Wide-area networks (WANs) are used to connect different LANs together. They can bridge LANs within a city, country, or global region. For CCNA candidates, understanding WANs is crucial for the 200-301 exam’s Network Fundamentals domain (15-25% weightage). CCNP students dive deeper into scalable WAN designs via ENCOR (20-30% on WAN optimization). Here’s why WANs matter: They bridge geographic gaps, enabling secure data flow for hybrid workforces. WANs leverage distinct WAN technologies like MPLS, SD-WAN, and Ethernet WAN, contrasting LAN-focused Ethernet switching—key for CCNA’s Layer 2 vs. Layer 3 distinctions.
What is a WAN?
WANs operate beyond geographic scopes to interconnect enterprise LANs with remote sites. Owned by service providers, organizations pay service fees to rent connectivity. This enables data, voice, and video transportation across telephone networks, cable, or satellite links.
Regional or branch offices communicate with central sites, share data with partners, and support traveling employees accessing corporate resources. Home users send data over vast distances—e.g., banking via the internet—while students access global library indexes. Large corporations use WANs for internet access, inter-location connectivity, external services, and remote management.
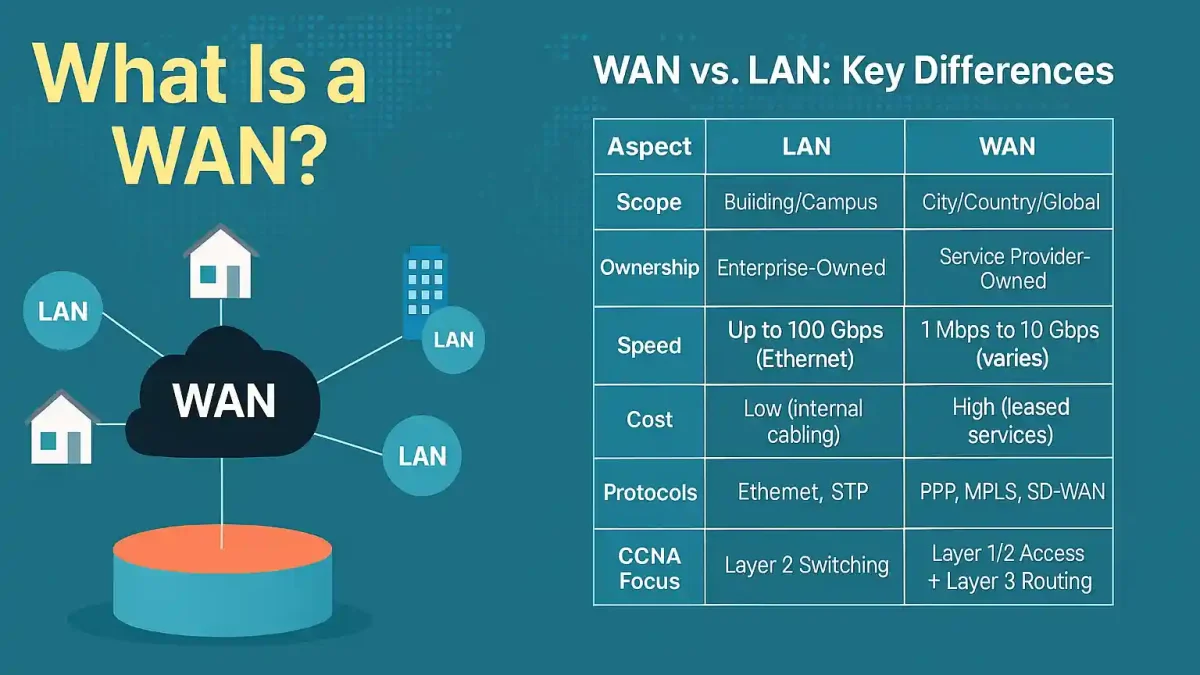
WAN vs. LAN: Key Differences
While LANs focus on local, high-speed Ethernet within buildings, WANs span cities or continents via leased lines.
| Aspect | LAN | WAN |
|---|---|---|
| Scope | Building/Campus | City/Country/Global |
| Ownership | Enterprise-owned | Service Provider-owned |
| Speed | Up to 100 Gbps (Ethernet) | 1 Mbps to 10 Gbps (varies) |
| Cost | Low (internal cabling) | High (leased services) |
| Protocols | Ethernet, STP | PPP, MPLS, SD-WAN |
| CCNA Focus | Layer 2 Switching | Layer 1/2 Access + Layer 3 Routing |
For CCNA, contrast LAN topologies (e.g., star) with WAN point-to-point links.
WAN Devices and WAN Technologies
WANs interconnect enterprise LANs to remote sites via carrier links. ISPs like AT&T or Verizon lease WAN edge devices, but enterprises increasingly deploy BYOD (Bring Your Own Device) models with SD-WAN for cost savings (up to 50%). Service providers deliver data, voice, and video over diverse infrastructures.
Edge Devices
- Routers: E.g., Cisco ISR series for CCNA labs—handle routing and encapsulation.
- Switches: For WAN handoff in Ethernet-based services.
Provider Equipment
- Core Routers: E.g., ASR 9000 series for MPLS backbones.
- Modems/Gateways: Convert signals for last-mile delivery.
Modern Additions
- SD-WAN Controllers: E.g., Cisco vManage for policy-based routing—essential for CCNP scalability.
| Device Type | Example | CCNA/CCNP Relevance |
|---|---|---|
| CPE Router | Cisco 2900 | Configures PPP/HDLC encapsulation |
| DCE Modem | Cable Modem | Handles clocking and signaling |
| SD-WAN Appliance | Viptela | Optimizes traffic over Internet/VPN |
WANs in the OSI Model
A WAN operates at both the physical layer and the data link layer of the OSI model. WAN access describes both physical layer delivery methods and data link layer requirements, including physical addressing, flow control, and encapsulation.
Physical layer protocols define electrical, mechanical, and operational aspects of connections. Data link layer protocols handle encapsulation and transmission mechanisms.
Visualize this: Layer 1 (Physical) manages cabling (e.g., T1/E1); Layer 2 (Data Link) encapsulates frames (e.g., via PPP). For CCNA, memorize: WANs skip Layers 3-7 at the edge, focusing on access.
CCNA Question Example: Which OSI layer defines WAN encapsulation? (Answer: Layer 2).
Different WAN technologies enable this: PPP, Frame Relay, HDLC, Ethernet WANs, MPLS, VSAT, and Broadband. Legacy links favor point-to-point (e.g., serial), but multipoint Ethernet WANs dominate in 2025 hybrid setups.
Essential WAN Terminology
The physical layer describes connections between the company and the service provider network. Common WAN terms include:
Customer Premises Equipment (CPE)
Devices on the enterprise edge connecting to carrier links, including wiring. Owned or leased from providers.
CCNA Tip: Configure on ISR routers with interface serial commands. Now often virtualized in NFV for cloud WANs.
Data Communications Equipment (DCE)
Devices that establish, maintain, and terminate sessions between WAN cloud and destinations (e.g., modems).
CCNP Insight: Handles DTR/DSR signaling in lab sims like Packet Tracer.
Data Terminal Equipment (DTE)
Source/destination for digital data (e.g., PCs, routers). Requires DCE to connect local loop to WAN; converts/reconverts signals.
CCNA Tip: Routers act as DTE in serial configs—set with clock rate on DCE side.
Demarcation Point
Border between customer and provider equipment; a junction box linking CPE to local loop.
Update for 2025: Virtualized in SASE architectures for simplified handoffs.
Local Loop
Copper or fiber cable connecting CPE to the provider’s Central Office (CO).
CCNA Tip: Common bottleneck—test with show interfaces for errors.
Central Office (CO)
Provider’s local office linking CPE to the broader network.
CCNP Insight: Houses DSLAMs for broadband; key in QoS designs.
Toll Network
All WAN-core equipment: fiber lines, switches, and routers.
Update for 2025: Increasingly software-defined with SDN overlays.
Local Exchange (LE): The CO’s switching fabric; contrasts with toll for intra-city vs. inter-city routing.
CCNA Tip: Understand LE for T1/E1 circuit mapping.
Common WAN Protocols
WAN protocols operate at Layer 2 for encapsulation and access. Key ones for CCNA/CCNP:
- PPP (Point-to-Point Protocol): Versatile for serial links; supports authentication (CHAP/PAP). Config:
encapsulation pppon interfaces. CCNA staple for dial-up/VPN basics. - HDLC (High-Level Data Link Control): Cisco default for serial; bit-oriented, error-free. Config:
encapsulation hdlc. Reliable but lacks authentication. - Frame Relay: Legacy packet-switched; uses DLCI for virtual circuits. CCNA-tested for migration: Map DLCIs with
frame-relay map. - MPLS (Multiprotocol Label Switching): Label-based forwarding for traffic engineering/QoS. CCNP focus:
mpls ipglobal config; enables VPNs.
Exam Tip: Compare: PPP > HDLC for security; MPLS over Frame Relay for scalability.
WAN Topologies and Design Best Practices
WAN topologies define connectivity patterns; choose based on redundancy, cost, and scale.
- Point-to-Point: Direct links (e.g., T1); simple for CCNA but costly.
- Hub-and-Spoke: Central hub routes to spokes; efficient for headquarters-branch.
- Full Mesh: All-to-all direct; high redundancy but expensive (n(n-1)/2 links).
- Partial Mesh: Balanced hybrid.
| Topology | Pros | Cons | CCNP Use Case |
|---|---|---|---|
| Hub-and-Spoke | Low cost, centralized mgmt | Single failure point | Branch offices |
| Full Mesh | High availability | Scalability issues | Critical financial nets |
| Partial Mesh | Balanced cost/redundancy | Complex config | Enterprise with partners |
Best Practices: For CCNP, design with BGP for dynamic peering; incorporate redundancy (e.g., dual MPLS + Internet).
Troubleshooting WAN Issues for CCNA/CCNP
Common WAN faults: Link down, encapsulation mismatch, clocking errors. Use layered approach.
- Layer 1: Verify cabling/DCE clock:
show controllers serial(check alarms). - Layer 2: PPP negotiation fails?
debug ppp negotiation; ensure matching encapsulation. - Scenario (CCNA): Serial interface up/up but no connectivity—fix with
clock rate 64000on DCE.
CCNP Advanced: MPLS label issues—show mpls forwarding; SD-WAN path selection via show sdwan omp routes.
Commands Table:
| Issue | Command | Output Check |
|---|---|---|
| Interface Status | show ip interface brief | Up/Up |
| Encapsulation Mismatch | show run interface | Matching PPP/HDLC |
| DLCI Mapping (Frame) | show frame-relay map | Active PVCs |
Future of WAN: SD-WAN and 5G
WANs evolve with cloud and mobility. SD-WAN overlays intelligent routing over Internet/MPLS, enabling zero-touch provisioning and app-aware policies. By 2026, 70% of enterprises will adopt SD-WAN. IDC predicts 60% will leverage it for AI-enabled automation by 2026.
5G WAN slicing offers low-latency private networks for IoT/edge. Ethernet WAN (MetroE) grows for 10G+ speeds.
2025 Trend: Gartner highlights an $8B opportunity in managed SD-WAN services.
CCNA/CCNP Exam Prep
Master WANs with these tips:
- Memorize: OSI Layers 1-2 for WAN; protocols like PPP vs. HDLC.
- Labs: Packet Tracer serial configs; GNS3 for MPLS.
- Practice Questions:
- What replaces Frame Relay? (A: MPLS/SD-WAN)
- DTE sets clock rate? (False—DCE does)
- MPLS benefit? (Traffic engineering)
- SD-WAN key feature? (App optimization)
- WAN topology for cost? (Hub-and-spoke)
Resources: Cisco Learning Network, Boson ExSim. Aim for 80% on WAN sims.
FAQs
What is a Wide Area Network (WAN) and how does it differ from a LAN?
WANs connect LANs across cities, countries, or globally using service provider infrastructure for data, voice, and video sharing. Unlike LANs, which are enterprise-owned for local buildings/campuses with high speeds (up to 100 Gbps) and low costs, WANs are leased, slower (1 Mbps-10 Gbps), and pricier, focusing on Layer 1/2 access and routing protocols like PPP/MPLS.
What are the main types of WAN technologies?
Key types include leased lines for dedicated point-to-point links, circuit switching for session-based connections via modems, packet switching (e.g., Frame Relay) for efficient shared data packets using virtual circuits, and cell relay variants. Modern additions like MPLS enable label-based VPNs, while SD-WAN overlays optimize apps over Internet/MPLS for scalability and cost savings up to 50%.
What are the advantages and disadvantages of WAN technologies?
Advantages: Bridge geographic gaps securely, support hybrid work with high availability in mesh topologies, and reduce costs via SD-WAN (70% adoption by 2026) with AI automation. Disadvantages: High leased service fees, variable speeds slower than LANs, single failure risks in hub-and-spoke setups, and migration needs from legacy Frame Relay to MPLS/SD-WAN for better scalability.
What protocols are commonly used in WAN technologies, and why?
PPP offers versatile serial encapsulation with authentication (CHAP/PAP) for secure links; HDLC is Cisco’s default for error-free bit-oriented transmission but lacks auth. MPLS provides QoS via labels for traffic engineering, while SD-WAN enables intelligent app-aware routing. These focus on OSI Layers 1-2 for physical delivery and data encapsulation in diverse infrastructures.