
Master Networking & Cybersecurity
Explore in-depth tutorials, latest industry trends, and expert insights to advance your IT career. Join thousands learning networking technologies.
7000+
Articles
1.2M+
Monthly Readers
100%
Free Content
Featured Article

AI-Driven Network Security 2026: Trends and Strategies
Discover how AI-driven network security detects threats 60% faster in 2026, with case studies, stats, and implementation steps for unbreakable defenses.
Trending Now
Latest industry trends and high-impact updates
 AI
AIHow Robotics and Secure Networking Are Feeding San Francisco’s Most Vulnerable
 Enterprise Technology
Enterprise TechnologyRed Hat extends open source technology into space
 Mobile Threat Defense
Mobile Threat DefenseZimperium Mobile App Response Agent helps security teams counter mobile attacks
 Cybersecurity
CybersecurityPoor security left hackers inside water company network for nearly two years
 Cybersecurity
CybersecurityGoogle researchers uncover criminal zero-day exploit likely built with AI
Browse Categories
Find content that matches your interests
Networking
Deep-dive guides for CCNA, routing, switching, and more

Network Architecture Essentials: Subnets, IP Whitelisting, and Managing Commercial IP Pools
This article explores how subnets, IP whitelisting, and commercial IP pools enable teams to build a controlled network layer for reliable web testing and data collection. It covers the importance of subnet separation, security policy simplification, and practical benefits for projects.

The Hidden Financial Benefits of Learning Networking Skills
Learning networking skills can lead to better job opportunities, higher earnings, and a more stable career in IT. Discover the hidden financial benefits.
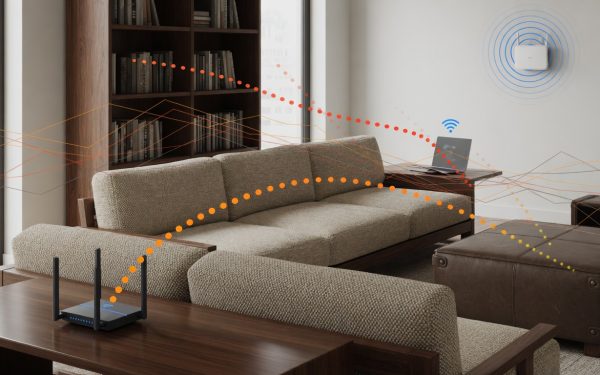
The Living Room Wi-Fi Trap: How Furniture Materials Break Your Signal
The living room is often the busiest wireless hub in modern homes, yet furniture materials frequently disrupt connectivity. This guide explains how wood, metal, and mirrors affect Wi-Fi bands and offers solutions for better signal strength.
Editors Picks
Hand-picked articles selected by our editorial team

Back Casting Room: Complete Guide to What It Is, How It Works, and Why It Matters in 2026
Whether you first heard this term in a business strategy meeting, a film production discussion, or an online forum, "back casting room" means something different depending on who is using it — and that confusion is exactly why most articles on this topic fail to actually help you. This guide cover

Node.js Outsourсing vs. In-House Team: What’s the Real Tradeoff?
Building a Node.js product involves choosing between outsourcing and an in-house team, each with unique benefits and challenges. In-house teams offer direct control and deep system knowledge but require lengthy recruitment. Outsourcing enables quick expertise access and speed but involves coordination with external partners.
What Stops AI Models From Working Reliably in Real Systems
AI models often excel in training but falter in production due to data drift, infrastructure dependencies, and versioning issues. This gap highlights the need for robust monitoring and MLOps practices. Teams can ensure reliability by addressing these real-world challenges effectively.
Latest Reviews
In-depth product & tech reviews from our editorial team
Latest News
Breaking tech news, security alerts, and industry updates

I use these 10 secret Netflix codes to find hidden movies – here's how to enter them
A Netflix user has detailed a method using 10 specific codes to access hidden movies on the platform,...

MuddyWater Deploys DLL Side-Loading in 9-Country Espionage Campaign
Iranian hackers MuddyWater target governments and critical sectors using DLL side-loading in a new cyberespionage campaign.

AI Chatbots Direct Users to Cryptojacking Malware Sites
AI chatbots are reportedly directing users to websites that install cryptojacking malware, exploiting retrieval-augmented generation systems. This leads...

JINX-0164 Malware Targets Crypto Firms via Fake Recruiters
A new macOS malware campaign, JINX-0164, is attacking cryptocurrency companies using fake recruiter lures. The operation distributes custom...

Threat Actors Exploit FortiClient EMS Flaw to Deploy Credential Stealer
Threat actors are exploiting a critical FortiClient EMS vulnerability to deploy credential-stealing malware, prompting urgent patching recommendations.

Kimsuky Expands Cyber Arsenal with HTTPSpy, HelloDoor, and VS Code Tunnels
North Korean hacking group Kimsuky deploys HTTPSpy, HelloDoor, and VS Code tunnels in latest campaign, targeting encrypted communications...
Job Opportunities
Browse verified job listings across tech, marketing, design and more
About the Role A newly discovered infostealer malware is targeting enterprise devices by exploiting a known…
Cybersecurity Research Role: Analyzing SSD Behavior Tracking Threats
About the Role This opportunity involves researching and analyzing a newly discovered cybersecurity threat where websites…

Cybersecurity Research: LinkedIn Phishing Abusing Adobe Platform
LinkedIn-Themed Phishing Campaign Exploits Adobe’s A/B Testing Platform A concerning cybersecurity threat has emerged targeting professionals…
About the Role Microsoft has recently redesigned its Microsoft 365 Copilot, an AI-powered assistant designed to…
About the Role Anthropic has recently launched Claude Opus 4.8 and announced plans to make its…
About the Role Claroty, a leader in cybersecurity solutions, has introduced Claroty Claire, an AI-powered security…











