announced that its new model, Claude Mythos Preview, can autonomously find and weaponize software vulnerabilities, turning them into working exploits without expert guidance. These were vulnerabilities in key software like operating systems and internet infrastructure that thousands of software developers working on those systems failed to find. This capability will have major security implications, compromising the…
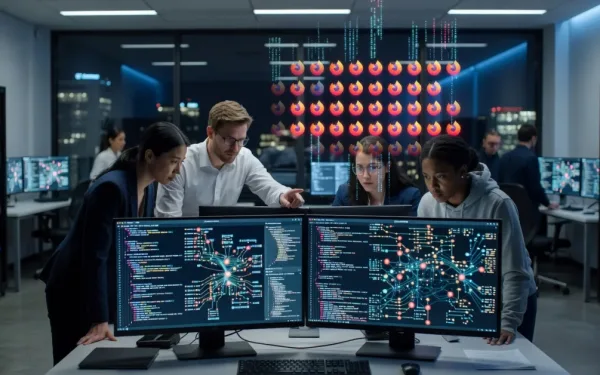
Claude Mythos Has Found 271 Zero-Days in Firefox
That’s a lot. No, it’s an extraordinary number: Since February, the Firefox team has been working around the clock using frontier AI models to find and fix latent security vulnerabilities in the browser. We wrote previously about our collaboration with Anthropic to scan Firefox with Opus 4.6, which led to fixes for 22 security-sensitive bugs in Firefox 148. As part…