Transmission Control Protocol (TCP) accepts data, segments it into chunks with headers, and encapsulates these into IP datagrams for peer exchange. TCP Reliability and Flow Control ensure complete, ordered delivery on Windows or Linux, critical for 2025 networks as of July 2025.
TCP Reliability
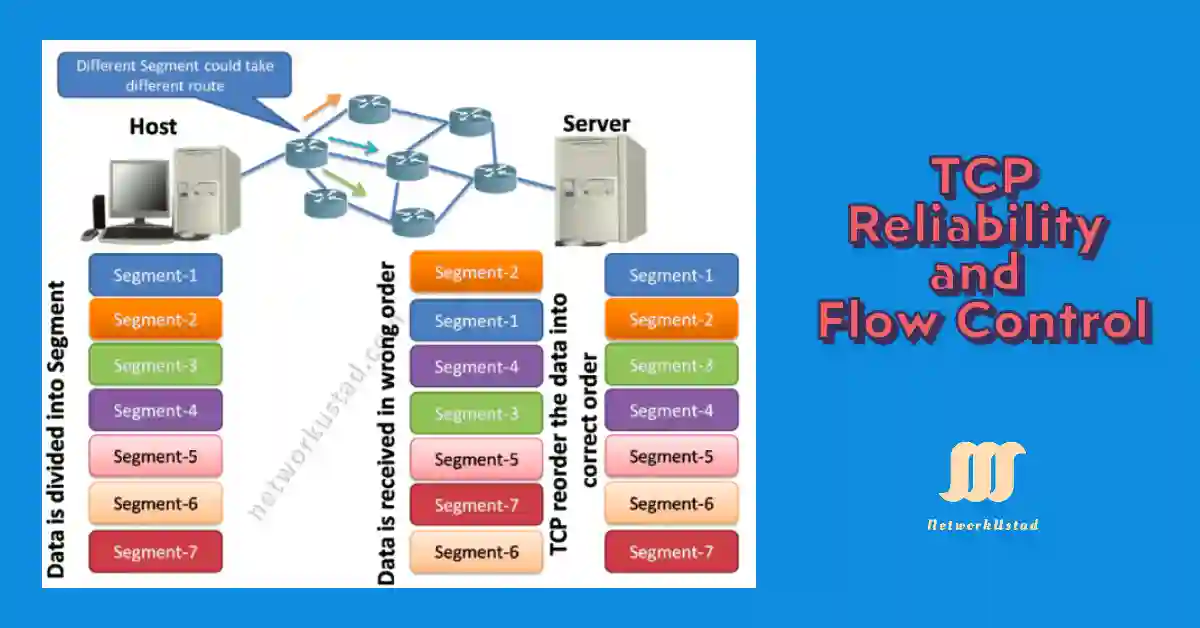
The TCP segments will possibly arrive at their destination out of order. For understanding, the original message to the receiver, the data in these out-of-order segments is reassembled in the correct order. Each segment’s header has been assigned a sequence number to achieve this goal. The sequence number represents the first data byte of the TCP segment.
During the established session, the first sequence number (ISN) is set. This ISN represents the opening value of the bytes for this session, which is transmitted to the receiving side application. When data is transmitted during the established session. The sequence number is increasing by the number of transmitted bytes. This data byte tracking enables every segment to individually find and acknowledge.
The missing segments can be identified and also reported. The ISN is effectively a random number. This is to avoid certain types of malicious attacks. For simplicity, we will use an ISN of 1 for the examples. Sequence numbers also show how to reassemble and reorder received segments, as shown in the figure.
The receiving TCP process places the data from a segment into a receiving buffer. Segments are in the proper sequence order and passed to the application layer when reassembled. The wrong order sequence number remains held for later processing. If, when the segments with the missing bytes reach the destination, these segments are processed in proper order.
TCP Flow Control
TCP also guarantees a reliable communication channel over an unreliable network. When someone sends data to another host, the host can receive the packets out of order; the host can lose the packets or the network can be congested, or the receiver node can be overloaded. When we are sending some application data, we usually don’t need to deal with this complexity; we just write data to a socket, and TCP flow control makes sure the packets are delivered correctly to the receiver node. The TCP flow control is a service of TCP.
Window Size and Acknowledgment
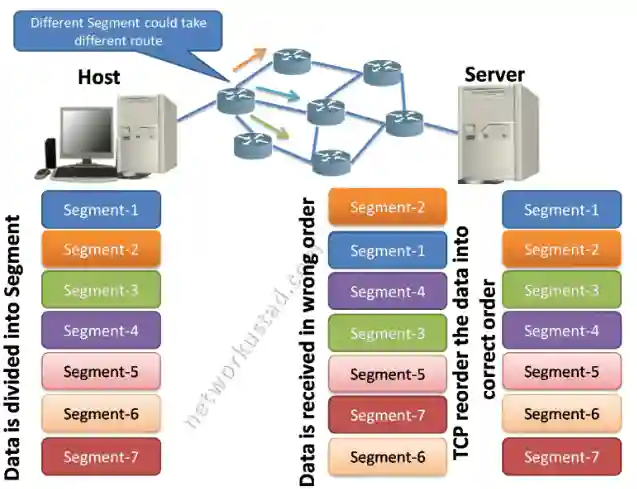
TCP flow control also checks the quantity of data that the destination host can receive and process reliably. It is the service that maintains the reliability of TCP transmission by adjusting the rate of data flow between the source host and destination host for an established session. To achieve this, the TCP header includes a 16-bit field called the window size.
The figure below illustrates an example of window size and its acknowledgements, which is the process of flow control. The window size is the number of bytes that the destination device of a TCP session can accept and process a single time. In this example, the host-B’s initial window size for the TCP session is 1,500 bytes.
Starting with the first byte, byte number 1, the final byte host-A can send without receiving acknowledgements is byte 1,500. This is host-A’s sending window. The window size is also included in every TCP segment, so the receiver can adjust the window size at any time depending on buffer availability.
The figure illustrates that the source is transmitting 1,500 bytes of data within each TCP segment. This is called MSS (Maximum Segment Size). The primary window size is settled upon when the TCP session is established, during the three-way handshake. The source host must bound the number of bytes sent to the destination host based on the destination’s window size.
Only after the source host receives an acknowledgement of receiving all the bytes at the destination host can it continue sending more data for the session. Usually, the destination host will not wait for all receiving bytes for its window size before replying with an acknowledgement. When the destination bytes are received and processed, the destination host will send acknowledgements to inform the source host that it can continue to send additional bytes.
Usually, the server will wait until it receives all 4,500 bytes before sending an acknowledgement. This means the host can correct its send window as it receives acknowledgements from the server. As shown in the figure, when host-A receives an acknowledgement with the acknowledgement number 3,001, it sends a window with an increment of another 4,500 bytes (the size of host-B’s current window size) to 7,500. host-A can now continue to send up to another 4,500 bytes to host B as long as it does not send past its new send window at 7,500.
The process of the destination host sending acknowledgements as it processes bytes received and continually adjusting the source’s send window is known as sliding windows. If the availability of the destination’s buffer space decreases, it may reduce its window size to inform the source to reduce the number of bytes it should send without receiving an acknowledgement. The window size determines the number of bytes that can be sent before expecting an acknowledgement. The next expected byte is a call for an acknowledgement number.
Congestion Avoidance
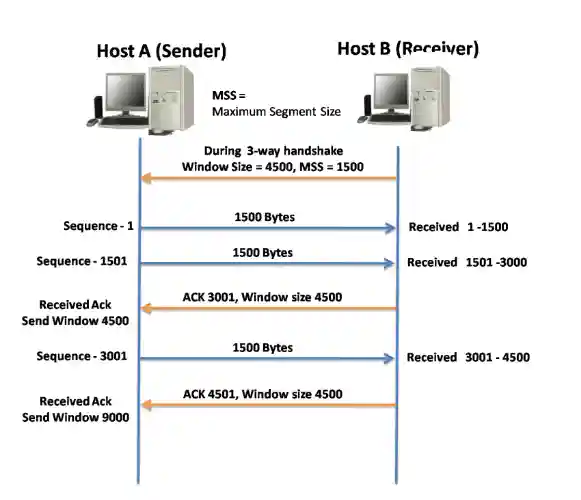
When congestion occurs on a network, it results in packets being discarded due to overload on the router. When packets containing TCP segments don’t reach their destination, they leave the packet without acknowledgement. By determining the rate at which TCP segments are sent but not acknowledged, the source host can estimate a certain level of network congestion.
One of the main principles of congestion control is avoidance. TCP tries to sense symbols of congestion earlier than it happen and to reduce or increase the load into the network accordingly. The option of waiting for congestion and then reacting is not as good because once a network saturates, it does so at an exponential growth rate and decreases the whole throughput enormously.
It takes a long time for the queues to consume, and then all senders host again and repeat this phase. By taking a practical congestion avoidance approach, the pipe is kept as full as possible without the threat of network saturation. The key is for the sender host to recognize the state of the network and client and to control the amount of traffic injected into the system.
Whenever there is congestion, retransmission of lost segments from the source will take place. If the retransmission is not controlled properly, the extra retransmission of the TCP segments can make the congestion even worse. Not only are new packets with TCP segments introduced into the network, but the feedback effect of the retransmitted TCP segments lost will also add to the congestion. To avoid and control congestion, TCP employs several congestion management mechanisms, timers, and algorithms.
If the source host did not receive an acknowledgement, or the acknowledgement was not received timely. Then it can reduce the number of bytes it sends before receiving an acknowledgement. Note that it is the source host that is decreasing the number of unacknowledged bytes it sends and not the window size determined by the destination. The figure above illustrates the TCP congestion control. The acknowledgement number is for the next expected byte, not for the segment.
Practical Example
Check sequence numbers on Windows with netstat -an or Linux with ss -i, e.g., a segment with sequence 1001-1500 arriving out of order can be reordered using buffer analysis.
Congestion Control Algorithms
TCP uses algorithms like Slow Start, Congestion Avoidance, Fast Retransmit, and Fast Recovery. On Linux, tune with sysctl -w net.ipv4.tcp_congestion_control=cubic (default in 2025).
Troubleshooting Tips
If segments are lost, use ping -t (Windows) or ping -f (Linux) to check network issues.
For buffer overflow, adjust window size with netsh int tcp set global autotuninglevel=restricted (Windows) or sysctl -w net.core.rmem_max=8388608 (Linux) as of 2025.
Conclusion
In summary, the Transmission Control Protocol (TCP) plays a pivotal role in ensuring reliable, ordered, and efficient data delivery across modern networks, a critical aspect for 2025’s growing IoT and enterprise environments. Through segmentation, sequence numbers, and the Initial Sequence Number (ISN), TCP reliability guarantees that out-of-order or lost segments are reassembled and retransmitted, verifiable on Windows with netstat -s or Linux with ss -i.
Flow control, facilitated by the sliding window mechanism and adjustable window sizes, prevents receiver overload, manageable via sysctl (Linux) or netsh (Windows) tuning. Congestion avoidance further optimizes performance by preemptively adjusting data rates, leveraging algorithms like Slow Start and Fast Retransmit, tunable with net.ipv4.tcp_congestion_control (Linux) or congestionprovider (Windows) as of 2025. By mastering these TCP features and applying OS-specific tools, network administrators can enhance server performance, troubleshoot effectively, and secure data transmission in today’s dynamic network landscapes.
FAQs
What is TCP reliability?
TCP reliability ensures data is delivered accurately by segmenting it into packets, detecting losses, and retransmitting if needed. It uses acknowledgments and sequence numbers to maintain order and integrity.
How does TCP handle out-of-order segments?
TCP receives segments that may arrive out of order due to different routes and reorders them correctly. It uses sequence numbers to reconstruct the original data sequence at the destination.
What is the role of flow control in TCP?
Flow control in TCP prevents the sender from overwhelming the receiver by regulating data transmission rate. It uses a sliding window mechanism to manage the amount of data sent.
Why is data segmentation important in TCP?
Data segmentation breaks large data into smaller segments for transmission, improving efficiency and reliability. It allows TCP to manage packet loss and reordering effectively across networks.
How does TCP ensure efficient data delivery?
TCP ensures efficiency by segmenting data, reordering out-of-sequence packets, and controlling flow. This process minimizes data loss and optimizes transmission between Host and Server.