Month: September 2019

Vishing, Smishing, Pharming, and Whaling in Cybersecurity: Definitions, Examples, and Prevention Tips
In the ever-evolving landscape of cybersecurity, social engineering attacks like vishing, smishing, pharming, and whaling continue to exploit human vulnerabilities alongside network weaknesses. According to the 2025 Verizon Data Breach Investigations Report, phishing variants account for over 30% of breaches, with vishing and smishing rising due to mobile and VoIP adoption. As a network engineer,...

What Is Phishing? A Comprehensive Guide for Cybersecurity Enthusiasts (Updated 2025)
As discussed in previous articles on network security, phishing remains a low-effort, high-reward tactic for cybercriminals. They send fake emails, text messages, or create authentic-looking websites to steal personal and financial data. This technique, also known as spoofing, involves forging email headers or IP addresses to mimic trusted sources, often evading basic network filters like...

Understanding Spyware, Adware, and Scareware: A Cybersecurity Guide for Enthusiasts
In the previous article, I discussed malware, including its types: viruses, worms, ransomware, Trojan horses, logic bombs, back doors, and rootkits. This article dives deeper into additional malware types—spyware, adware, and scareware—focusing on their mechanics, network implications, and real-world impacts. As a network engineer with years of experience in cybersecurity, I’ll emphasize how these threats...

Identifying Spam Mail: A Comprehensive Cybersecurity Guide for 2025
Email remains a universal service for billions worldwide, serving as one of the most popular communication tools. However, its widespread use comes with significant vulnerabilities, making it a prime target for cybercriminals. These unsolicited messages, commonly known as “junk mail” or spam, are predominantly sent by advertisers or malicious actors. Criminals exploit spam to distribute...
What is Malware and Malicious Software? (Updated 2025)
Updated: October 19, 2025—Includes latest threats and network defenses. Malware, or malicious software, is a program or file designed to disturb computer processes and operations or gain unauthorized entry to the computer system, often via network protocols like RDP or SMB, without the user’s knowledge or permission. Malware has become a common term for all...

Thwarting Cybercriminals: Master Key Measures and Strategies for Cybersecurity Enthusiasts in 2025
As a cybersecurity and networking expert with extensive experience in securing enterprise environments, I’ve seen firsthand how cybercriminals evolve their tactics. Thwarting cybercriminals isn’t easy, but companies, governments, and organizations are taking proactive steps to limit and discourage these threats. In this article, we’ll explore key actions and measures, updated for 2025, with practical insights...

Cyber Security Threats and Defenses: A Comprehensive Guide for 2025
Cyber security threats are a growing concern worldwide, escalating with AI and ransomware in 2025. Individuals and organizations rely on networks, making intrusions devastating. Computer networks are necessary for everyday activities, and both individuals and organizations depend on their computers and networks. Intrusion to these computers by an illegal person can result in a network...
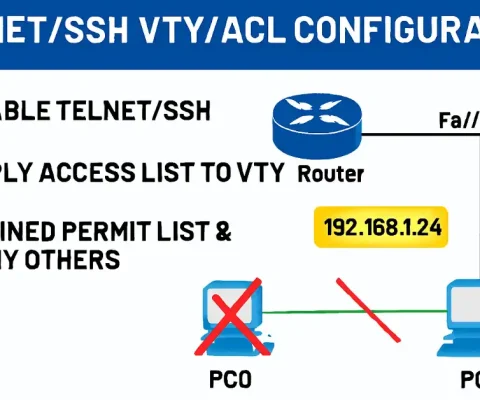
How to Configure Standard ACLs to Secure VTY Ports
All Cisco routers and switches do not allow remote access by default via terminal programs like PuTTY or Tera Term. Remote connectivity options include Telnet (VTY Port) or SSH. SSH provides encrypted sessions and is strongly recommended by Cisco for remote administration due to Telnet’s vulnerabilities. Prerequisites for CCNA/CCNP Students However, if your router’s Cisco...
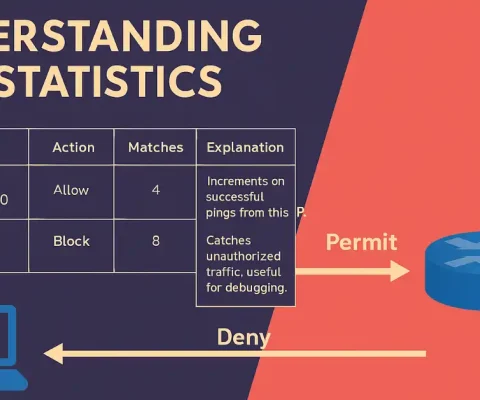
ACL Statistics in Cisco Networks: Monitoring Matches with show access-lists
Access Control Lists (ACLs) are essential for filtering traffic in Cisco networks. For CCNA students, understanding statistics helps verify if rules are working as intended. CCNP candidates should note how stats aid in troubleshooting complex setups like multi-interface ACLs. After an ACL has been configured and applied to an interface, it can block or permit...
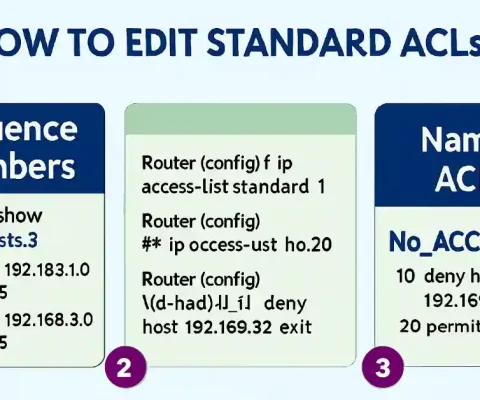
How to Edit Standard ACLs
Network administrators sometimes want to edit standard ACLs. As you know, each new entry you add to the Access Control List (ACL) appears at the bottom of the list, and the router assigns a sequence number to that entry automatically. Standard ACL statements are added to running-config files, but there is no built-in way to...