Separation of the large broadcast domain into smaller ones improves network performance. By design, routers block broadcast traffic. But routers usually have a limited number of LAN interfaces. A router’s main role is to move data between different networks. Virtual Local Area Networks (VLANs) enhance network performance by segmenting large broadcast domains into smaller, manageable ones.
Routers block broadcast traffic, making VLANs essential on Layer 2 switches for end-device connectivity. Key configuration commands include <vlan 10>, <interface vlan 10>, and <ip address 192.168.10.1 255.255.255.0> Aligning with CCNA practical skills. VLANs adhere to the IEEE 802.1Q standard for tagging and interoperability. They enhance network performance, scalability, and security by separating large broadcast domains.
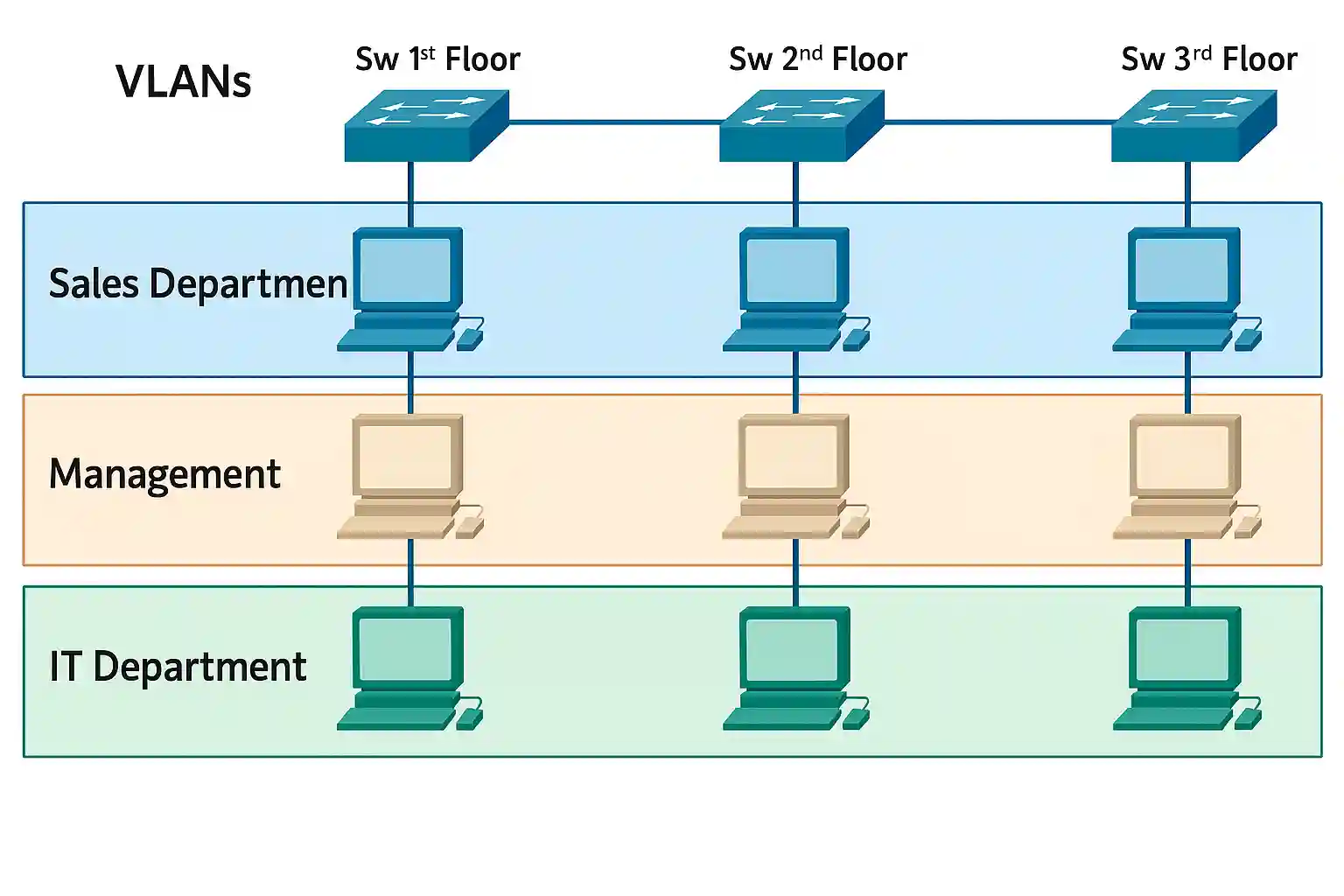
If a device in one VLAN sends broadcast data, all devices in that VLAN receive the data, but devices in other VLANs do not. Devices inside a VLAN act like they are in their independent network; however, they share a common infrastructure with other VLANs. Any switch port can belong to any VLAN, and unicast, broadcast, and multicast packets are forwarded and flooded only to the end station within the VLAN.
VLAN Trunking Protocol (VTP)
VTP manages VLAN configurations across switches. Modes include server (vtp mode server), client, and transparent, configurable with Cisco IOS commands.
For example, configure a switch as a VTP server with <vtp mode server> and set a domain name with <vtp domain MYDOMAIN> to propagate VLANs across the network.
What are VLANs?
Virtual Local Area Network also provides segmentation within a switched network. It is a technique that groups devices within a VLAN. Each VLAN operates as a separate logical network, requiring a router or routing-capable device to forward data to stations outside the VLAN.
Every Virtual Local Area Network is working as a separate logical network, and data destined for stations not in the VLAN must be forwarded through a router or device that supports routing.
Virtual Local Area Networks also make possible the implementation of access and security policies to particular groupings of users. For instance, each switch port is typically assigned to a single VLAN, though trunk ports can carry multiple VLANs using 802.1Q tagging.
Benefits of VLANs
VLANs make it simple to plan a network to maintain the goals of an organization. The most important benefits of Virtual Local Area Networks are as follows:
Security
Security is a primary benefit of VLANs, enabling isolation of sensitive data (e.g., management, sales, IT) using Access Control Lists (ACLs), such as access-list 10 permit 192.168.10.0 0.0.0.255. This can be implemented using Access Control Lists (ACLs), and VLANs also support Quality of Service (QoS) for VoIP prioritization.
Cost
Virtual LANs reduce the cost of the network because segmenting a network into smaller VLANs is cheaper than creating a routed network with routers.
Better Network Performance
Dividing flat Layer 2 networks into multiple broadcast domains reduces unnecessary traffic, integrating with Quality of Service (QoS) for VoIP. They integrate with Spanning Tree Protocol (STP) to prevent network loops, configurable with spanning-tree vlan 10 root primary.
Shrink Broadcast Domains
Dividing a large network into smaller VLANs reduces devices in the broadcast domain. As shown in the figure above, a total of nine hosts work in this network, but only three hosts are in the broadcast domains.
Improved IT staff efficiency
VLANs make network management very easy for IT staff because users with related network requirements share the same VLAN.
Simpler Project and Application Management
VLANs combine users and network devices to support both business and geographic requirements.
Simplified Administration for the Network Manager
VLAN simplifies network management. Grouping of users into virtual networks makes it easy to set up and control network policies at a group level.
Easy Troubleshooting
Network troubleshooting can be simpler and faster because different user groups are segmented and isolated from one another. If the network administrator knows that complaints are only coming from a different subset of users, the network administrator will be able to quickly narrow down where to look to find the issue.
| VLAN Type | Purpose |
|---|---|
| Default | Initial configuration |
| Data | User traffic |
| Native | Trunk compatibility |
| Management | Remote administration |
| Voice | VoIP support |
| Private | Enhanced security |
Types of VLANs
There are different types of Virtual Local Area Networks used in networking. The VLAN is defined by classes of traffic, and some others are defined by the specific function that they serve. Each switch has a default VLAN.
Default VLAN
VLAN-1 is the default VLAN on Cisco switches. After the first boot-up process, the switch loads the default configuration, and all switch ports become a part of the default VLAN (VLAN-1). The switch port that is part of the default VLAN works in the same broadcast domain. You can see that all ports are assigned to VLAN 1 by default. There is no difference between the features and functions of VLAN1 and other VLAN, excluding that it cannot be renamed or deleted. By default, all Layer 2 control traffic is associated with VLAN 1.

Data VLAN
A data VLAN is also called a user VLAN. It is used to separate the network into different groups of users or devices. Data VLAN is used to send user-generated traffic. It is also a separate voice and management traffic from data traffic.
Native VLAN
A native VLAN is assigned to an 802.1Q trunk port that was created for backward compatibility with old devices that don’t support VLANs, just like a hub. Frames belonging to the native VLAN are not tagged when sent out on the trunk links, so older devices can simply understand these frames.
Management VLAN
The separate VLAN for management, like monitoring, system logging, SNMP, and other sensitive management jobs, is best practice in networking. It also ensures that bandwidth for management will be available even when user traffic is high. VLAN 1 is also the management VLAN by default. Moreover, to create the management VLAN, the switch virtual interface of that VLAN is assigned an IP address and subnet mask, which management can remotely access via HTTP, Telnet, SSH, or SNMP. Due to VLAN 1’s default role, it’s best to assign a dedicated VLAN (e.g., VLAN 99) for management to enhance security, configured with interface vlan 99 and ip address 192.168.99.1 255.255.255.0.
Voice VLANs
If an organization uses voice over IP (VoIP), a separate VLAN is needed. This will save bandwidth for other applications and ensure VoIP quality. VoIP traffic requires assured bandwidth, priority, and less than 150ms delay, necessitating a dedicated VLAN design.
Private VLANs (PVLANs)
PVLANs enhance security with isolated and community types. Configure with <vlan 100 private-vlan isolated> to restrict communication.
Conclusion
The article is now more polished, with consistent formatting, reduced redundancy, and enhanced technical detail for CCNA/CCNP students. Remaining tasks include verifying all command examples with current Cisco IOS versions (e.g., 15.0 or later) and ensuring the attached image (show vlan brief output) is properly integrated with a caption. Let me know if you’d like further refinements or additional content!
FAQs
-
VLANs segment a network into smaller broadcast domains, improving performance and security by isolating traffic. They allow devices to be grouped logically regardless of physical location, enhancing management efficiency for network admins.