Tagging Ethernet Frames for VLAN Identification
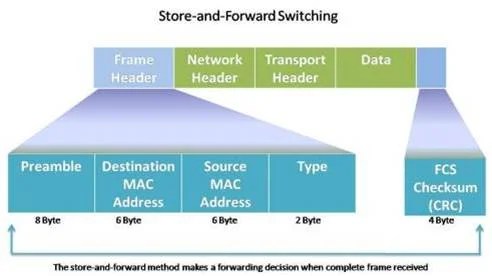
The Layer 2 devices use Ethernet frame header information to send packets without having routing tables. Usually, the Ethernet frame header does not contain any information about the virtual local area network (VLAN), so when Ethernet frames arrive in a trunk, The virtual local area network (VLAN) information should be added to the frame.
This method is called tagging. The standard for VLAN tagging is IEEE 802.1Q. The 802.1Q header includes a 32-bit tag inserted inside the original Ethernet frame header, specifying the VLAN to which the frame belongs.
When the switch receives an Ethernet frame on a port in access mode and is assigned a VLAN, the switch inserts a virtual local area network (VLAN) tag into the received frame header, calculates the FCS again, and sends out the tagged frame to the trunk port. The figure below illustrates the different fields of the VLAN tag:
- The Type—Type field is a 16-bit field called the tag protocol ID (TPID) value. The value for Ethernet is hexadecimal 0x8100.
- User priority– It has a 3-bit value that supports service implementation.
- Canonical Format Identifier (CFI)– This is a 1-bit identifier that enables Token Ring frames to be carried across Ethernet links.
- VLAN ID (VID)– A 12-bit VLAN identification number supports up to 4096 VLAN IDs.
Native VLANs and 802.1Q Tagging

Tagged Frames on the Native virtual local area network (VLAN)
Some devices that support trunking insert a VLAN tag into native VLAN traffic. If a port configured on 802.1Q trunk receives a tagged frame with VID and the same as the native VLAN, it drops the frame.
So, when configuring a switch port on a Cisco switch, configure devices to send untagged frames on the native VLAN. Other vendor devices, routers, non-Cisco switches, and servers support tagged frames on the native VLANs.
Untagged Frames on the Native VLAN
When a trunk port receives untagged frames, it forwards them to the native VLAN. If no devices are associated with the native VLAN and no other trunk ports are present, the switch drops the frame. When configuring an 802.1Q trunk port, the native VLAN ID is assigned as a default Port VLAN ID.
All untagged traffic coming in and out of the 802.1Q port is forwarded based on the PVID. For example, if VLAN 10 is native, every untagged data is sent to VLAN 10 with a PVID of 10. If the native has not been configured, the PVID value for the native VLAN is 1 because the default native VLAN is 1.
Voice VLAN Tagging

A separate voice VLAN is required for voice-over IP support. The port connecting the Cisco IP phone can be configured to use two VLANs: voice and data traffic.
The link between the IP phone and the switch works like the trunk to carry voice and data VLAN traffic. The Cisco IP Phone has a three-port 10/100 switch. These ports give dedicated connections to these devices:
- Port-1 – Connects the IP phone to the switch or other VoIP (Voice Over Internet Protocol) devices.
- Port-2 – This port is an internal 10/100 interface that carries the IP phone traffic.
- Port-3 – This access port connects to a PC or other device.
On the switch, the switch port is configured to send CDP (Cisco Discovery Protocol) packets and instruct an attached IP phone to send voice traffic to the switch in one of the following ways, depending on the type of traffic:
- In a voice VLAN tagging with a Layer 2 class of service priority value.
- In; an access VLAN tagging with a Layer 2 class of service priority value.
- In an access VLAN, untagged without a Layer 2 class of service priority value.
FAQs
Q1: What is VLAN tagging?
A1: VLAN tagging adds a VLAN tag to an Ethernet frame’s header to identify the VLAN to which the frame belongs. This helps in proper routing within VLAN-configured networks.
Q2: What standard is used for VLAN tagging?
A2: The standard used for VLAN tagging is IEEE 802.1Q. This standard defines the format and process for adding VLAN tags to Ethernet frames.
Q3: What are the components of an 802.1Q VLAN tag?
A3: An 802.1Q VLAN tag includes the following components:
- Type (TPID): A 16-bit field indicating the tag protocol ID.
- User Priority: A 3-bit field for service implementation.
- Canonical Format Identifier (CFI): A 1-bit identifier for Token Ring frames.
- VLAN ID (VID): A 12-bit field supporting up to 4096 VLAN IDs.
Q4: What is a native VLAN?
A4: A native VLAN is the default VLAN assigned to a trunk port. Untagged frames received on a trunk port are forwarded to the native VLAN.
Q5: How are tagged and untagged frames handled on a native VLAN?
A5: Tagged frames on a native VLAN are dropped if their VLAN ID matches the native VLAN. Untagged frames are forwarded to the native VLAN. If no devices are associated with the native VLAN, the frames are dropped.
Q6: What is the purpose of a voice VLAN?
A6: A voice VLAN separates voice traffic from data traffic, ensuring better quality of service for VoIP (Voice over IP) communications. Ports connecting to IP phones can be configured to use separate VLANs for voice and data.
Q7: How does VLAN tagging benefit network management?
A7: VLAN tagging simplifies network management by allowing administrators to segment networks logically, improving security, reducing broadcast domains, and enhancing traffic management.