Imran Khan
Cybersecurity specialist and certified ethical hacker (CEH). Focuses on penetration testing methodologies and network vulnerability assessments. Contributed 280+ articles on intrusion detection systems and firewall configurations for NetworkUstad.
Pentesting Is More Than a List of Found Vulnerabilities
Pentesting offers more than a simple list of vulnerabilities; it simulates real attacks to reveal exploitable weaknesses and their business impacts. Effective reports detail attack scenarios, exploitation conditions, potential losses, and prioritized action plans. This approach helps organizations focus on truly critical risks, enabling smarter investments in security.

How to Get a Cybersecurity Job in 2026: A Practical Roadmap
The cybersecurity field faces a widening talent gap, making 2026 an ideal time to enter or advance. Employers prioritize cloud security, IAM, and awareness of AI-driven threats alongside foundational skills. Build a mix of certifications like CompTIA Security+ and hands-on experience to stand out in applications.

Why Subcontractors Are the Weakest Link in DoD Cybersecurity Compliance
Most defense supply chain breaches originate at the subcontractor level, not with prime contractors. CMMC compliance requirements flow down to every organization handling Federal Contract Information or Controlled Unclassified Information. Prime contractors now require subcontractors to demonstrate certification to participate in programs.

How to Choose a Website to View Instagram Stories Without Compromising Your Account
Instagram Stories expose your username to viewers, driving demand for anonymous viewing tools. However, many websites pose security threats by requesting logins or downloads. This guide helps you spot red flags and select a reliable Instagram story viewer to stay safe.

Intel aims advanced Xeon 6+ at AI edge computing
Introduction: Revolutionizing AI at the Edge with Intel’s Latest Innovation In 2026, as artificial intelligence continues to permeate every aspect of business and daily life, the demand for efficient edge computing solutions has skyrocketed. Intel’s advanced Xeon 6+ processor emerges as a game-changer, specifically targeting AI edge computing challenges like real-time data processing and low-latency...
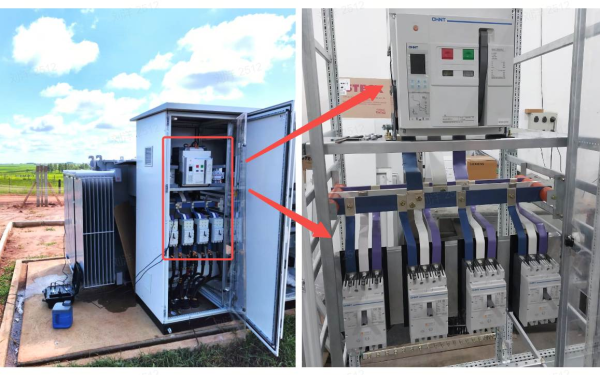
Voltage Surge Protection for Smart Homes and Offices: Applying Surge Protective Device Basics to Modern Power Distribution
If your home or office depends on smart lighting, Wi-Fi, security cameras, energy monitoring, or automated controls, you have a hidden risk: voltage surges can quietly damage sensitive electronics long before you notice a failure. That creates three common headaches for you: confusing choices when you try to “add surge protection,” worry about electrical safety...

Top Benefits of Vehicle Wraps for Walnut Creek Businesses
Vehicle wraps offer Walnut Creek businesses a high-impact way to build brand awareness without a massive monthly price tag. The top benefits include cost-effective local advertising, protection for your car’s paint, and a professional look that builds trust with customers. Unlike digital ads that disappear when you stop paying, a wrap works for you 24/7...

Best Time to Visit Australia from India – A Comprehensive Travel Guide
Australia’s seasons run opposite to India’s due to its Southern Hemisphere location, making it a year-round destination for Indian travelers. Understanding the varying climates helps ensure a comfortable trip with proper planning for activities and accommodation. Why Timing Matters for Your Australia Trip Australia spans a continent with diverse weather—from Sydney’s mild coasts to the...

How Precision Gear Replacement in 5-7 Days Can Secure Your Industrial Network Against Costly Downtime
In the era of Industry 4.0, manufacturing equipment is deeply integrated with network systems, where a single component failure — such as a lathe gear — can trigger cascading disruptions. Costly downtime often exceeds thousands of dollars per hour, while simultaneous cybersecurity vulnerabilities may emerge from impaired data flows. Traditional gear replacement cycles of 4–8...
Connect Automation: Bridging Devices, Data, and Decision-making in Industrial Environments
Industries across the globe are undergoing rapid transformation as technology redefines how operations are managed and optimized. This shift is driving organizations to rethink processes, improve efficiency, and safeguard long-term resilience. Modern systems are no longer isolated; instead, they are designed to function in harmony, ensuring seamless communication and reliable performance. At the center of...