Month: September 2019
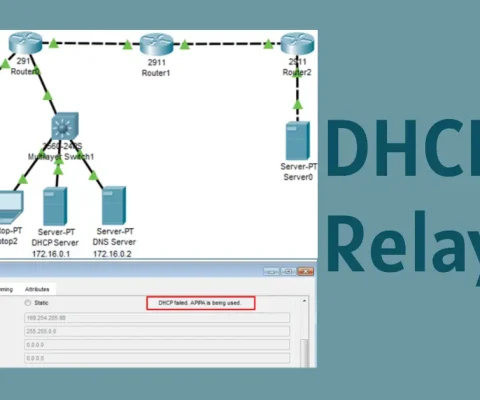
What is DHCPv4 Relay?
In enterprise networks, dedicated servers are usually used to provide DHCP, DNS, TFTP, and FTP services. The clients are not generally on the same subnet as those servers. The clients used to broadcast messages to locate the servers and get services. Now, look at the figure below. Laptop0 is attempting to acquire an IPv4 address...
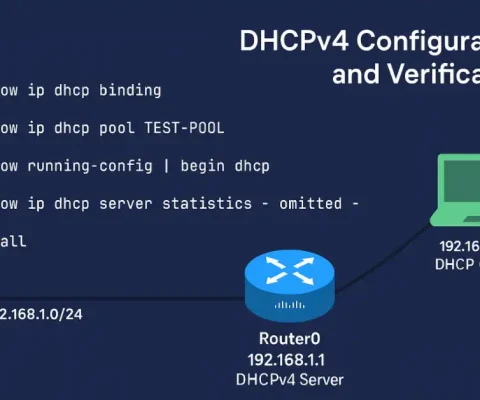
Master DHCPv4 Server Configuration (Updated 2025)
A Cisco router can be configured as a DHCPv4 server. The DHCPv4 server assigns and manages IPv4 addresses from specified address pools within the router to DHCPv4 clients. The steps for configuring the DHCPv4 server on Cisco routers are the following: Excluding IPv4 Addresses The router configured as the DHCPv4 server assigns all IPv4 addresses...
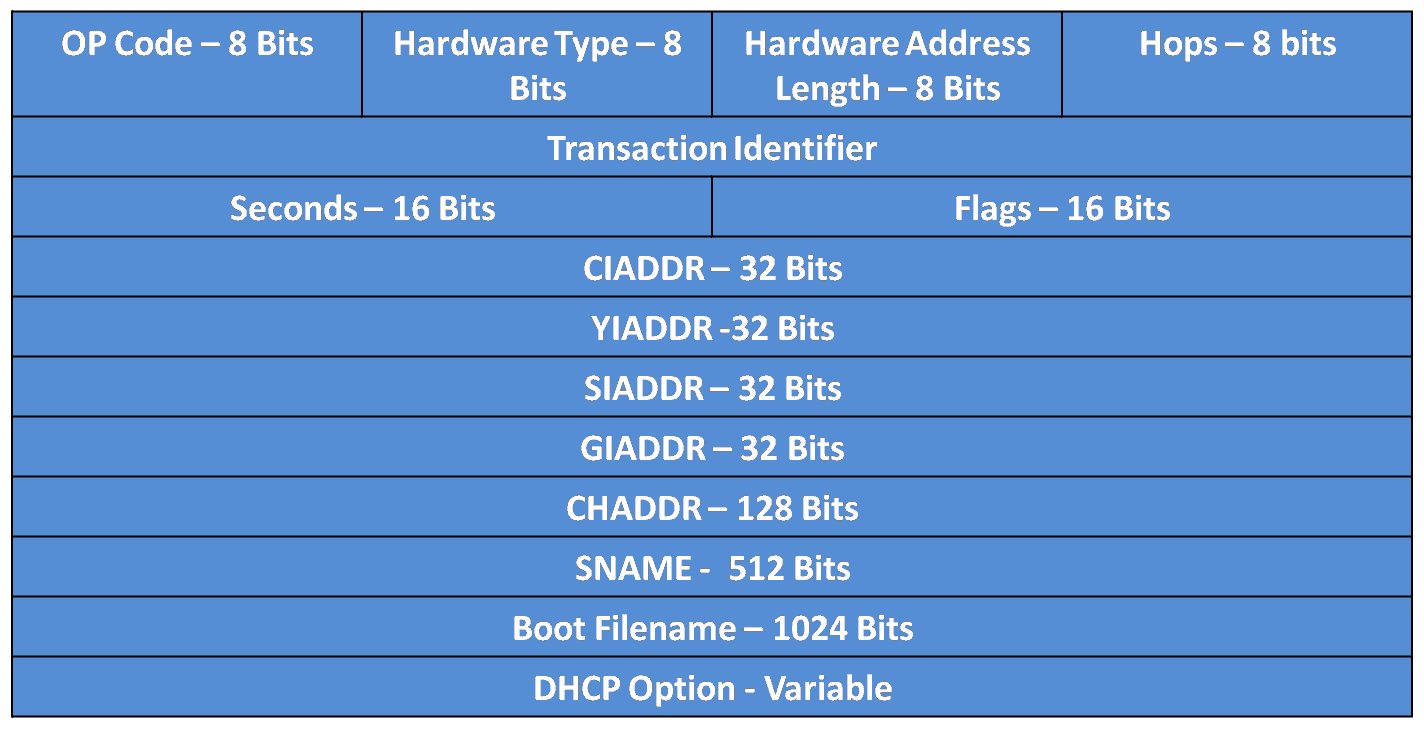
Understanding DHCPv4 Message Format
Dynamic Host Configuration Protocol version 4 (DHCPv4) is a cornerstone of IP address management in IPv4 networks, automating the assignment of IP addresses, subnet masks, default gateways, and other network parameters. Based on the Bootstrap Protocol (BOOTP), DHCPv4 uses UDP ports 67 (server) and 68 (client) to exchange messages between clients and servers. This article...
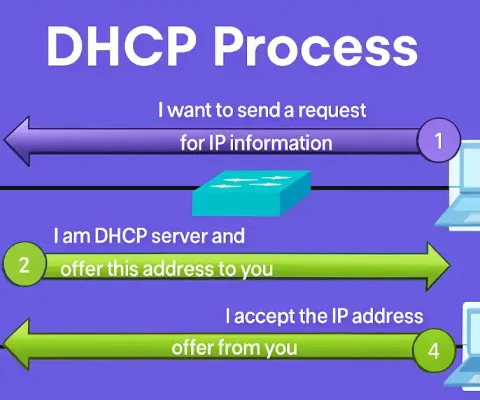
Understanding DHCPv4: A Comprehensive Guide
In modern networking, every device requires a unique IP address to communicate effectively. Understanding IP address management is crucial for network management. Static IP addresses are manually assigned to devices like routers, servers, and printers with fixed locations, enabling easy remote management. However, managing IP addresses for mobile or frequently changing devices is challenging, which...
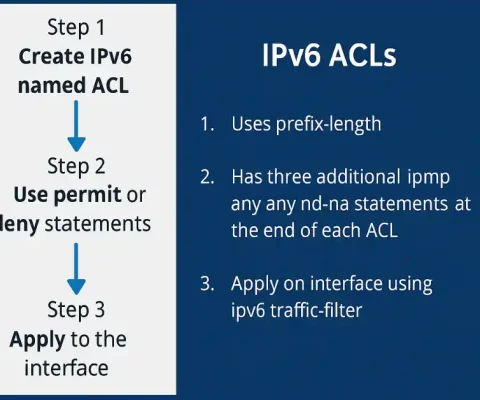
Understanding IPv6 ACLs Configuration: Step-by-Step Guide
Access Control Lists (ACLs) are a fundamental component of network security, and understanding IPv6 ACLs is essential for CCNA and CCNP certification candidates. As networks transition from IPv4 to IPv6 to accommodate the growing number of devices, mastering IPv6 ACL configuration is critical for securing modern networks. This comprehensive guide explains IPv6 ACLs, compares them...
How to Troubleshoot ACL Errors
Access Control Lists (ACLs) are fundamental to network security and traffic management in Cisco environments. However, misconfigurations can lead to ACL errors, blocking legitimate traffic or allowing unauthorized access. This article explores common ACL errors with examples, focusing on troubleshooting techniques using show commands. Understanding these errors is crucial for passing certification exams and excelling...
Inbound and Outbound ACL Logic
Access Control Lists (ACLs) are a fundamental component of Cisco networking, used to filter traffic based on predefined rules. For CCNA and CCNP students, mastering ACLs is critical for securing networks and passing certification exams. ACLs allow network engineers to permit or deny packets based on criteria like source and destination IP addresses, protocols, and...
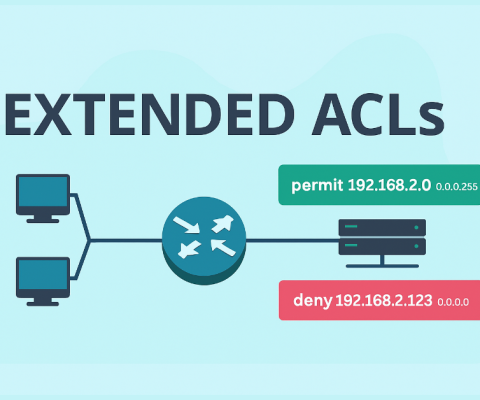
How to Configure Extended ACLs – Exclusive Explanation
The number of extended ACLs ranges from 100 to 199 and 2000 to 2699, providing 799 possible numbered ACLs. The 100-199 range was historically used, while 2000-2699 is recommended for modern networks due to greater flexibility and support for named ACLs. Choose based on your network’s complexity and Cisco IOS version. We can also create...

What Is Social Engineering in Cybersecurity? Types, Examples, and Prevention Strategies (2025 Guide)
Social engineering remains one of the most effective tactics in a cybercriminal’s arsenal, accounting for 36% of initial access vectors in incident response cases between May 2024 and May 2025. It’s a psychological manipulation technique where attackers exploit human behavior to gain unauthorized access to information, systems, or physical locations—without relying on code or exploits....

Browser Plugins and Poisoning: Risks, Exploits, and Defenses in Cybersecurity
Security backdoors and vulnerabilities can severely impact web browsers, leading to unwanted pop-up ads, collection of personal data, or installation of adware, viruses, or spyware. Cybercriminals often target a browser’s executable files, core components, and browser plugins to gain unauthorized access. Browser Plugins A browser plugin (now often called an extension or add-on in modern...