A passive interface is used in all routing protocols, where we can stop sending updates from a specific interface. The behavior varies from one protocol to another. In EIGRP, using the passive-interface, we stop sending outgoing hello packets; therefore, the router cannot form any neighbor adjacencies via the passive interface. This behavior stops both outgoing and incoming routing updates.
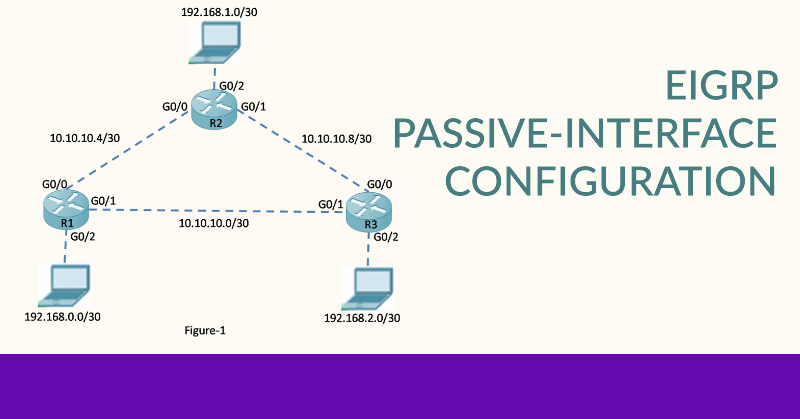
The passive-interface command can be used to stop the neighbor adjacencies. The command can be used in router configuration mode. We enable a passive interface to suppress unnecessary update traffic, for example, when an interface is a LAN interface with no other routers connected. It also increases security controls, such as stopping an unknown scoundrel routing device from receiving EIGRP updates. Figure 1 illustrates the R1, R2, and R3 where neighbor routers are not attached with interfaces GigabitEthernet 0/2 interfaces of R1, GigabitEthernet 0/2 interfaces of R2, and GigabitEthernet 0/2 interfaces of R3. The command syntax is the following:
Router(config-router)# passive-interface <interface-type interface-number>

Passive Interface
The passive-interface command prevents the exchange of routes on these interfaces, but EIGRP still includes these interfaces and their addresses in routing updates. The passive interface configuration for the above topology is as follows:
| Router R1 R1(config)#router eigrp 1 R1(config-router)# passive-interface gigabitEthernet 0/2 Router R2 R2(config)#router eigrp 1 R2(config-router)# passive-interface gigabitEthernet 0/2 Router R3 R3(config)#router eigrp 1 R3(config-router)# passive-interface gigabitEthernet 0/2 |
Using the passive-interface default command, we can configure all interfaces as passive. To disable an interface as passive, we can use the no passive-interface interface-type interface-number command in router configuration mode.
The passive-interface increases security by preventing the hello packet from An example of using the passive-interface to increase security controls is
When a network connects to a third-party organization over which the network administrator has no control, such as an ISP network, the local network must advertise the interface link through the local network. This security risk occurs if the ISP sends or receives a routing update to the local network devices. Anyone can compromise the local network through an ISP. So, in this case, we can set the interface connected to the ISP as a passive interface.
Verifying the Passive Interface
We can verify the interface on a router configured as passive using the “show ip protocols” command in privileged EXEC mode. Figure 2 illustrates the output of this command on router R1. Notice that a GigabitEthernet 0/2 interface of R1 is a passive interface, but the routing update still includes the address for this interface, 192.168.0.0.
FAQs: EIGRP Passive-Interface
1. What is EIGRP?
EIGRP (Enhanced Interior Gateway Routing Protocol) is an advanced distance-vector routing protocol used in computer networks to automate routing decisions and configuration.
2. What is a passive-interface in EIGRP?
A passive interface in EIGRP prevents sending EIGRP hello packets on a particular interface. This effectively stops EIGRP from forming neighbor relationships on that interface.
3. Why would I use a passive-interface in EIGRP?
Using a passive-interface can improve network security and efficiency by preventing unwanted EIGRP traffic and avoiding unnecessary formation of EIGRP neighbor relationships on certain interfaces.
4. How do I configure a passive-interface in EIGRP?
To configure a passive-interface in EIGRP, you use the command “passive-interface <interface>” in the EIGRP configuration mode. This disables the sending of EIGRP hello packets on the specified interface.
5. Can I use the passive-interface command on multiple interfaces?
Yes, you can configure multiple interfaces as passive by specifying each interface in the EIGRP configuration mode.
6. What happens to existing EIGRP neighbors when I configure an interface as passive?
Existing EIGRP neighbors on an interface that is newly configured as passive will be dropped, as the interface will no longer send EIGRP hello packets to maintain the neighbor relationship.
7. Is there a way to make all interfaces passive by default in EIGRP?
Yes, you can use the “passive-interface default” command in EIGRP configuration mode to make all interfaces passive by default. You can then use the “no passive-interface <interface>” command to selectively enable EIGRP on specific interfaces.
8. What are the benefits of using a passive-interface in EIGRP?
The main benefits include enhanced security by restricting EIGRP traffic and more efficient use of network resources by reducing unnecessary EIGRP communications.
9. Can the passive-interface command affect network performance?
Using passive-interface judiciously can improve network performance by limiting unnecessary EIGRP traffic. However, misconfiguring it might prevent essential EIGRP neighbor relationships, potentially causing network disruptions.
10. How can I verify the configuration of passive interfaces in EIGRP?
You can use the “show ip eigrp interfaces” command to verify which interfaces are configured as passive in EIGRP.