There are three main types of NAT translation: static NAT, dynamic NAT, and port address translation (PAT). This guide is tailored for CCNA (200-301) and CCNP (ENCOR & ENARSI) students, with full Cisco IOS configurations, packet walk-throughs, verification commands, and troubleshooting tips.
Static NAT
Static NAT translation is also known as one-to-one NAT. Static NAT translation maps network traffic from a static external IP address to a static internal IP address or an internal whole network. It translates real addresses to mapped addresses.
In other words, static NAT uses a one-to-one mapping of local and global addresses. The mapping includes destination IP address translation and source IP address translation in different directions.
Static NAT allows connections to be established and starts a conversation from either side of the network, but translation is limited to one-to-one or between blocks of addresses of the same size. In static NAT, for each private address, a public address must be reserved. No address pools are necessary for static NAT.
A static NAT translation is mostly used in enterprise networks to enable external network or Internet connectivity to computers, servers, or networking devices within a private local area network having an unregistered private IP address. It creates a one-to-one relationship between the public and private IP addresses.
So, the private IP address can be mapped to only one public IP address at a time. The end-user, on the other hand, has a transparent view of the remote device/network and accesses it using the mapped public IP address. It also ensures network security and privacy by hiding the details of internal network usage, architecture, and patterns from external or public users.
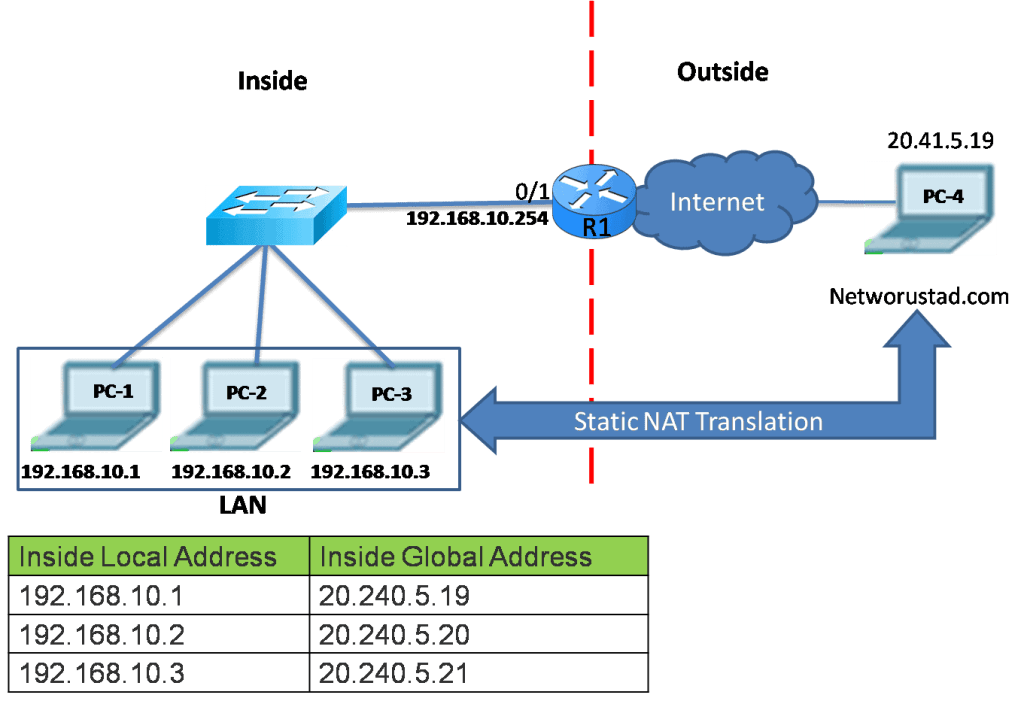
R1 is configured with static NAT for the inside local addresses of PC1, PC2, and PC3. When PC1, PC2, and PC3 send data to the Internet, their inside local addresses are translated to the configured inside global addresses. To outside networks, these devices have public IPv4 addresses.
Static NAT is also useful for devices that require authorized access while offsite but not by the general public on the Internet. For example, a network administrator from PC4 can SSH to devices in LAN inside global address 20.240.5.19. R1 translates this inside global address to the inside local address and connects the administrator to any device on the LAN.
The static NAT requires enough public IPv4 addresses to accommodate the total number of users. The static NAT translation table is also illustrated in the image below.
Dynamic NAT
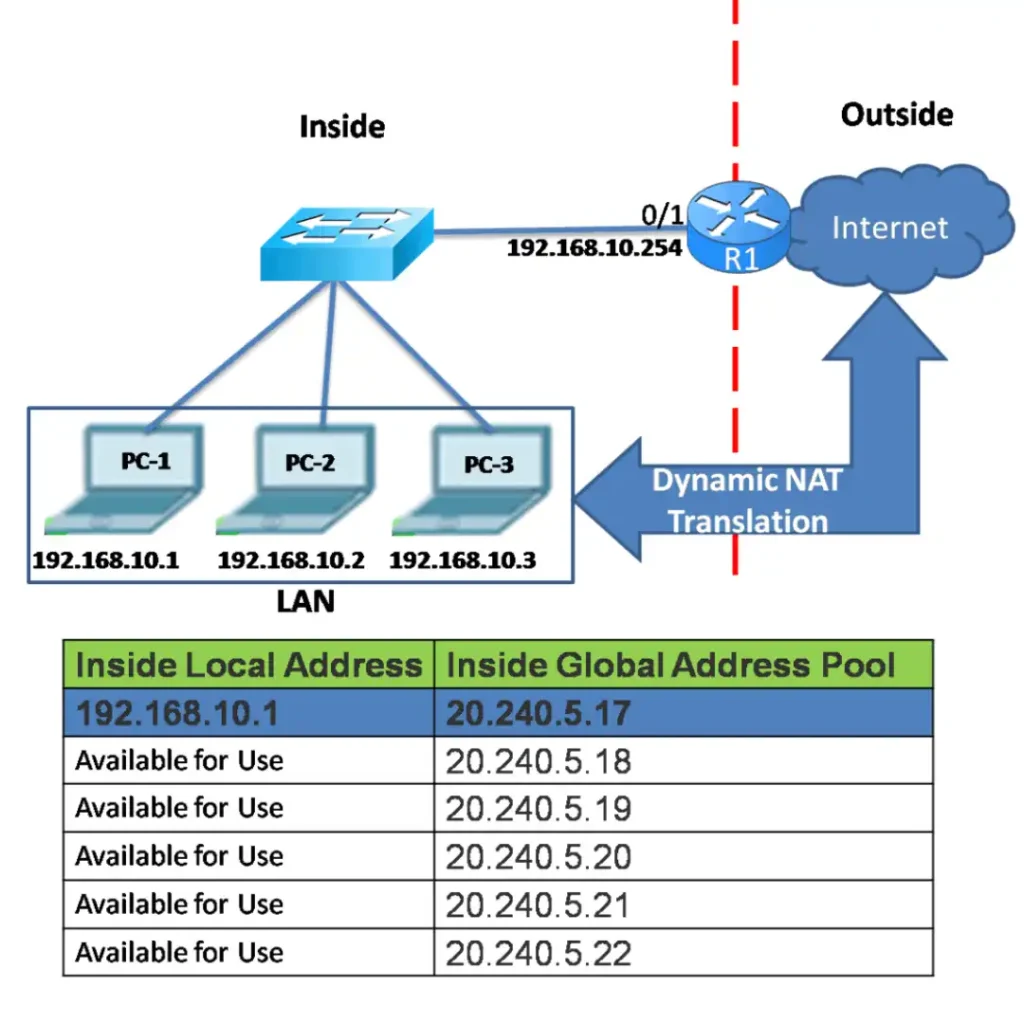
In the dynamic NAT, multiple private IP addresses are mapped to a pool of public IP addresses. Dynamic NAT is working on the principle of first come, first served.
We use dynamic NAT when we know the number of fixed users who want to access the Internet at a given point of time. When an inside user requests access to an outside network, dynamic NAT assigns an available public IPv4 address from the pool of addresses.
When an inside user sends traffic through the NAT router, it examines the source IP address and compares it to the internal local address pool. If it finds a match, then it determines which inside global address pool it should use for the translation.
The figure below illustrates the dynamic NAT. PC1 has accessed the Internet using the first available address in the dynamic NAT pool. The other addresses of the pool are still available for further use. Similarly to static NAT, dynamic NAT also requires enough public IPv4 addresses to assure the total number of simultaneous user sessions.
Port Address Translation (PAT)
Port Address Translation (PAT) is an extension of Network Address Translation (NAT) also known as the NAT overload. NAT permits multiple devices on a LAN to be mapped to a single public IPv4 address to conserve IP addresses.
In Port Address Translation (PAT), all devices that go through the address NAT router have the same global IP address assigned to them, including the source TCP or UDP port numbers to differentiate the different connections. If two devices have the same port number, the NAT router changes one of them to ensure uniqueness.
With Port Address Translation (PAT), when a device initiates a TCP/IP session, it generates a TCP or UDP source port value to individually recognize the session. When the NAT router receives a packet from the client, it uses its source port number to individually identify the specific NAT translation.
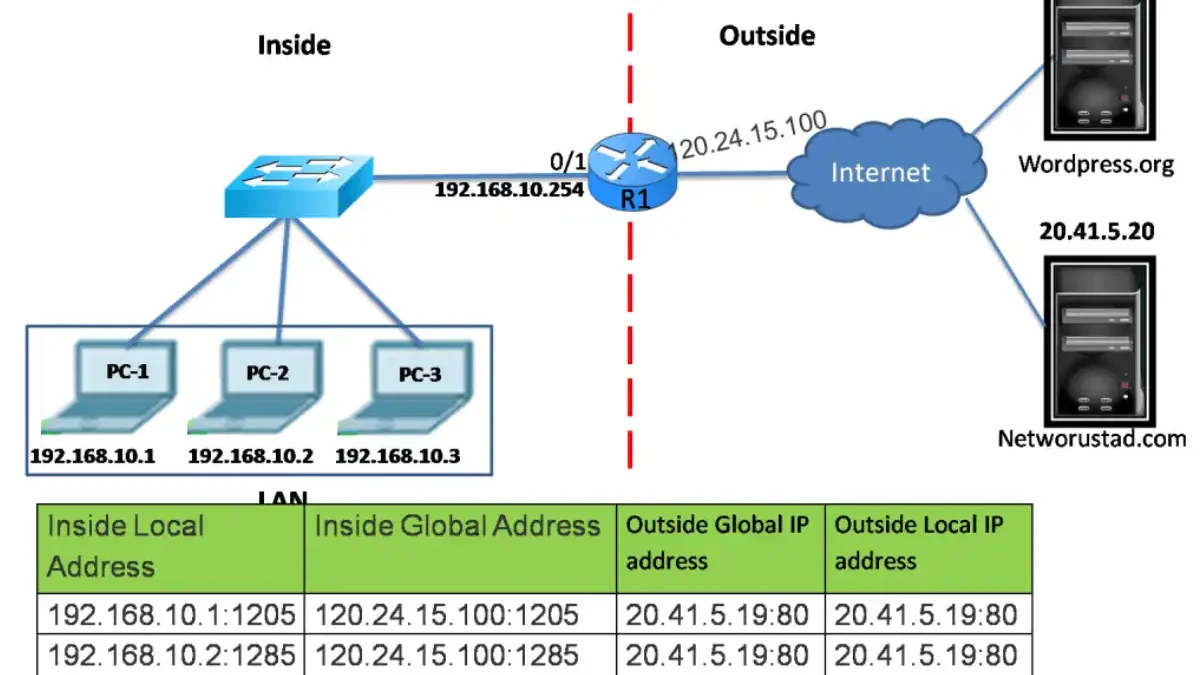
Port Address Translation ensures the use of a different TCP port number for each session with a server on the Internet. When a reply comes back from the server, the source port number becomes the destination port number, which determines the device forwards to the packets. The PAT process also ensures the incoming packets were requested; this adds security to the session. Now examine the figure below.
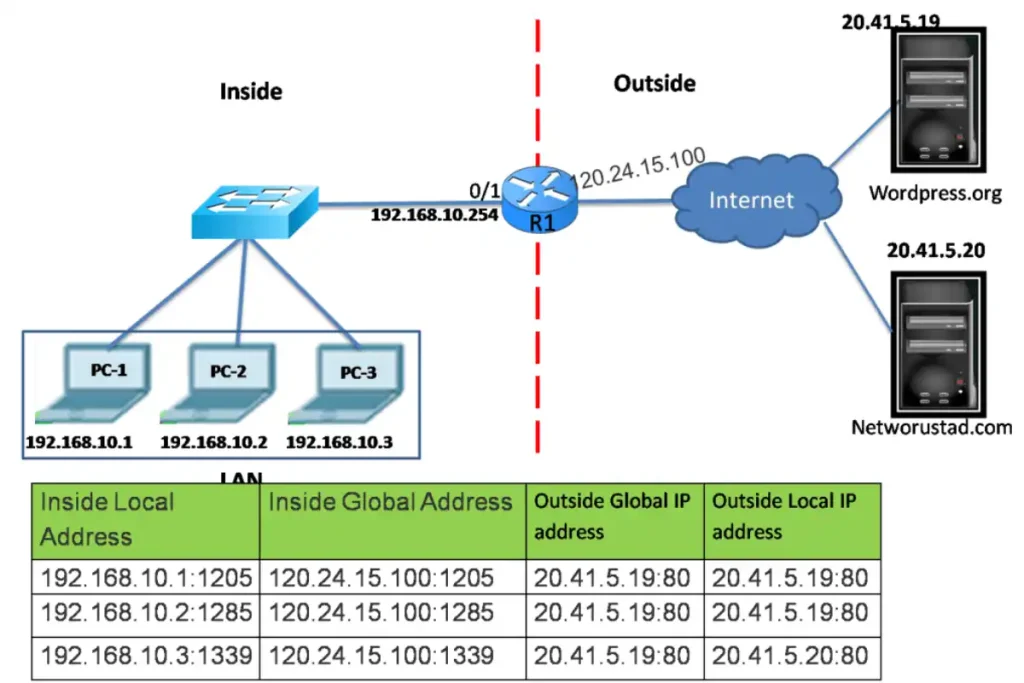
When R1 processes any packet, it uses a port number to individually identify the source of the packet. The source address is the inside local address, including the TCP/IP-assigned port number added by the NAT overloading.
The destination address is the outside local address, including the service port number added by the NAT-configured router. Port 80 is the HTTP port. R1 translates the inside local address to an inside global address, including the port number. The destination address is not changed.
In the example, the client port numbers are 1205, 1285, and 1339. The NAT-enabled router did not change the port numbers. There are chances that these port numbers may have already been used for other active sessions. (PAT Configuration)
PAT Port Allocation Groups
| Group | Port Range | Use Case |
|---|---|---|
| 0 | 0–511 | Well-known (avoided) |
| 1 | 512–1,023 | Registered ports |
| 2 | 1,024–65,535 | Dynamic/Ephemeral |
PAT preserves the original port if available. If conflict: Assigns next available port starting from Group 2 → Group 1 → next IP
NAT Order of Operation (CCNA Exam Essential)
| Direction | Order |
|---|---|
| Inside → Outside | 1. Routing → 2. NAT (Inside-to-Outside) |
| Outside → Inside | 1. NAT (Outside-to-Inside) → 2. Routing |
Key Exam Point: Static NAT is checked before dynamic/PAT.
Common Issues
| Symptom | Cause | Fix |
|---|---|---|
| No translation | ACL denies traffic | Verify access-list |
| 1:1 mapping only | Missing overload | Add overload keyword |
| No Internet | Wrong inside/outside | Swap interfaces |
| Port conflict | Too many sessions | Use larger pool |
FAQs – What are the types of NAT translation
What is the main difference between static NAT and dynamic NAT?
Static NAT creates permanent 1:1 mapping, requiring one public IP per private host; dynamic NAT assigns public IPs temporarily from a pool on a first-come, first-served basis, reusing addresses after sessions end.
How does PAT conserve public IPv4 addresses compared to static/dynamic NAT?
PAT maps thousands of private IPs to a single public IP by adding unique TCP/UDP source ports; static needs one public IP per host, and dynamic needs a pool equal to max simultaneous users.
What is the NAT order of operation when traffic flows from inside to outside?
Cisco checks the routing table first, then applies inside-to-outside NAT (static before dynamic/PAT). Outside-to-inside reverses: NAT first, then routing.
Why might a device fail to translate with the “no Internet access” symptom?
Common causes: wrong inside/outside interface designation, ACL blocking traffic, missing “overload” keyword in PAT, or exhausted dynamic pool. Swap interfaces or add overload to fix.
How does the router handle port conflicts in PAT?
PAT preserves the original port if available; if conflicted, it assigns the next free port starting from the dynamic range (1024–65535), then registered (512–1023), and finally another IP if a pool exists.