Access Control Lists (ACLs) are fundamental to network security and traffic management in Cisco environments. However, misconfigurations can lead to ACL errors, blocking legitimate traffic or allowing unauthorized access. This article explores common ACL errors with examples, focusing on troubleshooting techniques using show commands. Understanding these errors is crucial for passing certification exams and excelling in real-world networking roles.
ACL Error – Example 1
In the figure, host 192.168.2.2 has no HTTP or HTTPS access with 192.168.4.2. When entering the show access-lists command, matches are shown for the first deny statement, which indicates that traffic has matched this statement.
Now, look at the order of the entries. Host 192.168.2.2 has no connectivity with 192.168.4.2 because of the rule process ID 10 order in the access list. When the router processes ACLs from the top to down, statement 10 denies host 192.168.2.2 for TCP traffic, so statement 20 can never be matched. Statements 10 and 20 should be reversed. The third line allows all other non-TCP traffic under IP, such as ICMP, UDP, etc.
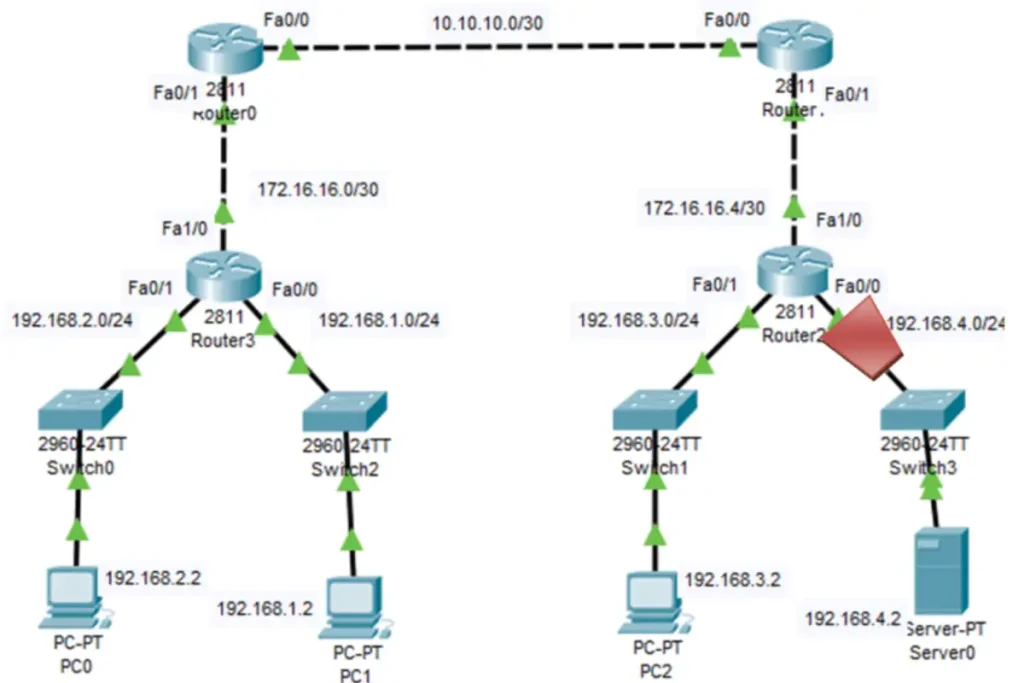
Extended IP access list 101 10 deny tcp 192.168.2.0 0.0.0.255 any 20 permit tcp 192.168.2.0 0.0.0.255 host 192.168.4.2 eq www 30 permit ip any any
ACL Errors – Example 2
The network 192.168.2.0/24 cannot use TFTP to connect to the 192.168.4.2 server.
The 192.168.2.0/24 network cannot use TFTP to connect to 192.168.4.2 because TFTP uses UDP. However, when we use the show access-list command, the statement has no permit entry for UDP traffic.
The access list allows all other TCP traffic, and UDP is implicitly denied. The implied deny any statement does not appear in the show access-lists output, so matches are not shown. The third statement must be changed to ip any any instead of tcp any any.
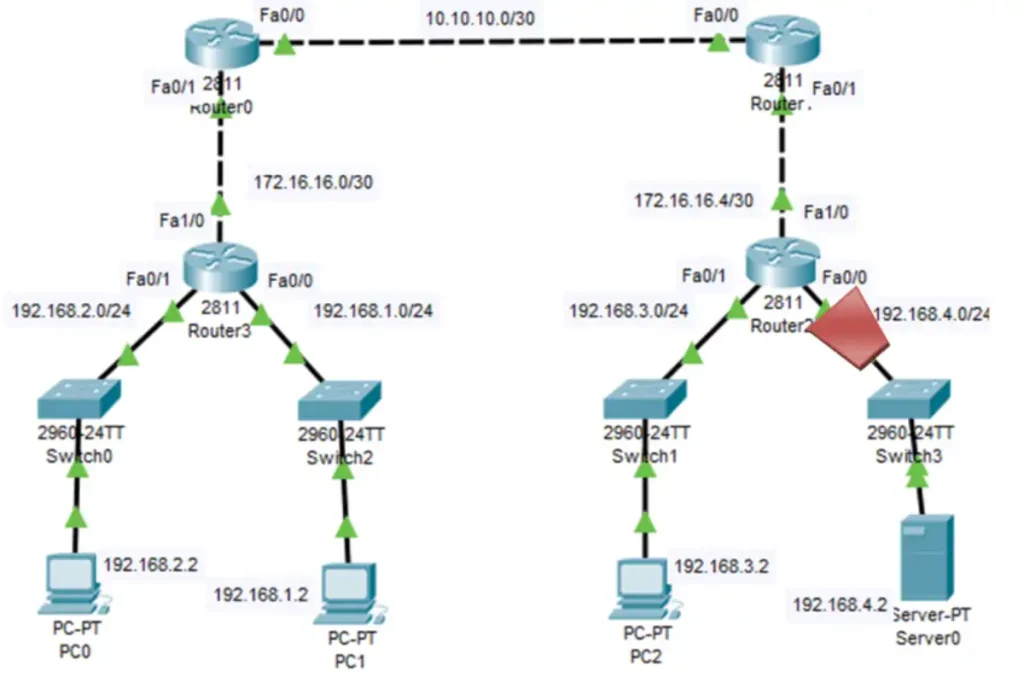
R2#show access-lists Extended IP access list 101 10 permit tcp 10.10.10.0 0.0.0.255 host 192.168.4.29 eq www (6 match(es)) 20 deny tcp 192.168.2.0 0.0.0.255 any 30 permit tcp any any R2#
ACL Errors – Example 3
In the topology in the figure, the 192.168.1.0/24 network can use Telnet to connect to 192.168.4.0/24, but this is not according to policy; this connection should not be allowed. The results of the show access-lists command show that the permit statement has been matched.
The 192.168.1.0/24 network can use Telnet because the Telnet port number in statement 10 of access-list 101 is listed incorrectly in the ACL statement.
It currently denies any source packet with a port number equal to Telnet. To deny Telnet traffic inbound on fa0/0, we need to deny the destination port number equal to Telnet. For example, deny TCP or any eq telnet.
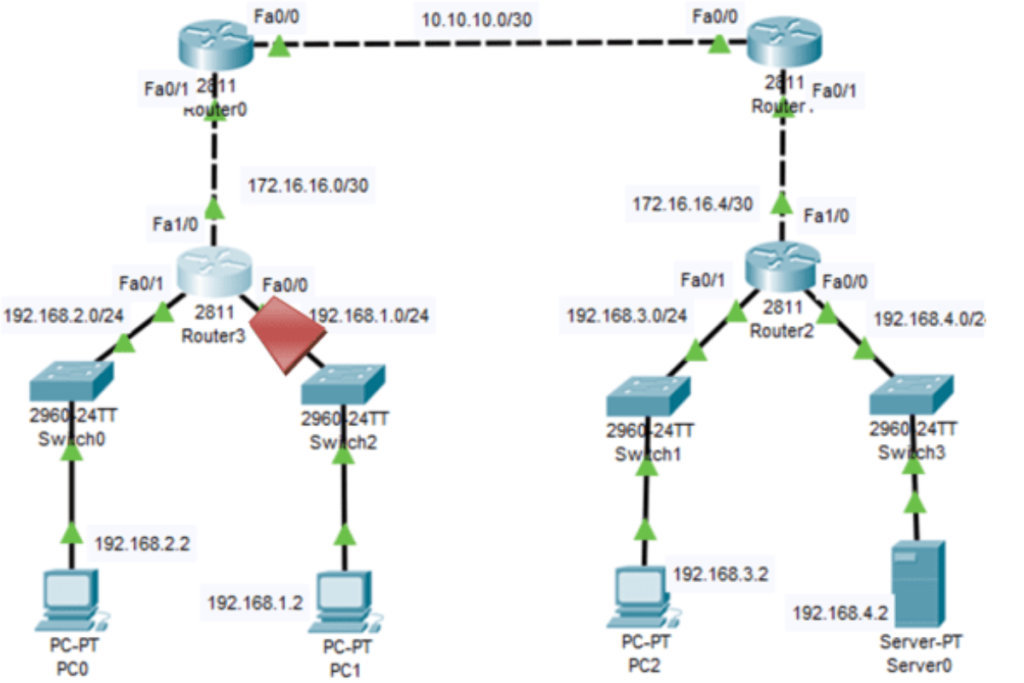
R3#show access-lists Extended IP access list 103 10 deny tcp any eq telnet any 20 deny tcp 192.168.1.0 0.0.0.255 192.168.4.0 0.0.0.255 eq www 30 permit tcp any any (162 match(es)) R3#
Common Misconfigurations
- Missing
permit ip any anyat the end, leading to implicit deny. - Applying ACL to the wrong interface direction (inbound vs. outbound).
- Overlapping IP ranges causing unintended blocks.
Lab Exercise
Configure an ACL to allow HTTP from 192.168.1.0/24 to 192.168.2.0/24:
- Create ACL:
access-list 101 permit tcp 192.168.1.0 0.0.0.255 192.168.2.0 0.0.0.255 eq www - Apply to interface:
ip access-group 101 in - Test with
pingandtelnetfrom a client.
Troubleshooting ACLs with Packet Captures
Use Wireshark to capture traffic and correlate it with ACL rules. Apply a capture filter (e.g., host 192.168.2.2) to identify dropped packets, then adjust the ACL accordingly.
Common ACL Misconfigurations Checklist
- Verify ACE order and placement.
- Check protocol and port numbers.
- Ensure explicit permits for required traffic.
- Test with
pingortelnetafter changes.
Conclusion
Mastering ACL errors is essential for certification and effective network management. Practice with show commands, verify ACL order, and test configurations in a lab environment. Explore more Cisco networking topics to enhance your skills!
FAQs
What causes ACL errors in Cisco routers?
ACL errors in Cisco routers often stem from incorrect ACE order, wrong port numbers, or missing permits. Use show access-lists to identify issues, crucial for troubleshooting.
How can I troubleshoot ACL misconfigurations?
Troubleshoot ACLs with show access-lists to check matches, verify direction via show running-config, and test traffic. Essential to master network diagnostics.
Why does ACL order affect network traffic?
ACL order matters as Cisco routers process rules top-down; a higher deny blocks permits below it. Reversing statements like 10 and 20 fixes connectivity.
How do I allow UDP traffic in an ACL?
To allow UDP, add a specific permit (e.g., permit udp 192.168.2.0 0.0.0.255 eq tftp). Avoid ip any any for security