Imran Khan
Cybersecurity specialist and certified ethical hacker (CEH). Focuses on penetration testing methodologies and network vulnerability assessments. Contributed 280+ articles on intrusion detection systems and firewall configurations for NetworkUstad.

Malwarebytes Helps You Stay Secure Without Overthinking It
Malwarebytes offers straightforward digital security that runs in the background, eliminating the need to overthink every online action. Its clean interface provides clear visibility into threats and protection status. Users gain confidence without technical overwhelm.
Cyber-Smart Business: How Owners Can Stay Secure in a Digital World
Digital growth exposes businesses to cyber vulnerabilities like ransomware and phishing. Business owners must understand risks, hire cybersecurity experts, and implement consistent safeguards to prevent financial loss and disruptions. Strong security starts with awareness and proactive action.

Why Security Audits Are Essential for Protecting Financial Data
In Q4 2024, 35% of Americans faced data breaches affecting identity or accounts. Security audits are now essential for all organizations handling financial data, going beyond compliance with penetration testing and code audits. This guide covers audit essentials, risk management, and prevention strategies.
How to Avoid IP Bans When Using Proxies?
This guide explains why websites ban proxy IPs and shares key methods to avoid detection. Rotate proxies, add delays between requests, mimic human behavior, and opt for high-quality proxies to stay under the radar.

Protect Your Family’s Data with Safe Cargobike Choices
Cargobikes are popular for families but collect data via apps and sensors, raising privacy concerns alongside physical safety. This guide helps evaluate GDPR-compliant models, lighting features, and data management to protect your family on the road and online.

How to Choose the Best Neck Fan for Your Travel Needs
Picture this: you’re navigating a bustling airport, hauling luggage through crowded terminals, or exploring an open-air market under a blazing summer sun. Within minutes, you’re sweaty, uncomfortable, and wishing you had some way to cool down without stopping to fan yourself with a crumpled boarding pass. Overheating during travel is one of those universal frustrations...

How Businesses Use Lie Detection Methods To Prevent Fraud And Improve Security
Businesses employ lie detection techniques to identify fraud risks beyond traditional audits by analyzing physiological responses. Polygraph testing aids pre-employment screening for high-risk roles, revealing hidden deceptions. Compliance with laws like the EPPA ensures ethical application.

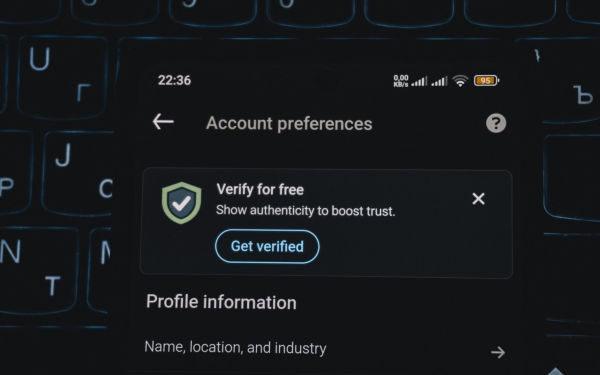
Practical Cybersecurity Strategies For RIAs Start With Control
Registered Investment Advisors can strengthen cybersecurity through access management and technical safeguards without massive budgets. Key practices include unique accounts, multi-factor authentication, and least-privilege access to reduce risks and ensure compliance. Focus on control for reliable, visible security aligned with regulations.

Business data protection guide for small businesses
This guide highlights key data protection risks for small businesses, including cyber attacks and lost devices. It emphasizes mapping data flows and adopting habits like password managers, multi-factor authentication, and regular software updates to safeguard operations.
4 Best Deepfake Detection Solutions for Enterprise Identity Verification in 2026
Deepfake attacks on identity verification are surging in 2026 with advanced AI tools enabling synthetic identities and impersonation. Legacy systems fail against these dynamic threats, but leading platforms offer robust detection for enterprises. Review the top 4 solutions for fraud prevention and KYC compliance.