Cybersecurity
Welcome to NetworkUstad’s Cybersecurity Hub – your comprehensive resource for staying secure in an increasingly connected world. In today’s digital landscape, cyber threats evolve faster than ever. From sophisticated ransomware attacks to simple phishing scams, businesses and individuals face constant risks. Our cybersecurity section delivers practical, actionable insights to help you build robust defenses and protect what matters most. Whether you’re a security professional, IT administrator, business owner, or someone concerned about digital privacy, you’ll find expert guidance covering everything from fundamental security principles to advanced threat protection strategies. What You’ll Discover: 🔐 Security Fundamentals – Master the CIA Triad, understand information security basics, and build a strong foundation in cybersecurity principles. 🛡️ Threat Intelligence – Learn about different attack vectors, hacker types, malware categories, and emerging cyber threats targeting organizations worldwide. 🔒 Protection Strategies – Explore practical defense mechanisms including encryption, multi-factor authentication, network security, endpoint protection, and access controls. 📊 Compliance & Governance – Navigate regulatory requirements like GDPR, HIPAA, PCI DSS, and industry frameworks such as NIST and ISO 27001. ⚡ Incident Response – Prepare for the inevitable with comprehensive guides on breach detection, containment, recovery, and forensic analysis. 🚀 Emerging Technologies – Stay ahead with insights on AI security, cloud protection, IoT vulnerabilities, blockchain security, and quantum computing threats. 💼 Enterprise Security – Discover strategies for securing hybrid workforces, protecting corporate data, managing third-party risks, and building security-aware cultures. 🎓 Career Development – Explore ethical hacking careers, certification paths (CEH, CISSP, OSCP), and skill development resources. Our articles combine technical depth with practical applicability. We break down complex security concepts into digestible insights, provide real-world examples, and offer step-by-step implementation guides. No unnecessary jargon—just clear, actionable cybersecurity knowledge you can use immediately. From understanding basic threats to implementing enterprise-grade security architectures, NetworkUstad’s cybersecurity content empowers you to make informed decisions and take meaningful action. We cover the full spectrum: network security, application security, data protection, cloud security, mobile security, and everything in between. Security isn’t a one-time project—it’s an ongoing journey. Join thousands of readers who trust NetworkUstad to keep them informed about the latest threats, best practices, and innovative solutions in cybersecurity. Protect your network. Secure your future. Start exploring our cybersecurity resources today.

Keep your Business safe from Cyber threats transmitted through email.
As a business owner, protecting your company from cyber threats transmitted through email is essential. Phishing assaults, malware, and ransomware are hazards that can jeopardize your company’s sensitive data, disrupt operations, and harm your reputation. You may dramatically lower the chance of a successful cyber-attack via email by adopting robust email security measures, teaching staff...

Android cleaners app for better performance of android devices
Android devices are some of the most popular and widely used gadgets today. But, just like your computer, they accumulate junk in fragmented files and other unnecessary data over time. This can slow down their performance and cause them to become sluggish. An Android cleaner app can help improve your device’s performance by removing these...

Here’s what you should look out for while selecting a data privacy suite.
Data privacy software is all the rage nowadays, and rightly so! As stricter and stricter data privacy laws and regulations are being implemented worldwide, it has become much more critical for businesses to comply with these regulations to carry out their operations effectively and efficiently. Now, it must be pointed out that several different data...
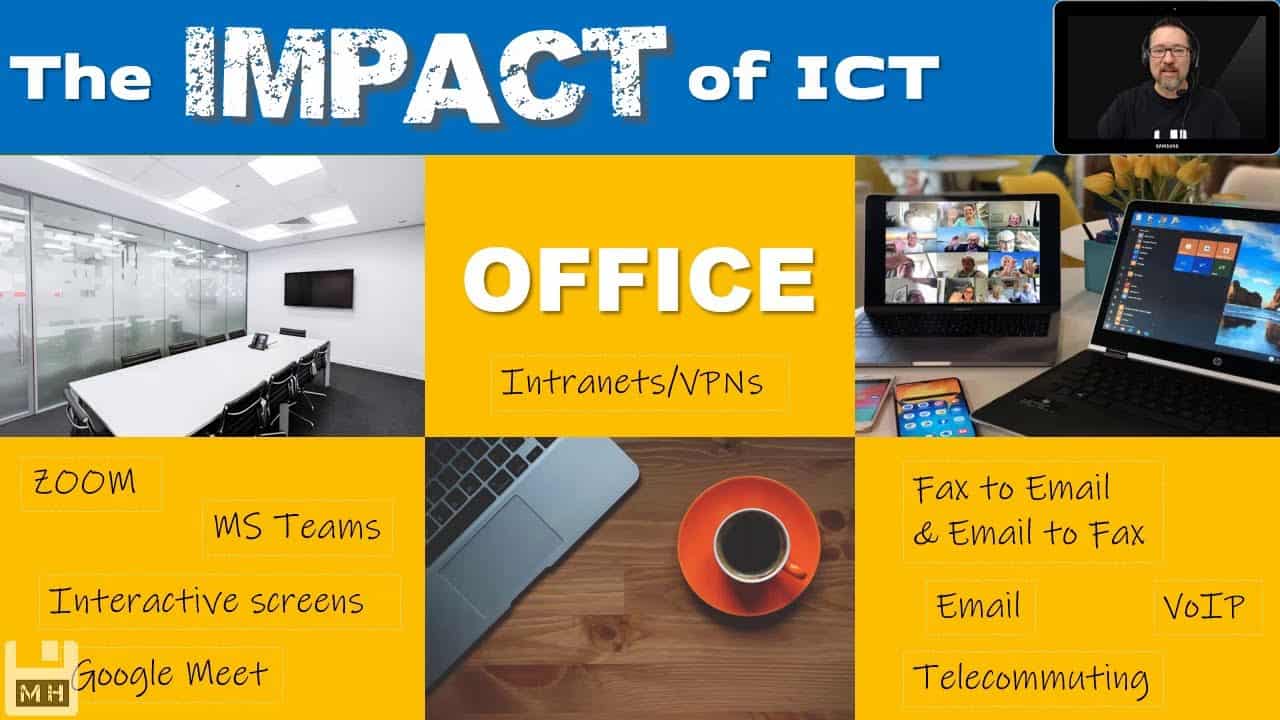
Top services provided by Impact ICT in Perth
Introduction Impact ICT is a leading IT services provider in Perth, Australia. Whether you’re looking for managed services or cloud solutions, Cyber Security providers in Perth can help you find the right technology solution to meet your needs. From remote working to cybersecurity and more, Impact ICT offers a wide range of services to help...

What Is Palo alto networks: Everything You Need to Know
Introduction to Palo Alto Networks Palo Alto Networks is a company that provides a platform for security and networking. The company was founded in 2005, and its headquarters are in Santa Clara, California. Palo Alto Networks has been profitable since 2012. In 2013, the company went public on the New York Stock Exchange. Palo Alto...

What is application security? Everything you need to know
Application security is the practice of protecting apps from unauthorized access and data breaches. It includes securing the app from external threats and safeguarding the data stored within it. Application security is important for businesses of all sizes. A data breach can result in lost customers, decreased revenue, and damage your reputation. There are many...
Several great reasons for the purchase of a PHP code security scanner
You are looking forward to the upcoming weekend, sat in the office proud of the business that you oversee. You are a people’s person who is happy to leave specialised departments to the right people, being of the belief that it’s always best to leave things you are not totally proficient at to the experts....

PCI Compliance: Everything You Need to Know
You may have heard the term “PCI compliance” bandied about, but what does it mean? PCI compliance is a set of regulations for any business that processes, stores, or transmits credit card information. If your business falls into any of these categories, it’s important to understand the PCI compliance process and what is required of...

The Top 10 Cybersecurity Tips and Tricks For Small Businesses
Cybersecurity is one of the biggest concerns for many small businesses today. While there’s no foolproof way of defending your business from possible cyberattacks, there are plenty of ways and measures you can take to strengthen your defence – whether it’s XDR or even an SIEM alternative. Below are 10 best ways to protect your...

Web Intelligence Is Crucial To Your Business. Learn Why!
At a time when the competition is getting tougher and the proliferation of e-commerce websites is increasing, it’s necessary to have strategies in place to help your company stay afloat. One such strategy could be building a website that will keep your customers coming back for more. The one major advantage you’ll have with this...