
CCNA
Cisco Certified Network Associate certification resources
Master TCP 3-Way Handshake and Boost Your Skills (Updated 2025)
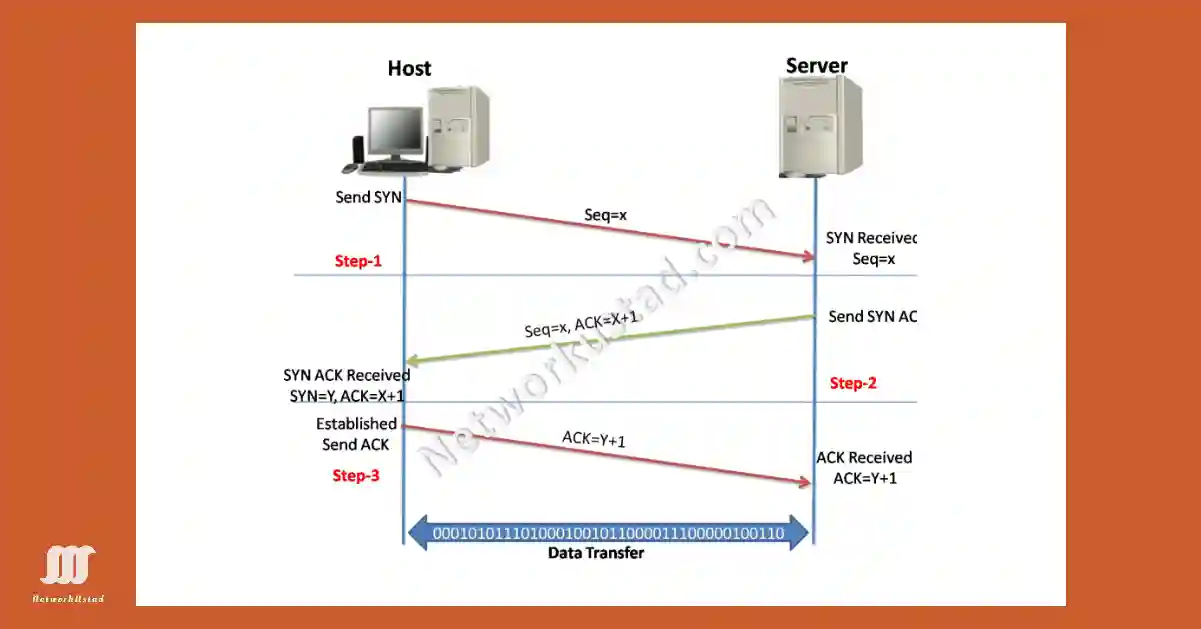
The TCP 3-way handshake is also known as the TCP handshake. It contains three message handshakes or SYN, SYN-ACK, and ACK. It is the method for TCP/IP connection over an IP-based network. TCP’s 3-way handshaking is often called the SYN, SYN-ACK, ACK technique because there are three messages transmitted by TCP to negotiate and start...
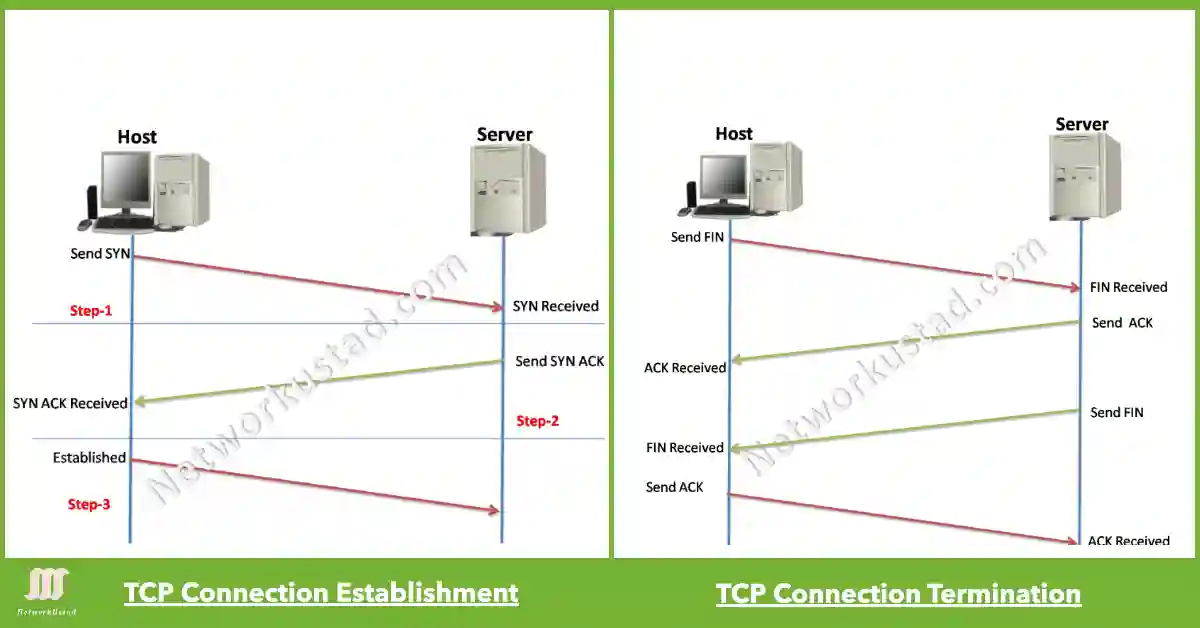
Master TCP Connection Establishment and Termination – Boost Your Skills (Updated 2025)
All application processes on the server use unique port numbers. The network administrator can use default ports (e.g., 80 for HTTP, 21 for FTP) or configure custom ports manually, ensuring no conflicts. An active server application requiring an open port on the server means the transport layer accepts and processes segments addressed to that port...

Netstat Command, Troubleshoot Connections in Seconds Exclusive 2025 Guide
Knowing which active TCP connections are open on a networked host is crucial, especially with the 2025 IoT growth. The netstat command is a vital tool for verifying these connections on Windows (e.g., 10/11) or Linux, addressing security risks from unexplained connections, a key concern as of 2025 This netstat command shows detailed information about...
TCP vs UDP Explained: Unlock the Secrets of Success 2025 Guide
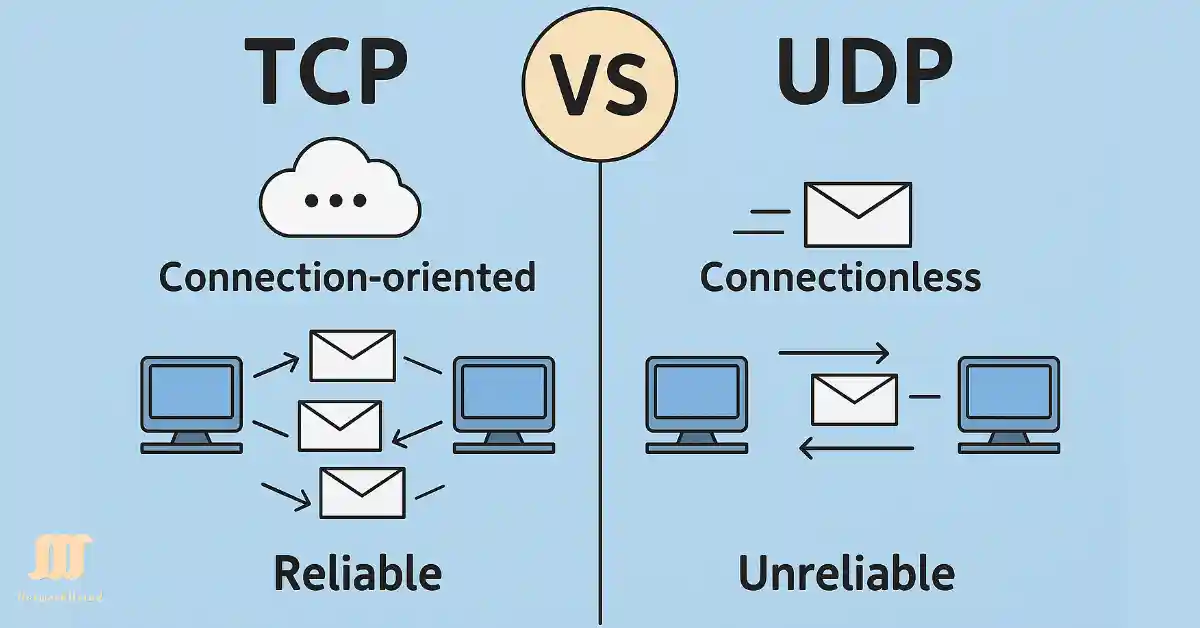
The TCP and UDP transport layer protocols handle data communications between terminals in an IP network, with TCP and UDP adapting to 2025’s IoT and 5G demands. The TCP is a connection-oriented protocol, and UDP is a connectionless protocol. TCP powers secure file transfers like banking uploads, while UDP drives live sports streaming, meeting 2025’s...
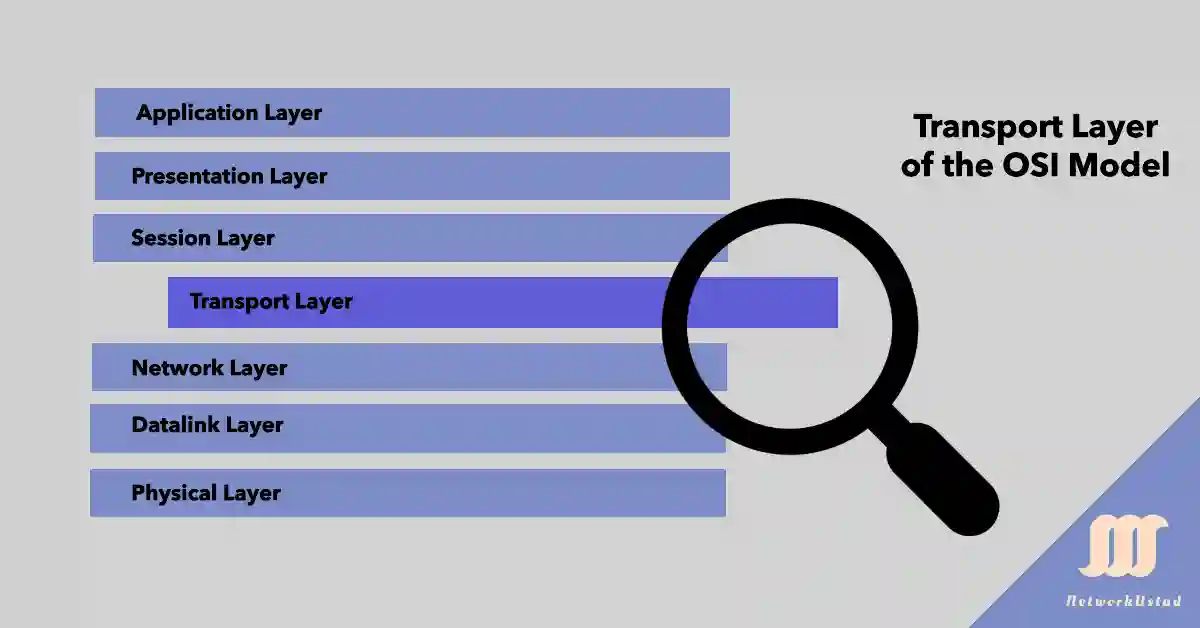
Transport Layer Unveiled: Boost Your OSI Model Knowledge With this Exclusive 2025 Guide
The transport layer supports real-time apps like video conferencing (UDP) and secure browsing (TCP with TLS), adapting to 2025’s cloud and IoT demands. For a web server (port 80) and email (port 25) on 192.168.1.10, the transport layer routes HTTP and SMTP data to the correct processes. TLS over TCP secures data for HTTPS, adding...
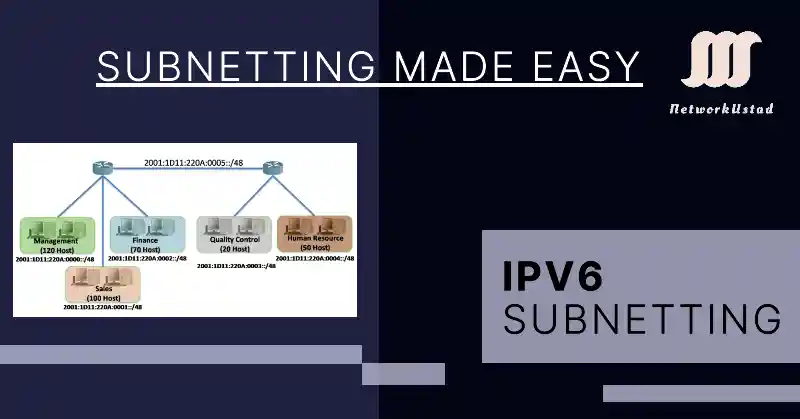
IPv6 Subnetting Simplified: Unlock the Power of Next-Gen Networking
The shift to IPv6 addresses the exhaustion of IPv4’s 32-bit space, with adoption accelerating in 2025 to support IoT and global connectivity, necessitating new subnetting strategies. IPv6 addresses are increasingly replacing IPv4 due to address exhaustion, with adoption surpassing 40% globally by 2025, driving new subnetting needs. We use CIDR, VLSM, and NAT to save...
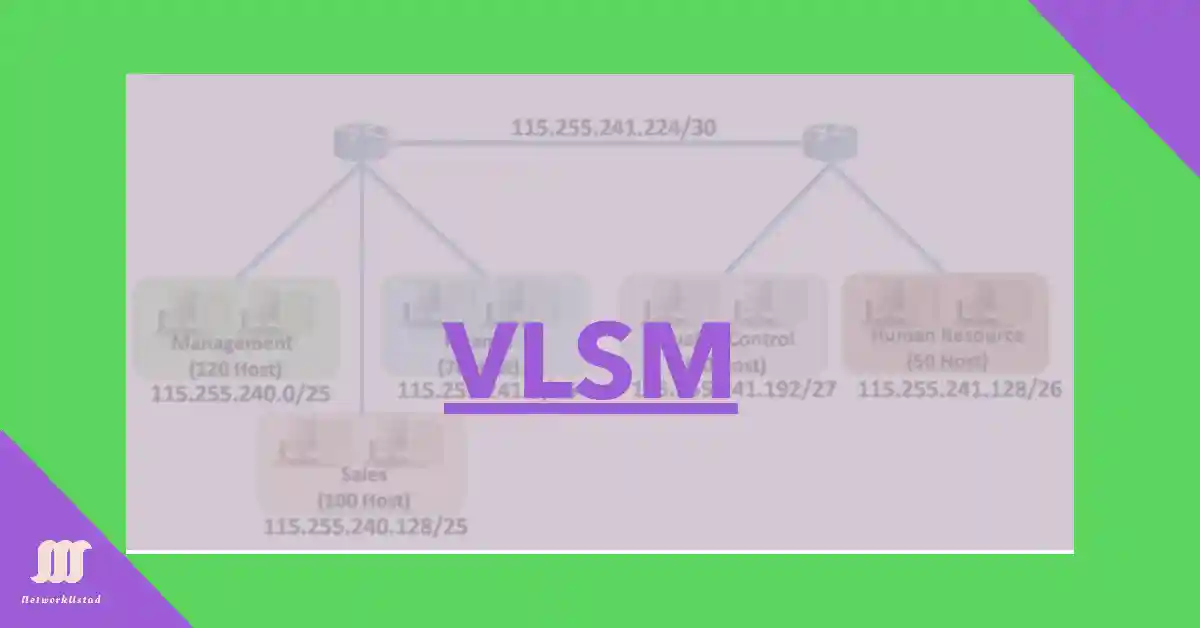
VLSM Insights: Avoid IP Waste with Precision Subnetting 2025 Guide
VLSM (Variable Length Subnet Masking) helps improve the use of IP address space, with applications in IPv6 internal segmentation as of June 2025. Using a variable-length subnet mask, we can assign LAN and WAN segments without wasting IP addresses. As shown in the scenario in the Figure below, the hosts in each subnetwork will be...
Master Subnetting Based on Network Requirement – Exclusive Guide 2025
Sometimes, the number of sub-networks is more critical than the number of host addresses per sub-network. For example, an organization wants to separate network traffic based on internal structure or department setup. In this case, subnetting based on network requirements is most important in determining how many bits to borrow. The addressing scheme must allow...
Master Subnetting Based on Host Requirements: Unleash Efficient Subnetting Success with Our 2025 Guide
Subnetting involves a trade-off: borrowing more host bits increases subnets but reduces hosts per subnet. For example, a /16 network with 16 host bits can be subnetted to /22 (64 subnets, 1022 hosts) or /28 (4096 subnets, 14 hosts), guiding network design as of June 2025. We consider either the host requirement or the network...
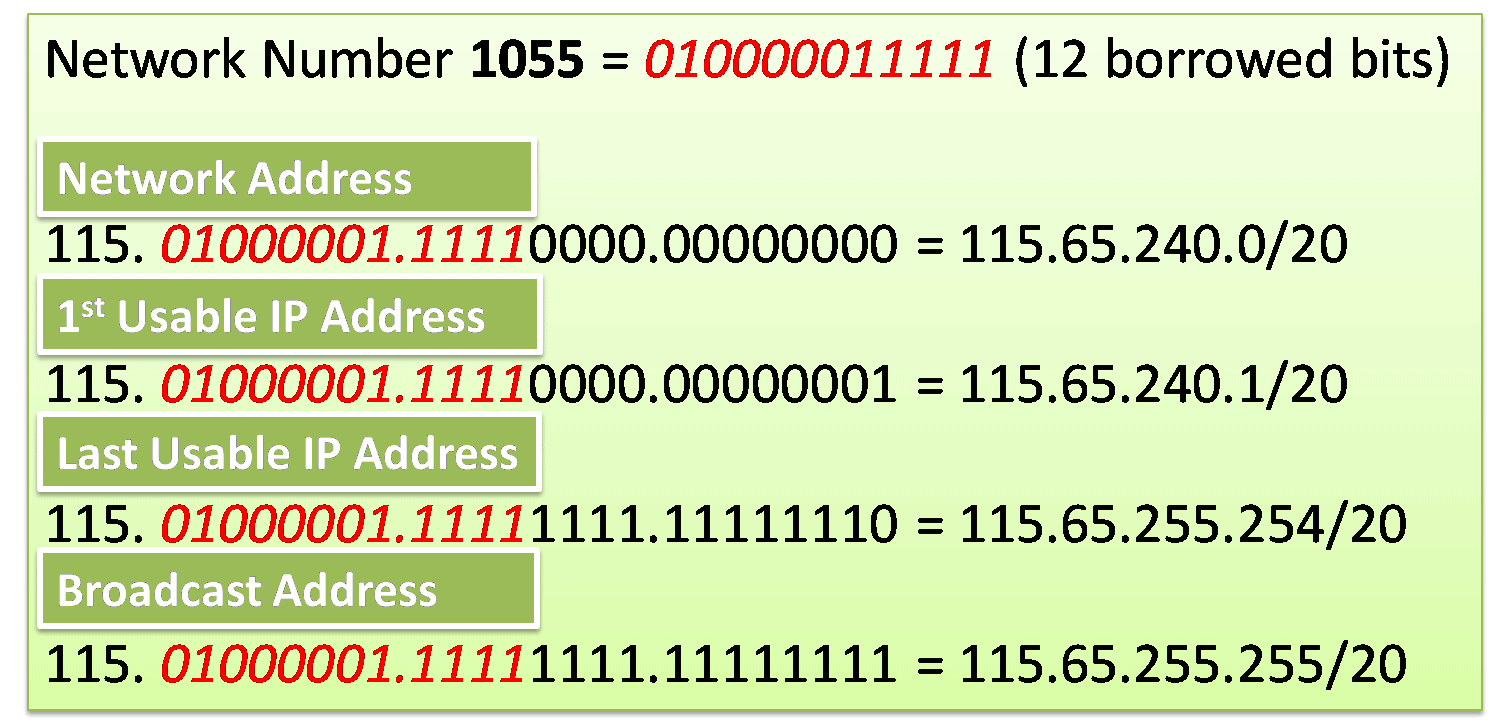
Creating 4000 Subnets from a /8 Prefix – Exclusive How to Guide
Some organizations need more subnets. For example, a small ISP requires 4000 subnets for its clients. Each client required abundant space in the host portion to create their subnets. The network address 115.0.0.0/8 has a default subnet mask of 255.0.0.0 or /8 prefix. The /8 prefix means that there are 24 host bits available to...