
How Monthly AC Rentals Can Fit Your Budget While Offering Cool Comfort
Delhi NCR is a place that faces extreme weather, with summers being too hot most of the time. Although an air conditioner is necessary, it is not always possible to buy one outright. The steep initial cost, installation fee, and maintenance over time can run up a substantial amount. That is where AC rental monthly steps in as an easy and cost-effective solution. Why It Makes Sense to Rent an AC on a Monthly Basis Selecting an AC on rent monthly basis in Delhi NCR is a financial convenience without compromising comfort. If you are a student, a working professional,…
Why Moviezrules Is Unsafe in 2025: Updated Risks, Fines & Top Legal Alternatives
In the ever-evolving landscape of online streaming, sites like Moviezrules promise free access to the latest movies and TV shows. But what seems like a convenient shortcut often leads to serious pitfalls. According to a 2025 Alliance for Creativity and Entertainment (ACE) study, consumers are up to 65 times more likely to encounter malware on piracy sites compared to legitimate platforms. This surge in threats, driven by advanced cyber tactics, makes Moviezrules not just illegal but a direct risk to your devices, data, and finances. In this updated guide for November 2025, we dive into the latest domain shifts, emerging…
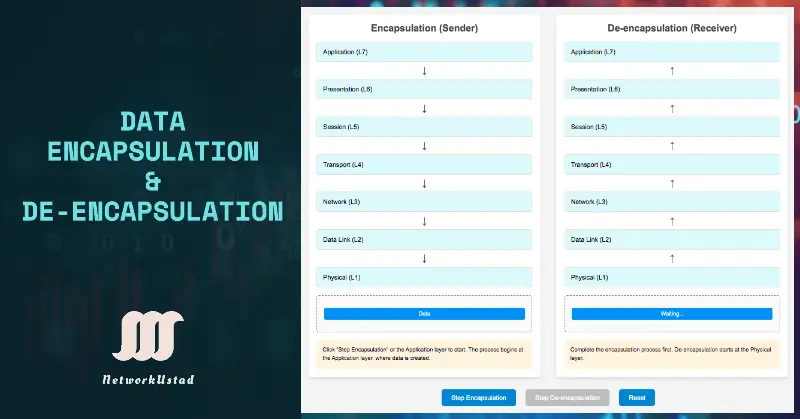
Understanding Data Encapsulation and Decapsulation in OSI Layers: A Comprehensive Guide With Simulator Updated 2025
Data encapsulation and de-encapsulation are crucial for transmitting information across computer networks. Encapsulation involves wrapping data in a specific format before sending it over the network, ensuring it can traverse various communication mediums and reach its destination intact. On the other hand, de-encapsulation is the process of unwrapping and extracting the original data at the receiving end. These processes are pivotal in maintaining data integrity, enhancing efficiency, and facilitating seamless communication within complex network architectures. Furthermore, in this exploration, we delve into the intricacies of data encapsulation and de-encapsulation to unravel their significance in networking. Data Encapsulation In the previous…

What Affects Bitcoin Price the Most? 7 Key Factors Explained
Bitcoin is known for its price volatility, and while some see this as a risk, others view it as an opportunity. But what drives the ups and downs of the world’s most famous cryptocurrency? Understanding the main Bitcoin price drivers can help both beginners and experienced investors make more informed decisions. From macroeconomic forces to crypto-specific events, here are seven key factors that have the most impact on Bitcoin’s price. 1. Supply and Demand At its core, Bitcoin follows the classic rules of supply and demand. With a fixed supply of 21 million coins, scarcity plays a significant role in price movement. When…

Why First-Time Buyers Keep Choosing Mini Dab Rigs Over Full-Size Options
The cannabis accessory space is changing quickly, with new users driving demand for gear that’s simple, portable, and budget-friendly. One clear trend is emerging: more first-time buyers are gravitating toward compact setups instead of traditional full-size rigs. For those just getting started, a mini dab rig offers the right mix of ease and efficiency. Tucked easily into a backpack or small living space, it fits the pace of everyday life without overcomplicating things. The appeal is clear—less gear to manage, faster setup, and a smoother way to explore concentrates without the intimidation of a full-sized setup. Size Matters More Than…
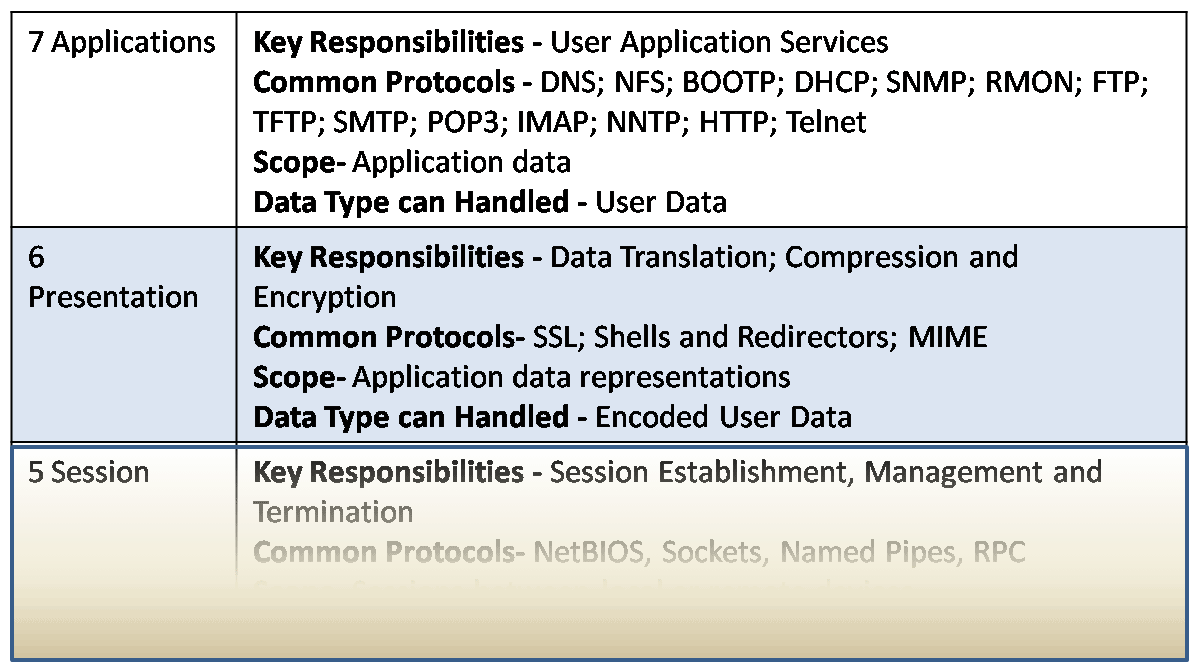
OSI Model, including its 7 Layer Introduction
As the importance of computers grows, vendors recognize the need for networking with them. They produced a variety of protocols whose specifications were not made public. Hence, each vendor had different ways of networking computers, and these ways were not compatible with each other. This means that the computers of one vendor could not be networked with another vendor’s computers. Slowly, these specifications were made public, and some inter-vendor compatibility was created, but this still represented too many complications. To resolve this compatibility issue, the OSI model was introduced. OSI Model In 1977, the International Organization for Standardization (ISO) started…
Networking Essentials: Spotlight on the 6 Types of Network
We can characterize 6 types of networks with the size of the area covered, the number of users connected, the number and types of services available, and the area of responsibility. The most important and famous kinds of networks are: Local Area Network (LAN) It is the first and most important part of networks. It provides access to users and end devices in a small geographical area, such as a home network, a small business network, or a network in the same building. The following are the key points for LANs:- Key Characteristics Examples: Home networks, office workstations, school labs….

Jilo Virals Exposed: Facts, Phishing Risks, Safety Tips, Legal Implications, and 2026 Updates
In 2021 and 2022, the term “Jilo Virals” exploded across the internet, driven by its association with pirated streaming of Spider-Man: No Way Home. This viral phenomenon sparked curiosity, controversy, and significant cybersecurity concerns. Was Jilo Virals a legitimate streaming platform, a phishing scam, or something else entirely? This comprehensive guide uncovers the truth about Jilo Virals, exploring its origins, phishing risks, safety tips, legal implications, and what’s changed in 2026. Whether you’re a movie fan, a cybersecurity enthusiast, or simply curious, this article provides everything you need to know to stay informed and safe. What is Jilo Virals? Jilo…
What is a Network? – Exclusive Definitions
Before starting Cisco Internetworking, the network introduction is important for the networking student to be aware of “what a network is” and “what network is importance themselves”. So, first of all, what is a network? In simple words, It is a collection of interconnected devices (such as computers, printers, etc.) in such a way that they can communicate with each other. To better understand, let us look at the example of how things worked before networks. For this, suppose a large international company that sells ABC products at a time when networks did not exist. Let us call this company XYZ…
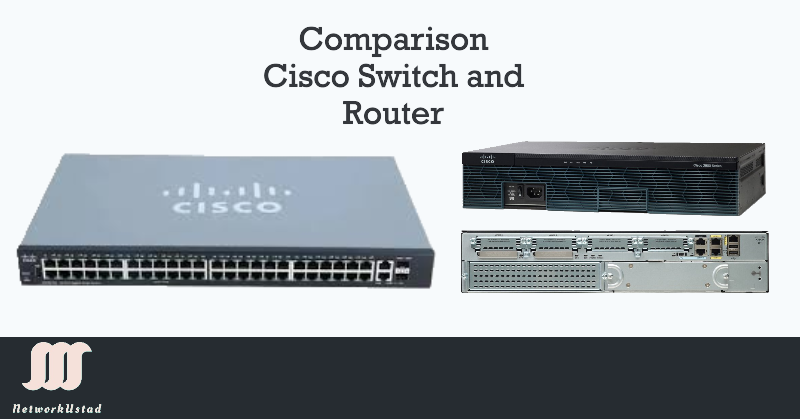
Comparing Switch and Router: A Comprehensive Guide
The Switch and Router comparison is most important because both are the backbone devices in computer networking. So, I am comparing Switches and Routers for networking students. If someone understands the Switch and Router comparison, he can easily manage a network. Definition of Router A router is a Layer 3 (Network Layer) device that forwards data packets between distinct networks. Routers determine the optimal path for data transmission using a routing table and the destination IP address in packets. They operate with routable protocols like TCP/IP, which are essential for connecting local networks to the internet (WAN). Routers perform advanced functions such as Network…

3 Basic Network Component – Exclusive explanation
Any network infrastructure contains three components: devices, Media, and Services. Moving data from source to destination can be as simple as connecting one device to another. Note:- At the end of this article, the assessment test is waiting for you about the Basic network Components Devices and media are the physical network components, also known as Hardware network components. We can touch or take some physical place, such as the PC, switch, router, wireless access point, or the cabling used to connect the devices. Services include many typical network applications people use daily, like email and web hosting services. Additionally,…

20 Most Destructive Viruses History in the World
A computer virus is a program, script, or macro created to harm a computer, steal private information, change data, send e-mail, and display messages. More importantly, when the viruses were executed, they spread bycopying itself into or over the following:- Virus writers use detailed knowledge of security vulnerabilities to gain access to a host’s computer. When was the term “Virus” First Used The theory of a computer program capable of reproducing itself was first mentioned by John von Neumann in his 1949 “Theory of self-reproducing automata” essay. First computer virus ever created. How to protect your computer from viruses Anti-virus software is the solution to protect…

Toys for Kids: Tips for Buying
When buying toys for kids, you need to consider what your child is likely to enjoy the most. Your child may love technology, but they are still developing skills that will last a lifetime. Action figures are a perfect choice for this age group. Many come with accessories and vehicles. Your child will love playing pretend. Action figures can also be great for teaching children about the world and science. This year, top toys for kids include a Polly Pocket set. It comes with over 20 accessories. These include life-size 3D glasses, a movie theater set, a phone, and 12…

The Evolution of Peer-to-Peer Communication in the Digital Age
Peer-to-peer communication has changed the way people share, connect, and collaborate. It removes the need for central authorities. Users speak directly with each other. Over the past decades, peer-to-peer, or P2P, has evolved from basic data exchange to complex, real-time systems. It has shaped messaging, file sharing, online conferencing, and more. This article comprehensively and structuredly explains the development of P2P communication. It covers key milestones, technical approaches, social impacts, and security implications. Each section is designed to deliver depth while remaining easy to read. The Origin of Peer-to-Peer Communication Principles From Local Networks to Global Sharing P2P communication began…
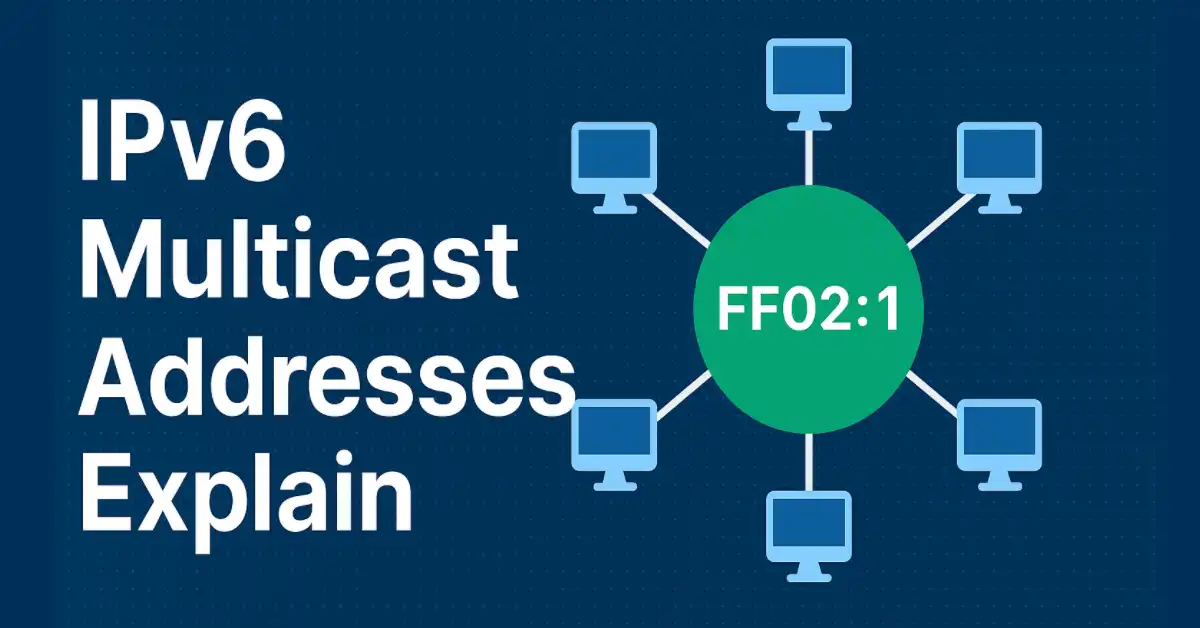
IPv6 Multicast Addresses Explained: Structure, Types, Examples, and Use Cases
I have already written about IPv6 multicast addresses in my previous article. IPv6 multicast addresses work similarly to IPv4 multicast addresses. IPv6-enabled devices can join and listen for multicast traffic on an IPv6 multicast address. Multicasting is one of the powerful features of IPv6 addresses, which enables one-to-many communication, optimizing bandwidth for applications like video streaming, IoT, and network discovery protocols. This article provides a comprehensive guide to IPv6 multicast addresses, covering their structure, types, practical examples, and real-world use cases. Whether you’re a CCNA/CCNP candidate, a network engineer, or an enthusiast, this guide will help you with the knowledge…