Cybersecurity
What is Malware and Malicious Software? (Updated 2025)
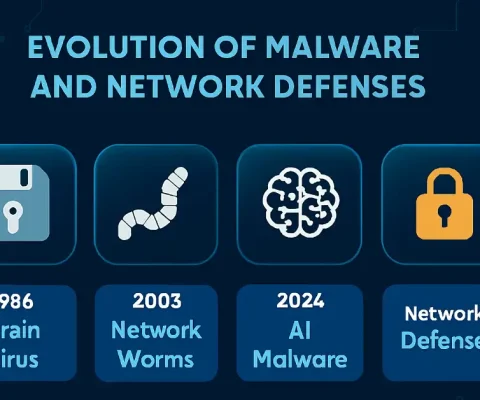
Updated: October 19, 2025—Includes latest threats and network defenses. Malware, or malicious software, is a program or file designed to disturb computer processes and operations or gain unauthorized entry to the computer system, often via network protocols like RDP or SMB, without the user’s knowledge or permission. Malware has become a common term for all...

Thwarting Cybercriminals: Master Key Measures and Strategies for Cybersecurity Enthusiasts in 2025
As a cybersecurity and networking expert with extensive experience in securing enterprise environments, I’ve seen firsthand how cybercriminals evolve their tactics. Thwarting cybercriminals isn’t easy, but companies, governments, and organizations are taking proactive steps to limit and discourage these threats. In this article, we’ll explore key actions and measures, updated for 2025, with practical insights...

Cyber Security Threats and Defenses: A Comprehensive Guide for 2025
Cyber security threats are a growing concern worldwide, escalating with AI and ransomware in 2025. Individuals and organizations rely on networks, making intrusions devastating. Computer networks are necessary for everyday activities, and both individuals and organizations depend on their computers and networks. Intrusion to these computers by an illegal person can result in a network...
What is VLAN Attacks – Brief Explanation
In the previous article, I explained how trunks work. By default, trunk ports can use all VLANs and pass traffic for multiple VLANs across the same physical link between switches. The VLAN simplifies network administration and maintenance. It also improves the performance of the network, but it has some backhaul for hackers which is necessary...