CCNA
Cisco Certified Network Associate certification resources

Mastering Host Address, Network Prefix, Network ID, and Broadcast ID in 2025
This article, “Mastering Prefix, Network ID, Broadcast ID, and Host Address” is the continuation of my previous articles about the IP address, which are the following: IP address Classes- Exclusive Explanation Positional Number System and Examples (Updated 2025) Network and Host Portion of IPv4 Address So, you need to study the above article to understand...
Master Network and Host Portion of IPv4: Ignite Your Networking Skills Today!
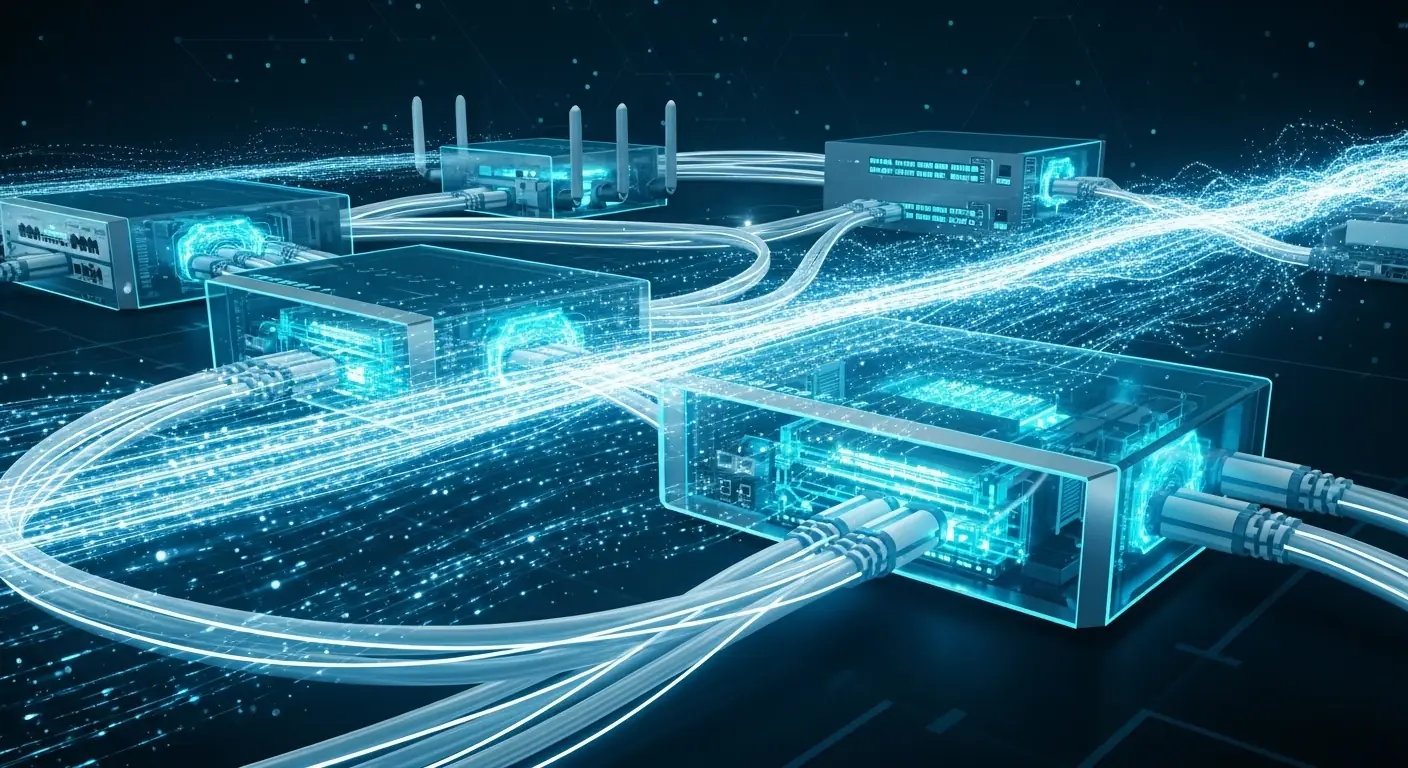
Each network requires a unique network number, and each host requires a unique IP address. The IPv4 address is a 32-bit number that uniquely identifies a network and host. In 2025, mastering IPv4 addressing is crucial for CCNA preparation and managing networks with 5G, IoT, and high-speed 100G/400G/800G interfaces, where efficient IP allocation remains vital....
Positional Number System and Examples (Updated 2025)
In a positional number system, each symbol represents a different value depending on the position it occupies in a number, and each system has a value that relates to the number directly next to it. The total value of a positional number is the total of the resultant value of all positions. The decimal number...
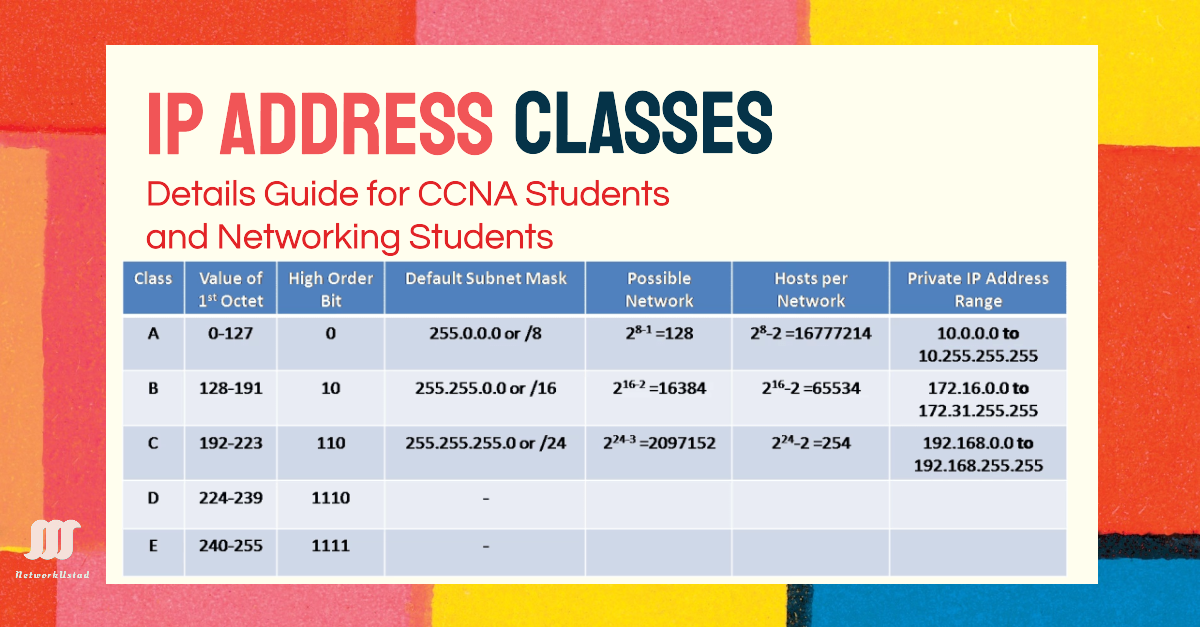
Mastering IPv4 Address Classes with Confidence: 2025 Guide
The IPv4 address is an identifying number for network devices. It is similar to a home or business address, which supplies that specific physical location with a particular address. Devices on a network are differentiated from one another through IPv4 addresses. In 2025, understanding IPv4 addressing is critical for CCNA preparation and managing networks with...

Cisco Router Interface Configuration: CLI Guide, IPv6 Setup & Troubleshooting (2025 Update)
Properly configuring Cisco router interfaces is critical for network performance, security, and scalability. Whether you’re setting up an essential LAN connection or advanced IPv6 routing, this guide covers CLI commands, real-world labs, and troubleshooting tips updated for Cisco IOS XE 2024. We can categorize Cisco Interfaces Physical Interfaces: GigabitEthernet, Serial, FastEthernet, etc. Logical Interfaces: Loopback,...

Mastering Basic Cisco Router Configuration: 2025 Guide
Different IP networks cannot communicate with each other without a router. Routers successfully do this job by sending packets from one IP network to another using routing. Before using the router, some basic configuration is required. This article covers the Basic Cisco Router Configuration Guide. We will use Cisco Packet Tracer for simulation and configuration....
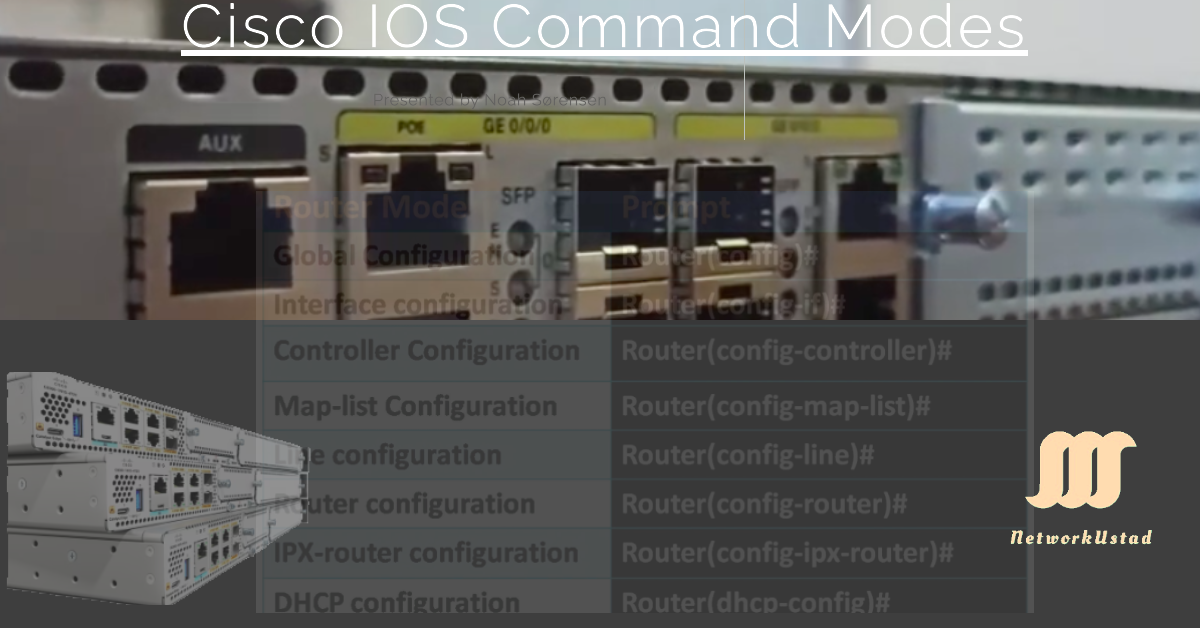
Cisco IOS Command Modes Explained: User EXEC, Privileged EXEC, and Global Configuration Modes (2024 Guide)
Introduction – Cisco IOS Command Modes Cisco IOS devices use hierarchical command modes to control access and prevent accidental misconfigurations. Whether you’re managing a router, switch, or preparing for the CCNA exam, understanding these modes is critical: In addition, the Global configuration mode contains sub-configuration Modes. The figure below illustrates the Cisco IOS sub-configuration modes,...
Cisco Router Interfaces: The Ultimate 2025 Guide for CCNA Students
Routers are the backbone of modern networks, and understanding their interfaces is the first step toward mastering network configuration. Whether preparing for the CCNA exam or managing enterprise infrastructure, this 2025 guide covers everything from legacy Ethernet ports to cutting-edge SD-WAN interfaces. In 2025, router interfaces are evolving with AI-driven traffic management and 5G backhaul, making this...
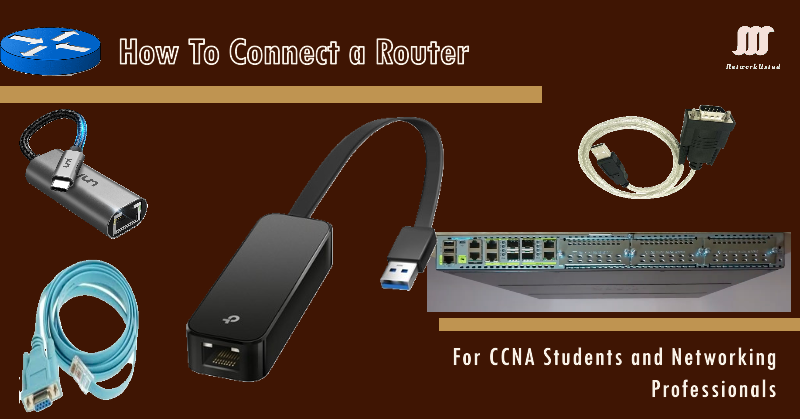
How to Connect and Access a Cisco Router: The Ultimate 2025 Guide for CCNA Students
Connecting to a Cisco router is the first step toward mastering network configuration, a critical skill for CCNA students and aspiring network engineers. Understanding physical console access and remote SSH management is essential, whether setting up a home lab or troubleshooting enterprise networks. In 2025, mastering Cisco router connections is vital for CCNA certification and...
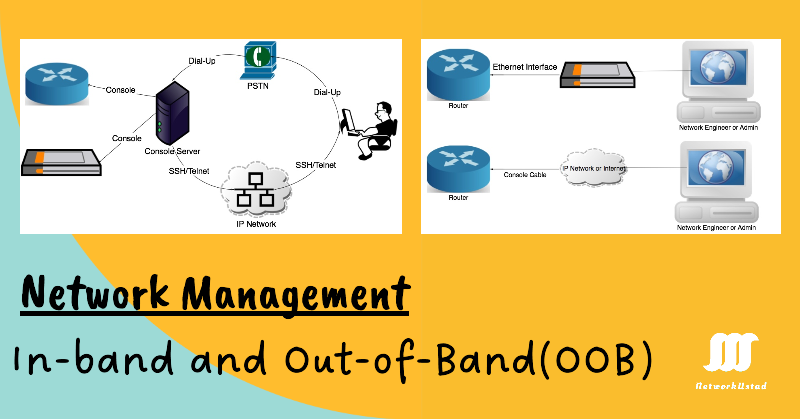
In-Band and Out-of-Band Network Management: A Complete Guide for Beginners
Network Management is critical for businesses, IT teams, and even CCNA students learning the ropes. Two fundamental approaches—in-band and out-of-band (OOB) management—determine how administrators monitor, configure, and troubleshoot devices. This guide’ll break down these concepts, compare their pros and cons, and explore real-world use cases. By the end, you’ll understand when to use each method and how modern...