Cybersecurity
Welcome to NetworkUstad’s Cybersecurity Hub – your comprehensive resource for staying secure in an increasingly connected world. In today’s digital landscape, cyber threats evolve faster than ever. From sophisticated ransomware attacks to simple phishing scams, businesses and individuals face constant risks. Our cybersecurity section delivers practical, actionable insights to help you build robust defenses and protect what matters most. Whether you’re a security professional, IT administrator, business owner, or someone concerned about digital privacy, you’ll find expert guidance covering everything from fundamental security principles to advanced threat protection strategies. What You’ll Discover: 🔐 Security Fundamentals – Master the CIA Triad, understand information security basics, and build a strong foundation in cybersecurity principles. 🛡️ Threat Intelligence – Learn about different attack vectors, hacker types, malware categories, and emerging cyber threats targeting organizations worldwide. 🔒 Protection Strategies – Explore practical defense mechanisms including encryption, multi-factor authentication, network security, endpoint protection, and access controls. 📊 Compliance & Governance – Navigate regulatory requirements like GDPR, HIPAA, PCI DSS, and industry frameworks such as NIST and ISO 27001. ⚡ Incident Response – Prepare for the inevitable with comprehensive guides on breach detection, containment, recovery, and forensic analysis. 🚀 Emerging Technologies – Stay ahead with insights on AI security, cloud protection, IoT vulnerabilities, blockchain security, and quantum computing threats. 💼 Enterprise Security – Discover strategies for securing hybrid workforces, protecting corporate data, managing third-party risks, and building security-aware cultures. 🎓 Career Development – Explore ethical hacking careers, certification paths (CEH, CISSP, OSCP), and skill development resources. Our articles combine technical depth with practical applicability. We break down complex security concepts into digestible insights, provide real-world examples, and offer step-by-step implementation guides. No unnecessary jargon—just clear, actionable cybersecurity knowledge you can use immediately. From understanding basic threats to implementing enterprise-grade security architectures, NetworkUstad’s cybersecurity content empowers you to make informed decisions and take meaningful action. We cover the full spectrum: network security, application security, data protection, cloud security, mobile security, and everything in between. Security isn’t a one-time project—it’s an ongoing journey. Join thousands of readers who trust NetworkUstad to keep them informed about the latest threats, best practices, and innovative solutions in cybersecurity. Protect your network. Secure your future. Start exploring our cybersecurity resources today.

Rotating Proxies: Enhancing Online Anonymity and Efficiency
In the digital age, the ability to remain anonymous and access the internet without restrictions has become a priority for many users and businesses. This is where the concept of rotating proxies comes into play, offering a sophisticated solution to these needs. A proxy acts as an intermediary between a user’s device and the internet,...

Building Blocks of Cybersecurity: Why IT Infrastructure Security Matters
The Importance of IT Infrastructure Security You know how important it is to keep your physical home secure, right? You lock your doors and windows, maybe even have an alarm system. Well, the same goes for your digital home. Your IT infrastructure security is just as crucial to protect. After all, it houses everything from...

Zero Trust Security Model – Exploring Its Principles
Online threats constantly evolve, mounting attacks on IT and hacking into systems. From these threats, no firewall can give us total protection. Complex risks today are more complicated in terms of their dangers. The Zero Trust Security Model does not assume that all threats to safety exist on the network itself. It takes a proactive...

Cyber-Smart: Integrating Cybersecurity into Tech Education
In today’s digital world, cybersecurity is more important than ever. As technology advances at an incredible pace, the threat from cybercriminals is also growing rapidly. According to a report from Statista, there were over 750,000 unfilled cybersecurity jobs in 2023. In this article, we will discuss the correlation between cybersecurity and tech education. The Skills...

Harnessing Cybersecurity: A Strategic Advantage for Personal Injury Law Firms
In the digital age, personal injury law firms face unique challenges and opportunities. The rise of technology has transformed how legal services are provided, making it vital for law firms to adapt and innovate. One area that offers both significant challenges and opportunities is cybersecurity. This article delves into how personal injury law firms can...

Becoming a Cybersecurity Expert: Navigating Online Courses and Educational Resources
In the rapidly evolving landscape of cyberspace, where digital threats lurk around every corner, the importance of cybersecurity has never been more pronounced. With cyber-attacks becoming increasingly sophisticated, the demand for skilled cybersecurity professionals is on the rise. As individuals seek to fortify their defenses and embark on a journey into the realm of cybersecurity,...

Managing Cybersecurity Risks for IoT-Connected Devices
While technology has proven to make our lives much easier with daily tasks, there are some concerns and risks you need to keep in mind as you bring in more devices to your home, utilize high-tech vehicles for your business, and pursue upgraded personal vehicles. Below are some of the most common risks that you...
The Role of Payment Facilitators in Enhancing Cybersecurity for Online Transactions
Online transactions have become a cornerstone of our daily activities in the fast-paced digital world. However, with this convenience comes the increased risk of cyber threats. As more consumers and businesses engage in digital commerce, the importance of cybersecurity in online transactions has escalated significantly. This is where Payment Facilitators (PayFacs) play a crucial role....
5 Plugins That Prevent Malicious Login Attempts
Every website owner faces risks from brute-force hacking attempts and other security issues. This is especially true for open-source platforms such as WordPress. Although the open-source nature of WordPress makes life easier for developers and users, it also makes WordPress-based websites prone to security risks. That’s why professional WordPress development services providers emphasize addressing security issues to...
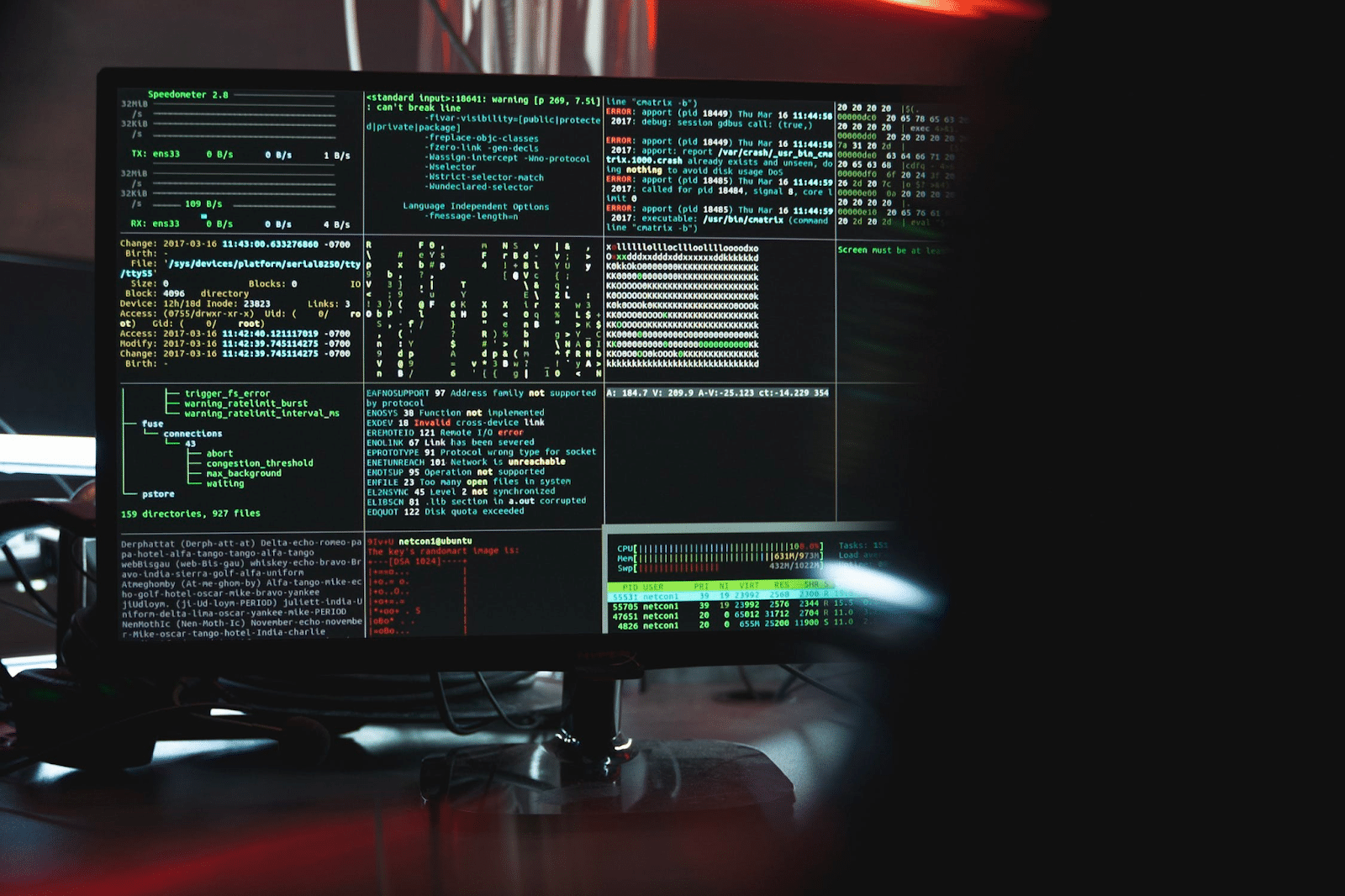
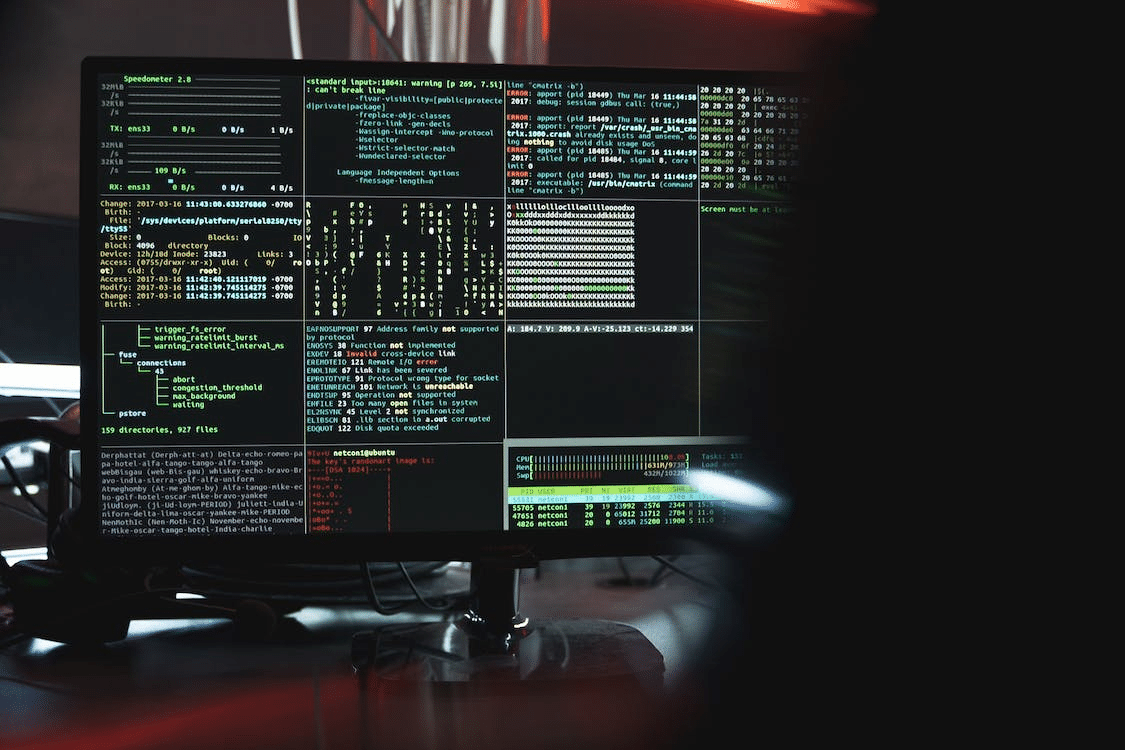
Top Cybersecurity Threats and Trends In 2024
As we move into the ever-evolving landscape of 2024, the digital realm remains a battleground for cyber threats that are constantly evolving in complexity and sophistication. Organizations and individuals must stay ahead of the curve to protect themselves from emerging dangers. In this blog post, with Vitaliy Klymenko, Editor-in-Chief in Slotamia and cybersecurity specialist, we...