VLAN trunking is a critical networking concept that allows multiple VLANs to traverse a single link between network devices, such as switches or routers. By enabling communication between devices in the same VLAN across different switches without requiring a router, trunking enhances network efficiency and scalability. For CCNA and CCNP students, understanding VLAN trunking is essential, as it’s a core topic in Cisco certification exams and a fundamental skill for managing enterprise networks.
This article explores VLAN trunking on Cisco switches, focusing on the IEEE 802.1Q standard, configuration steps, verification commands, and best practices. Whether you’re studying for your exams or configuring real-world networks, this guide provides practical insights to master VLAN trunking.
- Trunks that carry data from multiple local area networks (LANs) or virtual LANs (VLANs) across a single interconnect between switches or routers, called trunk ports.
- Trunks that combined multiple physical links to create a single higher-capacity, more reliable logical link, called port trunking.
As we mentioned above, a trunk is a point-to-point link between two network devices that carries data for more than one VLAN. A VLAN trunk extends VLANs to the whole network.
Understanding 802.1Q VLAN Trunking
Cisco switches support the IEEE 802.1Q standard for VLAN tagging, which adds a 4-byte tag to Ethernet frames to identify the VLAN they belong to as they traverse a trunk link. This enables multiple VLANs to share a single link between switches, routers, or devices with 802.1Q-capable NICs.
Key Points:
- Supported Interfaces: Trunk ports can be configured on Ethernet, Fast Ethernet, Gigabit Ethernet, or 10-Gigabit Ethernet interfaces.
- Trunking Modes: Cisco switches support trunk (static), dynamic auto, and dynamic desirable modes for trunk negotiation via Dynamic Trunking Protocol (DTP).
- Native VLAN: Untagged frames are sent over the native VLAN (default VLAN 1) unless configured otherwise.
Example: A trunk port on FastEthernet 0/24 carries tagged frames for VLANs 10 and 20, ensuring devices in the same VLAN on different switches can communicate.
Purpose of VLAN Trunks
A VLAN trunk is a point-to-point link between network devices (switches, routers, or servers with 802.1Q-capable NICs) that carries traffic for multiple VLANs. Unlike access ports, which belong to a single VLAN, trunk ports do not belong to a specific VLAN. Instead, they act as a conduit for VLAN traffic, enabling devices in the same VLAN on different switches to communicate without a router.
Key Features:
Trunks are essential for scaling VLANs across a network, supporting applications like IP telephony and server connectivity.
Trunks use 802.1Q tagging to differentiate VLAN traffic.
They can be configured to allow all VLANs or a subset for security.
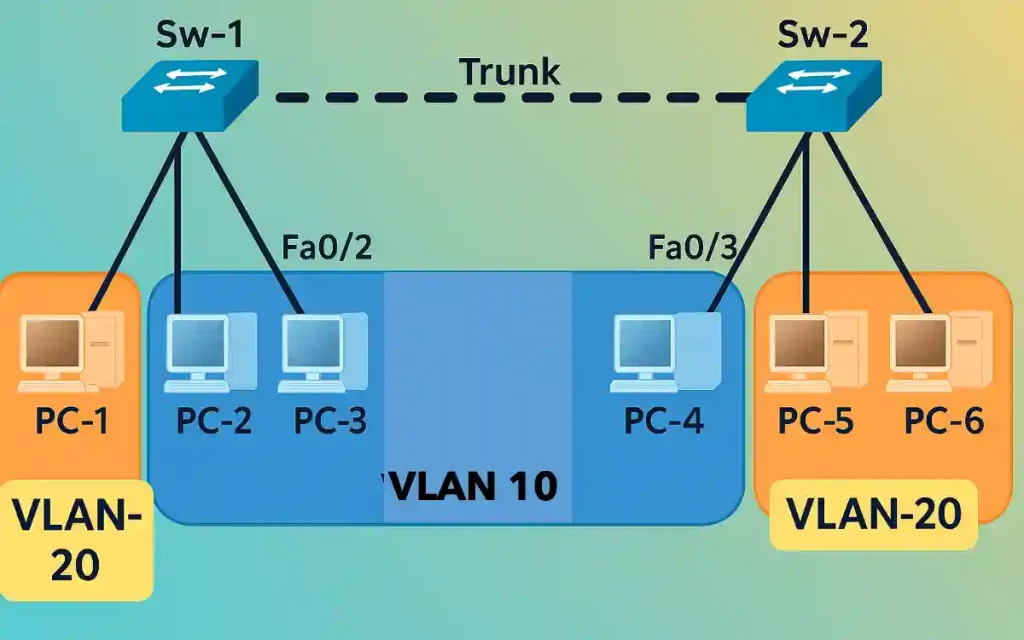
The topology consists of two Cisco switches (Sw-1 and Sw-2) connected via a trunk link to carry VLAN 10 (Sales) and VLAN 20 (Engineering) traffic:
Trunk Link: FastEthernet 0/24 on both switches, configured with 802.1Q encapsulation, allowing VLANs 10 and 20.
Sw-1: Ports Fa0/1 (VLAN 10, PC4), Fa0/2–Fa0/3 (VLAN 20, PC5 and PC6), and Fa0/24 (trunk to Sw-2).
Sw-2: Similar VLAN and port assignments, with Fa0/24 as the trunk port.
Configuring VLAN Trunking on Cisco Switches
Follow these steps to configure a trunk port between two Cisco switches (e.g., Sw-1 and Sw-2) to carry VLAN 10 (Sales) and VLAN 20 (Engineering) traffic.
Enter Interface Configuration Mode: Select the interface connecting the switches (e.g., FastEthernet 0/24).
Sw-1> enable
Sw-1# configure terminal
Sw-1(config)# interface fastEthernet 0/24Set the Port to Trunk Mode: Configure the interface as a trunk port using the IEEE 802.1Q encapsulation.
Sw-1(config-if)# switchport trunk allowed vlan 10,20
Sw-1(config-if)# exitRepeat on the Second Switch: Configure the corresponding interface on Sw-2 similarly.
Sw-2(config)# interface fastEthernet 0/24
Sw-2(config-if)# switchport mode trunk
Sw-2(config-if)# switchport trunk encapsulation dot1q
Sw-2(config-if)# switchport trunk allowed vlan 10,20
Sw-2(config-if)# exitSave the Configuration
Sw-1# write memory
Sw-2# write memoryVerify Trunk Configuration: Use the following command to confirm the trunk status and allowed VLANs:
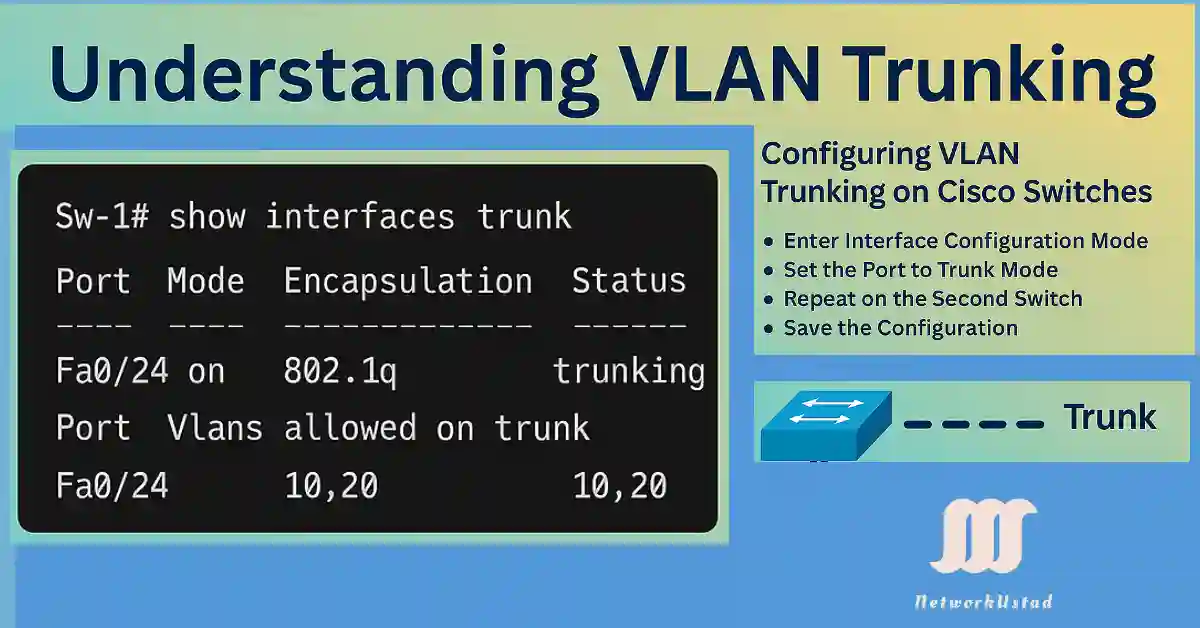
Sw-1# show interfaces trunk
Port Mode Encapsulation Status Native VLAN
Fa0/24 on 802.1q trunking 1
Port Vlans allowed on trunk
Fa0/24 10,20Troubleshooting VLAN Trunking Issues
Common VLAN trunking issues and their solutions include:
Trunk Not Forming
Cause: Mismatched trunk modes (e.g., one side is dynamic auto, the other is access).
Solution: Ensure both sides are set to switchport mode trunk or compatible dynamic modes. Verify with:
Sw-1# show interfaces trunk
VLAN Traffic Not Passing
Cause: VLANs may not be allowed on the trunk or not configured on both switches.
Solution: Check allowed VLANs with show interfaces trunk and ensure VLANs exist on both switches using show vlan brief. Add VLANs if needed:
Sw-1(config)# vlan 10
Sw-1(config-vlan)# name SALESEncapsulation Mismatch
Cause: One switch uses 802.1Q, while the other uses ISL (older Cisco standard).
Solution: Standardize on 802.1Q:
Sw-1(config-if)# switchport trunk encapsulation dot1qNative VLAN Mismatch
Cause: The native VLAN (default VLAN 1) differs between switches.
Solution: Set the same native VLAN on both sides:
Sw-1(config-if)# switchport trunk native vlan 1Use these commands to diagnose issues:
Sw-1# show interfaces trunk
Sw-1# show interfaces <interface-id> switchport
Sw-1# show vlan briefConclusion
Mastering VLAN trunking on Cisco switches enhances network efficiency and flexibility, enabling seamless traffic management across multiple VLANs. By following the outlined configuration steps and leveraging tools like the ‘show interfaces trunk’ command, you can optimize your network setup effectively. Embrace these techniques to build a robust and scalable network infrastructure.
FAQs
What is VLAN trunking and why is it important?
VLAN trunking allows multiple VLANs to be carried over a single link between switches, improving network efficiency and flexibility. It uses protocols like 802.1q to tag frames, ensuring proper traffic segregation and management across the network.
How do I configure VLAN trunking on a Cisco switch?
Enter interface configuration mode, set the port to trunk mode using the ‘switchport mode trunk’ command, and repeat on the second switch. Save the configuration to ensure the settings persist after a reboot.
What does the ‘show interfaces trunk’ command do?
The ‘show interfaces trunk’ command displays the trunking status of ports, including mode, encapsulation, and allowed VLANs. It helps verify the configuration, as shown with Fa0/24 allowing VLANs 10 and 20.
Can I allow specific VLANs on a trunk link?
Yes, you can specify which VLANs are allowed on a trunk link using the ‘switchport trunk allowed vlan’ command. This restricts traffic to only the designated VLANs, enhancing security and performance.
What is 802.1q encapsulation in VLAN trunking?
802.1q is a standard protocol that adds VLAN tags to Ethernet frames, enabling trunking between switches. It ensures that frames are correctly identified and routed to their respective VLANs.